Github Recon For Bug Hunters Ethical Hacking
Github Hafeezabhanu9 Ethical Hacking Project We've meticulously crafted this methodology to elevate the hacking prowess of security researchers. it provides a glimpse into how bheh's red team conducts bug bounty missions. Recon is the backbone of bug bounty hunting. to speed up the process and avoid repeating manual steps, i built a clean automation pipeline that performs all core recon tasks in one go —.
Automation Of Recon Process For Ethical Hackers Pdf An up to date, field tested github recon checklist, including tools, techniques, and best practices. Fetchmeurls is a powerful recon tool written by chris ‘saintdrug’ abou chabké from black hat ethical hacking, designed for bug bounty hunters to quickly fetch urls for multiple domains as part of a small or large scope actively and passively. 🚨 complete github recon guide for bug bounty & ethical hacking | hunter x in this video, you’ll learn how to perform professional github reconnaissance using real world tools and. Bug hunters waste a huge amount of time on recon across hundreds of programs. that’s why we built autorecon in bugtraceai — now public. filter by platform & program and instantly explore automated recon findings. less recon. more hacking. 🔗 recon.bugtraceai #bugbounty #cybersecurity #recon #infosec #ethicalhacking.
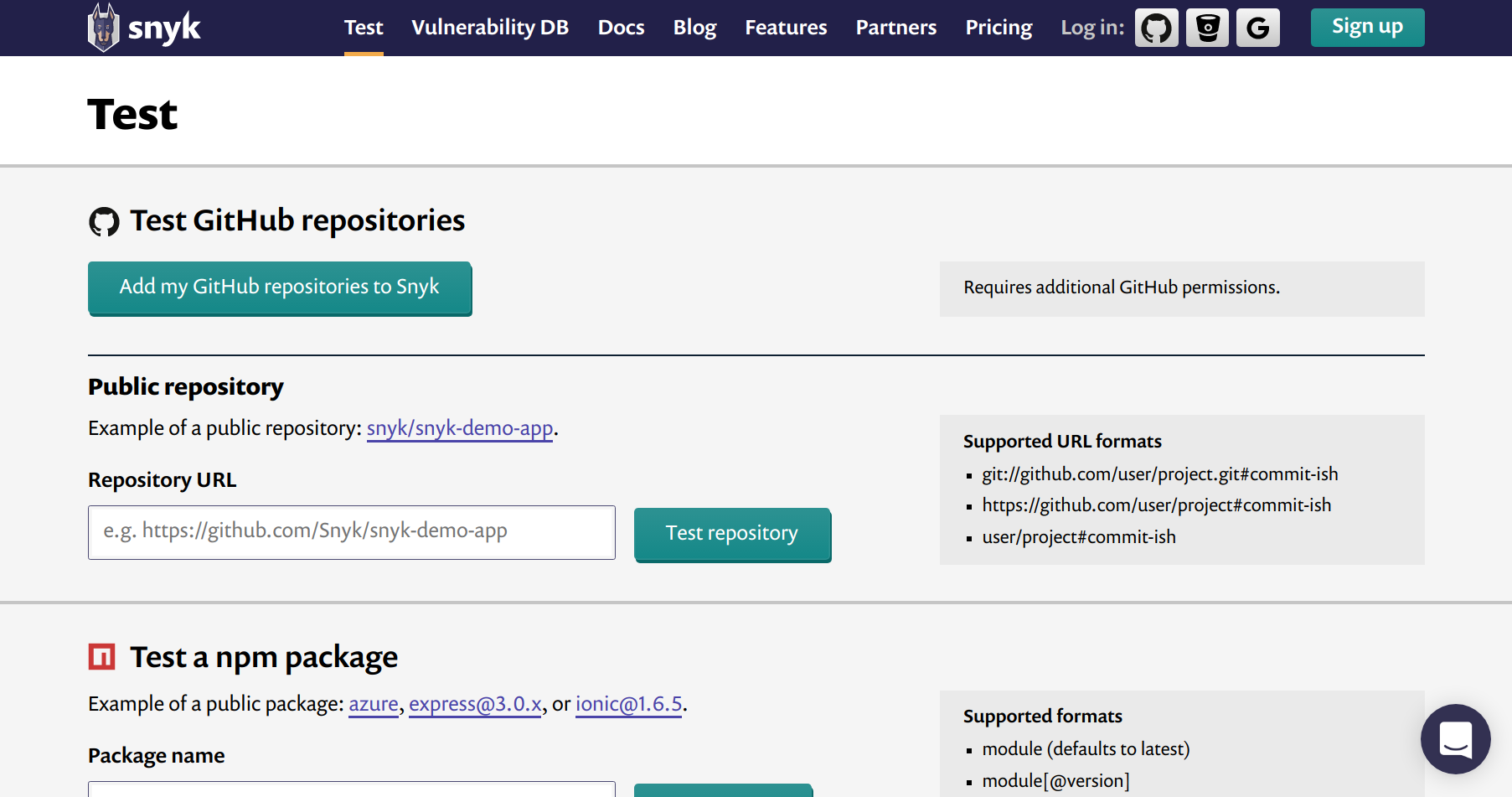
Github Plasmasecurity Bug Bounty Recon Automation This Python Script 🚨 complete github recon guide for bug bounty & ethical hacking | hunter x in this video, you’ll learn how to perform professional github reconnaissance using real world tools and. Bug hunters waste a huge amount of time on recon across hundreds of programs. that’s why we built autorecon in bugtraceai — now public. filter by platform & program and instantly explore automated recon findings. less recon. more hacking. 🔗 recon.bugtraceai #bugbounty #cybersecurity #recon #infosec #ethicalhacking. Developers often unknowingly push sensitive data into public repositories, giving ethical hackers a powerful vector to uncover secrets, tokens, credentials and much more. in this article, i’ll walk you through manual and automated techniques to extract valuable data from github. Whether you're a bug bounty hunter, ethical hacker, or a cybersecurity student, you'll learn how to use api keys, manage workspaces, explore the module marketplace, and perform passive and active recon with recon ng. This course is fully made for website reconnaissance for bug bounty hunters, penetration testers & ethical hackers. this is a intermediate level course all the topics are discussed here regarding recon on websites. This live and interactive training is designed to help you perform passive and active reconnaissance in ethical hacking and bug bounty hunting engagements. you will learn intermediate to advanced recon methodologies using open source intelligence (osint).
Github Ashutoshshah1 Ethical Hacking Roadmap This Is A Resource Developers often unknowingly push sensitive data into public repositories, giving ethical hackers a powerful vector to uncover secrets, tokens, credentials and much more. in this article, i’ll walk you through manual and automated techniques to extract valuable data from github. Whether you're a bug bounty hunter, ethical hacker, or a cybersecurity student, you'll learn how to use api keys, manage workspaces, explore the module marketplace, and perform passive and active recon with recon ng. This course is fully made for website reconnaissance for bug bounty hunters, penetration testers & ethical hackers. this is a intermediate level course all the topics are discussed here regarding recon on websites. This live and interactive training is designed to help you perform passive and active reconnaissance in ethical hacking and bug bounty hunting engagements. you will learn intermediate to advanced recon methodologies using open source intelligence (osint).
Github For Bug Bounty Hunters Cybernoz Cybersecurity News This course is fully made for website reconnaissance for bug bounty hunters, penetration testers & ethical hackers. this is a intermediate level course all the topics are discussed here regarding recon on websites. This live and interactive training is designed to help you perform passive and active reconnaissance in ethical hacking and bug bounty hunting engagements. you will learn intermediate to advanced recon methodologies using open source intelligence (osint).

Github Attacker Codeninja Reconx An Automated Recon Tool For Bug
Comments are closed.