Github Nathanielhawron Seedbruteforcer Program Built To Brute Force
Github Kvawenka Bruteforce Sha256 And Md5 Program built to brute force a seed given feateures from the resulting map. meant for minecraft:java edition, but can theoretically work for any similar application. Program built to brute force a seed given feateures from the resulting map. meant for minecraft:java edition, but can theoretically work for any similar application.
Bruteforce Github Topics Github Program built to brute force a seed given feateures from the resulting map. meant for minecraft:java edition, but can theoretically work for any similar application. Program built to brute force a seed given feateures from the resulting map. meant for minecraft:java edition, but can theoretically work for any similar application. I can connect with my mdi and mdi2 devices using their original software, but your program doesn't recognize the device as shown in the image. it detected the device once recently, but it didn't read the vin code and couldn't perform the scan. Using such extensive brute force methods can be very resource intensive, especially for longer passwords, as the number of combinations increases exponentially with the length of the password.
Github Snflo Bruteforce Code Used For Processing And Analysing Large I can connect with my mdi and mdi2 devices using their original software, but your program doesn't recognize the device as shown in the image. it detected the device once recently, but it didn't read the vin code and couldn't perform the scan. Using such extensive brute force methods can be very resource intensive, especially for longer passwords, as the number of combinations increases exponentially with the length of the password. Which are the best open source bruteforce projects? this list will help you: safeline, routersploit, thc hydra, allhackingtools, nettacker, instagram , and android pin bruteforce. Cmseek is best known for scanning content management systems and brute forcing them using its pre built or custom made brute forcing modules. it can detect around 180 different cms platforms and comes with advanced scanning capabilities for popular cms, including wordpress, drupal, and joomla. Short answer, that software is a total scam. and is stealing your information, while also using your system to mine bitcoin for him, instead of you. the code lies, telling you that it found wallets using word combinations. but everything is just built into the code to fool you. The answer is 12! = 479,001,600 possible mnemonics (less if there are repeated words). out of these only ~29,937,600 (1 in 16) produce a valid seed. this is definitely brute forceable. no, if you want to do this use a longer mnemonic (and make sure you permute them in a truly random way).
Github Ronreiter Bruteforce Seed Which are the best open source bruteforce projects? this list will help you: safeline, routersploit, thc hydra, allhackingtools, nettacker, instagram , and android pin bruteforce. Cmseek is best known for scanning content management systems and brute forcing them using its pre built or custom made brute forcing modules. it can detect around 180 different cms platforms and comes with advanced scanning capabilities for popular cms, including wordpress, drupal, and joomla. Short answer, that software is a total scam. and is stealing your information, while also using your system to mine bitcoin for him, instead of you. the code lies, telling you that it found wallets using word combinations. but everything is just built into the code to fool you. The answer is 12! = 479,001,600 possible mnemonics (less if there are repeated words). out of these only ~29,937,600 (1 in 16) produce a valid seed. this is definitely brute forceable. no, if you want to do this use a longer mnemonic (and make sure you permute them in a truly random way).
Brute Force Github Topics Github Short answer, that software is a total scam. and is stealing your information, while also using your system to mine bitcoin for him, instead of you. the code lies, telling you that it found wallets using word combinations. but everything is just built into the code to fool you. The answer is 12! = 479,001,600 possible mnemonics (less if there are repeated words). out of these only ~29,937,600 (1 in 16) produce a valid seed. this is definitely brute forceable. no, if you want to do this use a longer mnemonic (and make sure you permute them in a truly random way).
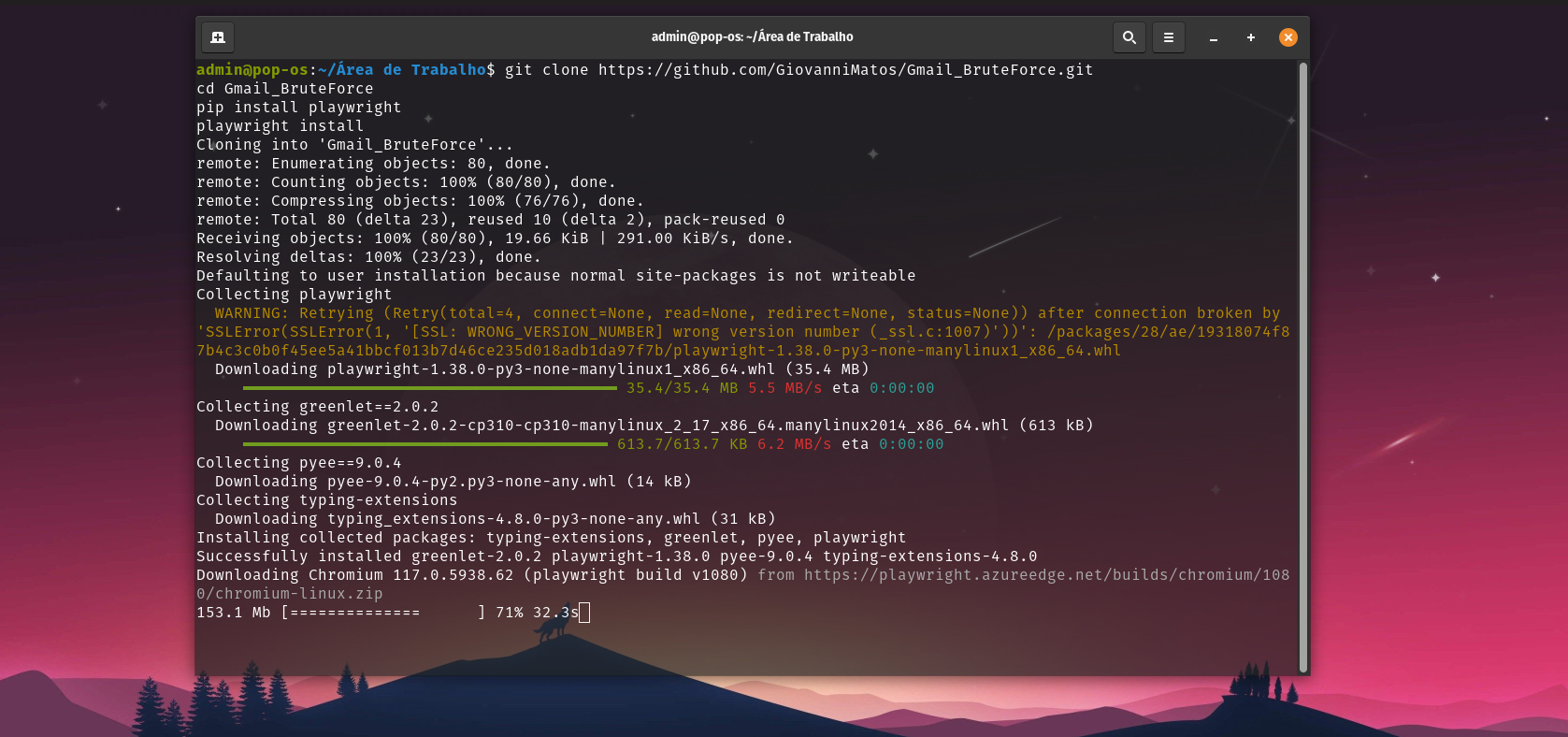
Github Giovannimatos Bruteforce рџ рџ Este Cгіdigo г гєtil Para Simular
Comments are closed.