Github Vulnerabilities Parallel Research

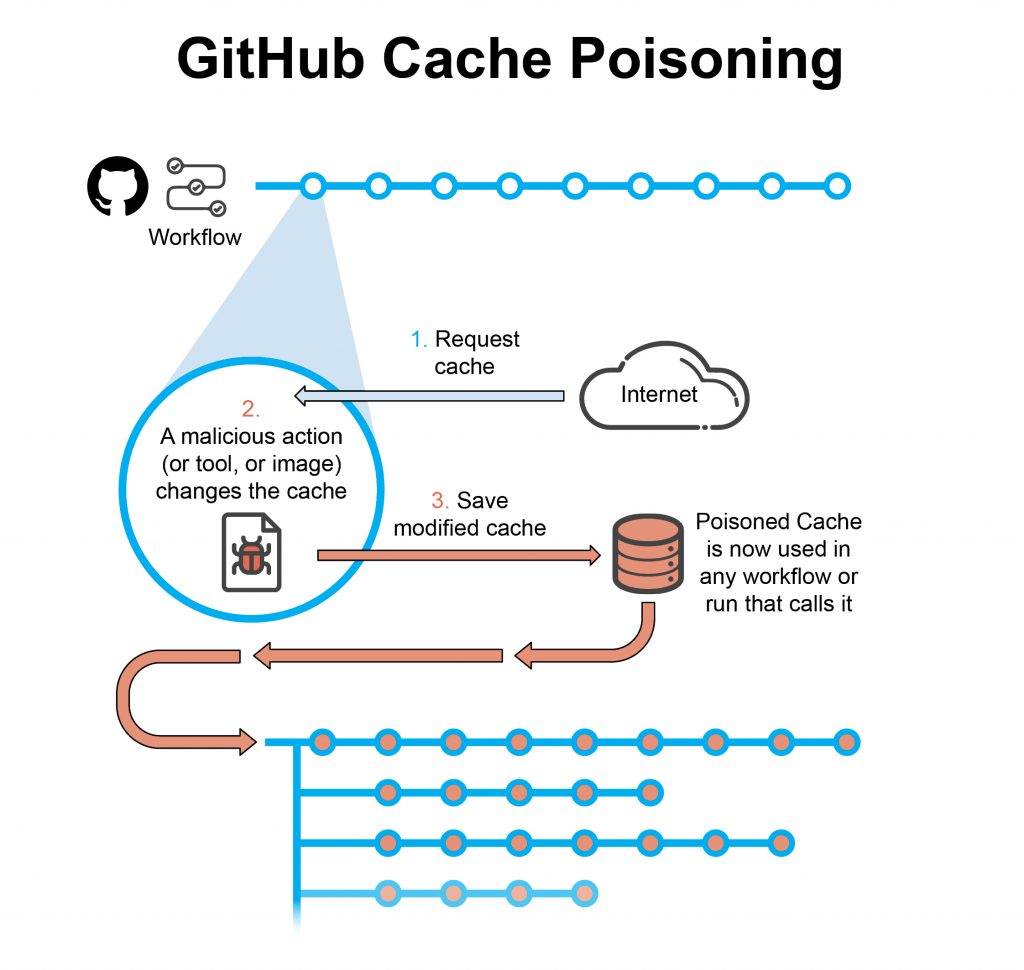
Github Vulnerabilities Parallel Research It didn’t take me long to realize that the github cross workflow artifact poisoning vulnerability discussed in the article bore a striking resemblance to the github cross workflow cache poisoning vulnerability we reported on in march 2022. Get the latest updates from the github security lab into vulnerabilities that are impacting the broader developer community.
Github Vulnerabilities Parallel Research Stanford and dryrun security research shows 87% of github copilot pull requests introduce vulnerabilities. tagged with security, github, ai, programming. Abstract and figures this paper presents a comprehensive empirical analysis of security vulnerabilities in ai generated code across public github repositories. Security vulnerability database inclusive of cves and github originated security advisories from the world of open source software. github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects. You are a cybersecurity assistant tasked with identifying potential vulnerabilities by analyzing github issues. your goal is to review each issue and determine whether it indicates a security vulnerability.

Github Vulnerabilities Parallel Research Scribe Security E2e Security vulnerability database inclusive of cves and github originated security advisories from the world of open source software. github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects. You are a cybersecurity assistant tasked with identifying potential vulnerabilities by analyzing github issues. your goal is to review each issue and determine whether it indicates a security vulnerability. Explore the latest vulnerabilities and security issues of github in the cve database. A study titled “eradicating the unseen” reveals the widespread presence of a critical path traversal vulnerability (cwe 22) across open source projects hosted on github. Security researchers have highlighted several vulnerabilities and malicious activities on github, a key platform for modern software development. I built an ai powered github vulnerability scanner that is easy to use, and simply outputs discovered vulnerabilities, the impact of the vulnerability, and recommendations on how to.
 (1).webp)
Github Copilot And Visual Studio Vulnerabilities Allow Attackers To Explore the latest vulnerabilities and security issues of github in the cve database. A study titled “eradicating the unseen” reveals the widespread presence of a critical path traversal vulnerability (cwe 22) across open source projects hosted on github. Security researchers have highlighted several vulnerabilities and malicious activities on github, a key platform for modern software development. I built an ai powered github vulnerability scanner that is easy to use, and simply outputs discovered vulnerabilities, the impact of the vulnerability, and recommendations on how to.
The Latest On Vulnerability Research The Github Blog Security researchers have highlighted several vulnerabilities and malicious activities on github, a key platform for modern software development. I built an ai powered github vulnerability scanner that is easy to use, and simply outputs discovered vulnerabilities, the impact of the vulnerability, and recommendations on how to.
Comments are closed.