Github Kolarajlakshmi Malware Detection
Github Kolarajlakshmi Malware Detection Contribute to kolarajlakshmi malware detection development by creating an account on github. In april 2026, north korean state sponsored hackers targeted south korean organizations using github as command and control infrastructure in multi stage attacks.
Github Pokemon12332112 Malware Detection Dprk linked actors use github c2 and lnk phishing in south korea, enabling persistent powershell control and data exfiltration. A series of malicious lnk files targeting users in south korea has been detected using a multi stage attack chain that uses github as command and control (c2) infrastructure. the campaign relies on scripting, encoded payloads and legitimate windows tools to maintain persistence while avoiding detection. Contribute to kolarajlakshmi malware detection development by creating an account on github. Contribute to kolarajlakshmi malware detection development by creating an account on github.

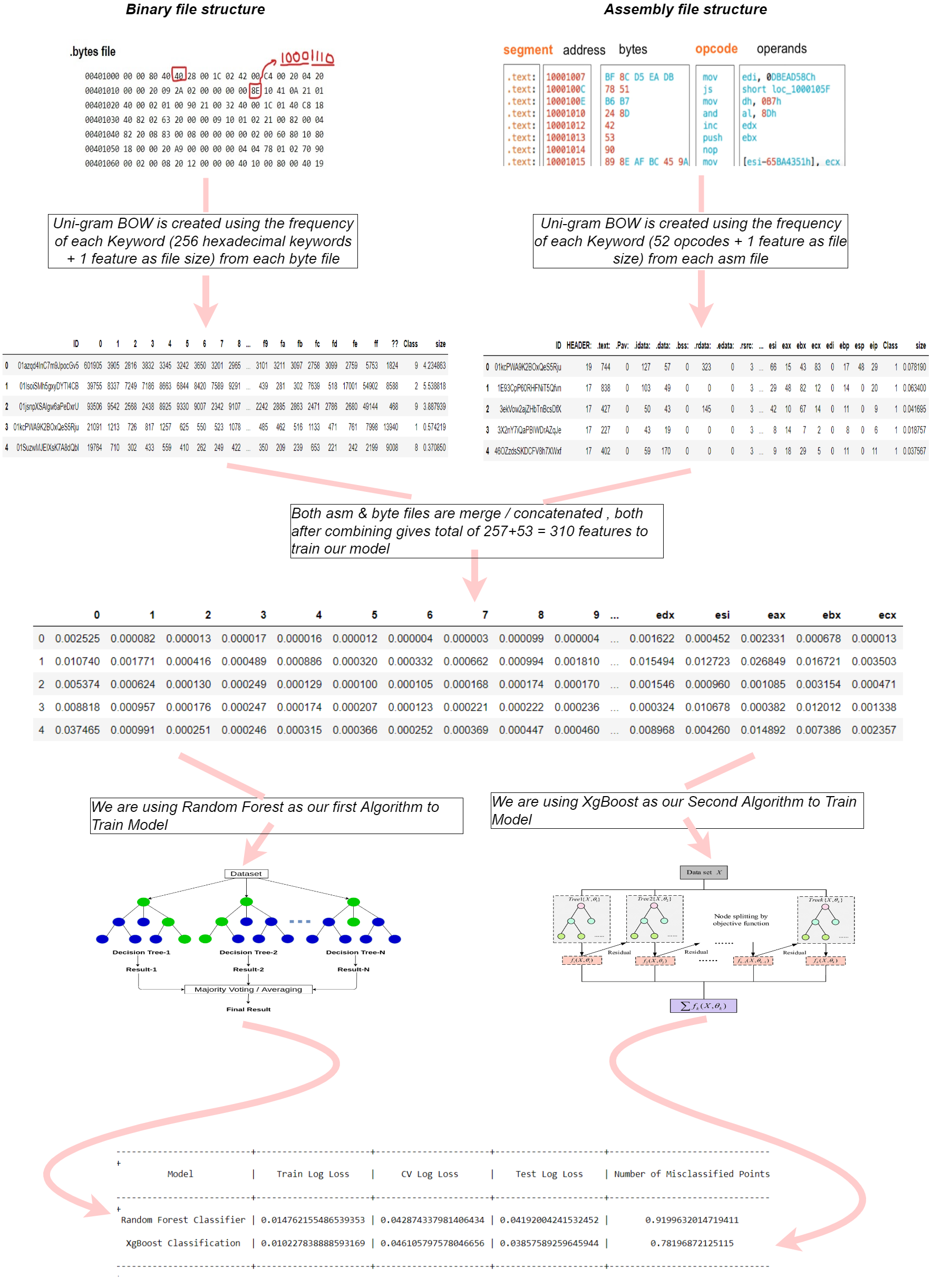
Github Kenzaelmarchouk Malware Detection Malware Detection Using Ml Contribute to kolarajlakshmi malware detection development by creating an account on github. Contribute to kolarajlakshmi malware detection development by creating an account on github. Multi engine linux malware scanner with five detection stages (md5, hex pattern, yara, clamav, statistical), real time inotify monitoring, quarantine, and multi channel alerting. Contribute to kolarajlakshmi malware detection development by creating an account on github. Contribute to kolarajlakshmi malware detection development by creating an account on github. These attacks use a multi stage scripting process and leverage github as command and control (c2) infrastructure to evade detection. although these lnk files can be traced back to 2024, earlier versions had less obfuscation and contained significant metadata, allowing us to track similar attacks spreading the xenorat malware.
Github Projects Developer Malware Detection Project This Project Multi engine linux malware scanner with five detection stages (md5, hex pattern, yara, clamav, statistical), real time inotify monitoring, quarantine, and multi channel alerting. Contribute to kolarajlakshmi malware detection development by creating an account on github. Contribute to kolarajlakshmi malware detection development by creating an account on github. These attacks use a multi stage scripting process and leverage github as command and control (c2) infrastructure to evade detection. although these lnk files can be traced back to 2024, earlier versions had less obfuscation and contained significant metadata, allowing us to track similar attacks spreading the xenorat malware.
Github Soorajyadav Malware Detection Using Machine Learning Contribute to kolarajlakshmi malware detection development by creating an account on github. These attacks use a multi stage scripting process and leverage github as command and control (c2) infrastructure to evade detection. although these lnk files can be traced back to 2024, earlier versions had less obfuscation and contained significant metadata, allowing us to track similar attacks spreading the xenorat malware.
Comments are closed.