Github Fal Com Scammer Invader Imbed Script Into Picture To Be
Javascript Traps For Analysts Sans Internet Storm Center Imbed script into picture to be activated when recieved by scammer, to report scammer ip address and or take snapshot using scammer webcam and report information back to scamme for reporting to proper athoritys fal com scammer invader. Imbed script into picture to be activated when recieved by scammer, to report scammer ip address and or take snapshot using scammer webcam and report information back to scamme for reporting to pro….

Angler Exploit Kit Generated By Admedia Gates Sans Isc To obscure the stagers retrieval of the payload, which will be hosted on the internet, we embed it into a png file. when our stager is executed through phishing mechanisms it will make a http get request to retrieve and extract the payload from the image and then execute it in memory. Let’s clear something up: simply embedding shellcode into an image does not magically turn it into an executable. double clicking a won’t detonate malware — and if anyone says otherwise,. Discover the rising threat of malware embedded in multimedia and interactive files. real world cases of svg malware, steganography in images, and exploits in office documents with scripts are detailed along with defense tips. Hackers embed malicious code into image files by hiding the code within the pixels of the image, extracting specific pixel information to execute the payload. this technique has been observed in cyberespionage groups such as worok, who use it to evade detection on compromised systems.
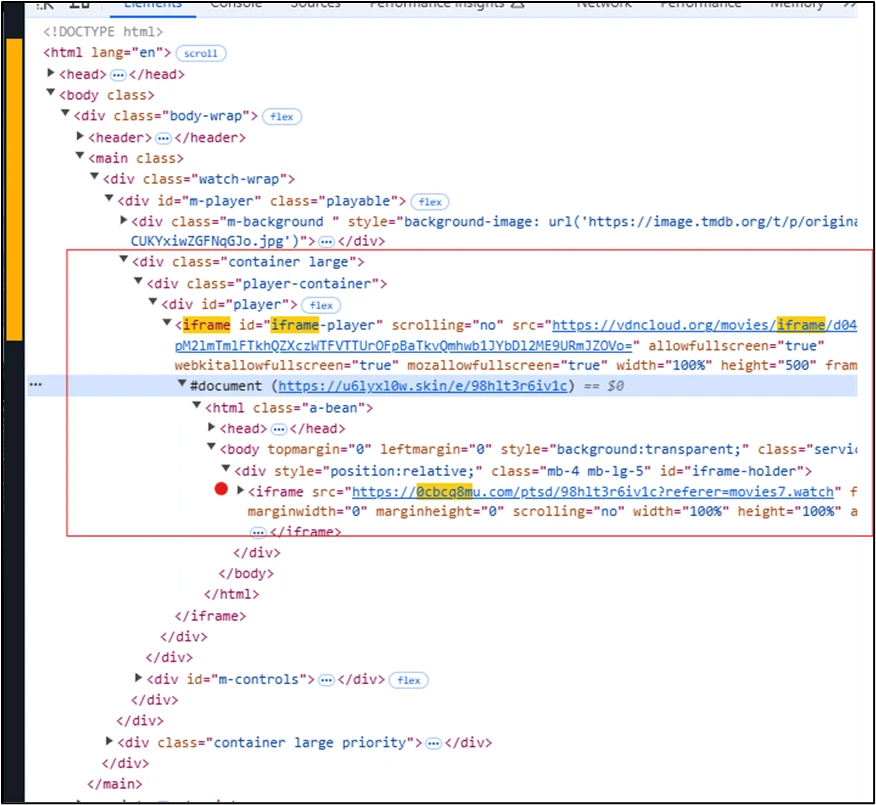
Malvertising Campaign Leads To Info Stealers Hosted On Github Discover the rising threat of malware embedded in multimedia and interactive files. real world cases of svg malware, steganography in images, and exploits in office documents with scripts are detailed along with defense tips. Hackers embed malicious code into image files by hiding the code within the pixels of the image, extracting specific pixel information to execute the payload. this technique has been observed in cyberespionage groups such as worok, who use it to evade detection on compromised systems. Instead of targeting .ico files, however, attackers chose to inject content into real files — both on compromised sites and in booby trapped magento repos on github. our security analyst keith petkus found this piece of malware injected on a compromised magento 2.x site. Threat actors have been observed concealing malicious code in images to deliver malware such as vip keylogger and 0bj3ctivity stealer as part of separate campaigns. There are 2 ways you can do this, the first is simply writing a script in a text file and saving it as a jpg. this is obviously not an image, but it will work. if you want a real image, you can take your image and use a hexeditor to add your script to the image metadata. Cybercriminals are able to smuggle malware through seemingly harmless images. check out this new trend and how you should defend against it.

Behind The Script Unmasking Phishing Attacks Using Google Apps Script Instead of targeting .ico files, however, attackers chose to inject content into real files — both on compromised sites and in booby trapped magento repos on github. our security analyst keith petkus found this piece of malware injected on a compromised magento 2.x site. Threat actors have been observed concealing malicious code in images to deliver malware such as vip keylogger and 0bj3ctivity stealer as part of separate campaigns. There are 2 ways you can do this, the first is simply writing a script in a text file and saving it as a jpg. this is obviously not an image, but it will work. if you want a real image, you can take your image and use a hexeditor to add your script to the image metadata. Cybercriminals are able to smuggle malware through seemingly harmless images. check out this new trend and how you should defend against it.
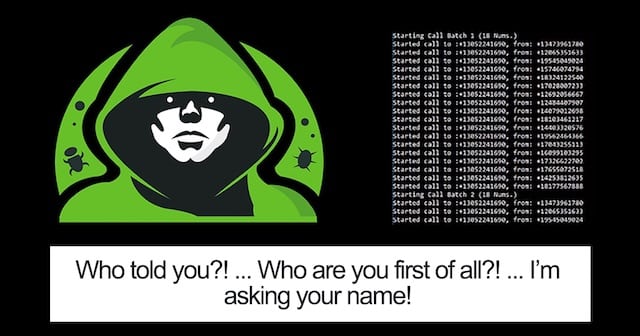
Programmer Writes Script That Calls Scammers 28 Times A Second And They There are 2 ways you can do this, the first is simply writing a script in a text file and saving it as a jpg. this is obviously not an image, but it will work. if you want a real image, you can take your image and use a hexeditor to add your script to the image metadata. Cybercriminals are able to smuggle malware through seemingly harmless images. check out this new trend and how you should defend against it.
Comments are closed.