Github Fa1c0n35 Mac Flooding
Github Fa1c0n35 Mac Flooding Contribute to fa1c0n35 mac flooding development by creating an account on github. Learn how to use mac flooding to sniff traffic and arp cache poisoning to manipulate network traffic as a mitm. for the sake of this room, let’s assume the following: while conducting a.
Github Mertkahyaoglu Macflood Mac Address Flooding Script In order to complete the fast forwarding of data, the table has an automatic learning mechanism; a flood attack means that the attacker uses this learning mechanism to continuously send different mac addresses to the switch, filling the entire mac table. What is mac flooding? definition: mac flooding is a network attack technique that overloads a switch’s mac (media access control) address table with fake mac addresses, causing it to fail and operate as a hub. Learn what mac flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat. I successfully completed the l2 mac flooding & arp spoofing room on tryhackme, mastering techniques like mac flooding and arp spoofing for network manipulation.
Github Ajeetdev Tryackme L2 Mac Flooding Arp Spoofing Write Up Learn what mac flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat. I successfully completed the l2 mac flooding & arp spoofing room on tryhackme, mastering techniques like mac flooding and arp spoofing for network manipulation. Fa1c0n35 has 175 repositories available. follow their code on github. In the "mac flooding attack" tutorial, we explained how to easily saturate the mac address table (cam table) of a switch with a large number of mac addresses. with just a few lines of python code and the scapy manipulation program, we turned a switch into a legacy hub device. For the last few years, mac users are facing a wave of fake apps on microsoft owned github that disguise themselves as popular software, only to trick victims into handing over their passwords. This room focuses on mac flooding and arp spoofing or poisoning. it deeply explains all the underlying concepts and basics that a learner should have when doing a network penetration testing.

Mac Flooding Pdf Fa1c0n35 has 175 repositories available. follow their code on github. In the "mac flooding attack" tutorial, we explained how to easily saturate the mac address table (cam table) of a switch with a large number of mac addresses. with just a few lines of python code and the scapy manipulation program, we turned a switch into a legacy hub device. For the last few years, mac users are facing a wave of fake apps on microsoft owned github that disguise themselves as popular software, only to trick victims into handing over their passwords. This room focuses on mac flooding and arp spoofing or poisoning. it deeply explains all the underlying concepts and basics that a learner should have when doing a network penetration testing.
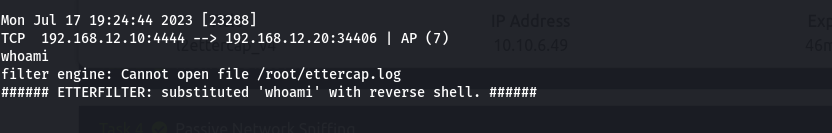
Tryhackme Layer 2 Mac Flooding And Arp Spoofing Nz1okaph1l For the last few years, mac users are facing a wave of fake apps on microsoft owned github that disguise themselves as popular software, only to trick victims into handing over their passwords. This room focuses on mac flooding and arp spoofing or poisoning. it deeply explains all the underlying concepts and basics that a learner should have when doing a network penetration testing.
Comments are closed.