Github Developer Blackmail Code Repository Exploitation
Malicious Code In Fake Github Repositories Kaspersky Official Blog This is github blackmail — a form of repository exploitation aimed squarely at developers’ careers. the danger isn’t faulty code; it’s reputational damage, job security, and control. Attackers have been seen cloning github repositories and adding malicious code to forks designed to infect developer systems and pilfer sensitive files that included software keys.

Over 100 000 Infected Repos Found On Github Exploits can be used by attackers to gain unauthorized access, escalate privileges, execute arbitrary code, or cause a denial of service. this topic covers the various types of exploits, such as zero day exploits, remote code execution, and privilege escalation. In 2024, gitlab developers discovered two critical vulnerabilities in their system. due to verification errors, attackers could hijack user accounts and modify repository contents. this type of attack is known as repojacking. Attackers presumably tapped github access data via phishing, copied and deleted the contents of the repositories and then blackmailed those affected. Github and gitlab are essential tools for programmers, project managers, and software developers worldwide. however, this widespread trust is increasingly being weaponized by cybercriminals. because these git repository platforms are critical for business operations, enterprise networks cannot simply block them.
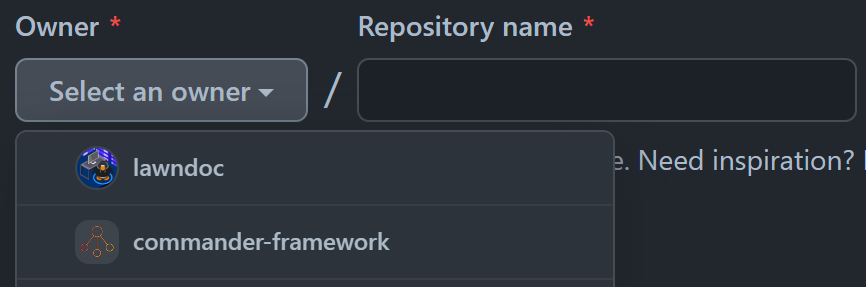
Thinking Like A Hacker Finding Source Code Leaks On Github Attackers presumably tapped github access data via phishing, copied and deleted the contents of the repositories and then blackmailed those affected. Github and gitlab are essential tools for programmers, project managers, and software developers worldwide. however, this widespread trust is increasingly being weaponized by cybercriminals. because these git repository platforms are critical for business operations, enterprise networks cannot simply block them. Threat actors leverage anthropic's claude code source leak to distribute vidar information stealing malware through malicious github repositories targeting developers. This article delves into the multifaceted ways github is exploited for malicious infrastructure, the challenges posed to cybersecurity and effective strategies for mitigation. In the latest attack, hackers compromised python repos with an obfuscated version of a credential stealer (blackcap grabber). once login passwords, browser cookies and other sensitive information. Once attacker controlled code runs in the context of a privileged github actions job, every other misconfiguration becomes exploitable, from token misuse to secret exposure. let’s walk through a simple example.
Malicious Actors Exploit Github To Distribute Fake Exploits Threat actors leverage anthropic's claude code source leak to distribute vidar information stealing malware through malicious github repositories targeting developers. This article delves into the multifaceted ways github is exploited for malicious infrastructure, the challenges posed to cybersecurity and effective strategies for mitigation. In the latest attack, hackers compromised python repos with an obfuscated version of a credential stealer (blackcap grabber). once login passwords, browser cookies and other sensitive information. Once attacker controlled code runs in the context of a privileged github actions job, every other misconfiguration becomes exploitable, from token misuse to secret exposure. let’s walk through a simple example.

Mods On Github Come With Infostealers Cybernews In the latest attack, hackers compromised python repos with an obfuscated version of a credential stealer (blackcap grabber). once login passwords, browser cookies and other sensitive information. Once attacker controlled code runs in the context of a privileged github actions job, every other misconfiguration becomes exploitable, from token misuse to secret exposure. let’s walk through a simple example.
Comments are closed.