Github Cyberheroess Suite Exploit Suite Exploit Focuses On The

New Exploit Puts Thousands Of Github Repositories And Millions Of Users "suite exploit focuses on the dynamics of exploits." cyberheroess suite exploit. We develop ai driven waf bypass, penetration testing tools, and automation for security assessment cyberheroess.
New Exploit Puts Thousands Of Github Repositories And Millions Of Users Advanced security assessment suite featuring quantum inspired algorithms cyberheroess suite. "suite exploit focuses on the dynamics of exploits." actions · cyberheroess suite exploit. "suite exploit focuses on the dynamics of exploits." cyberheroess suite exploit. "suite exploit focuses on the dynamics of exploits." suite exploit readme.md at main · cyberheroess suite exploit.

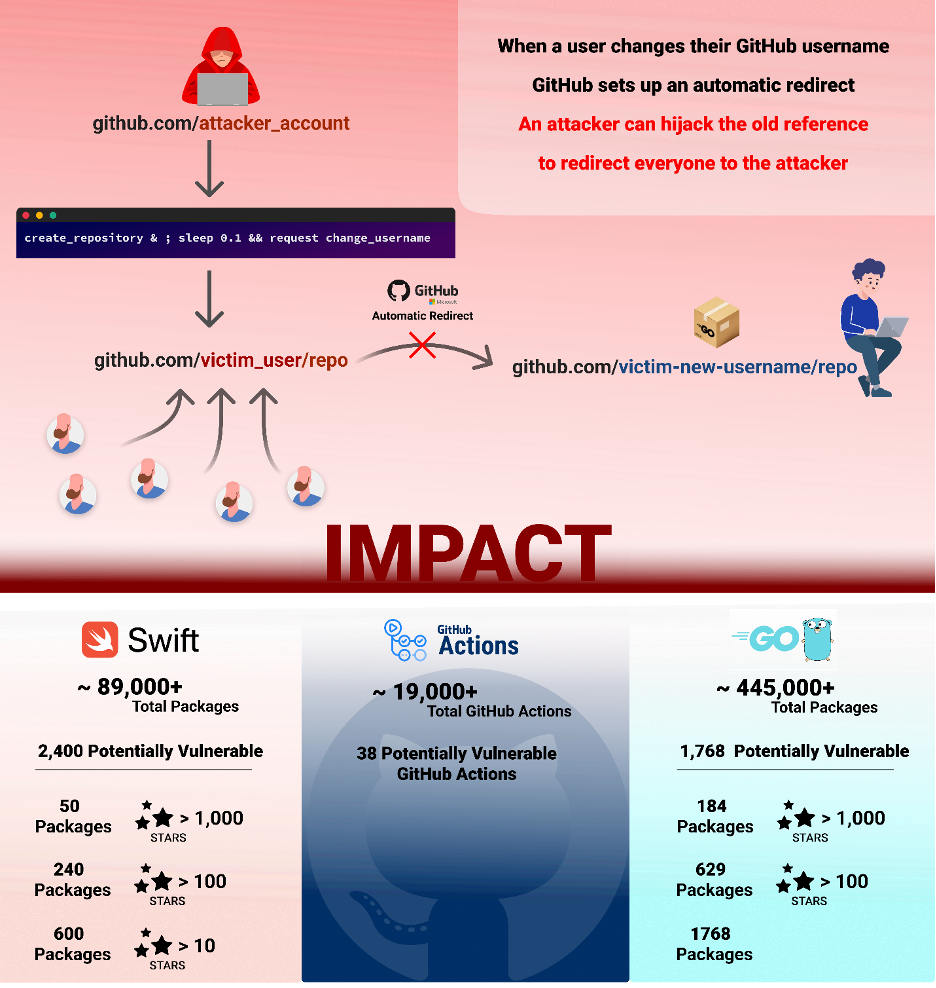
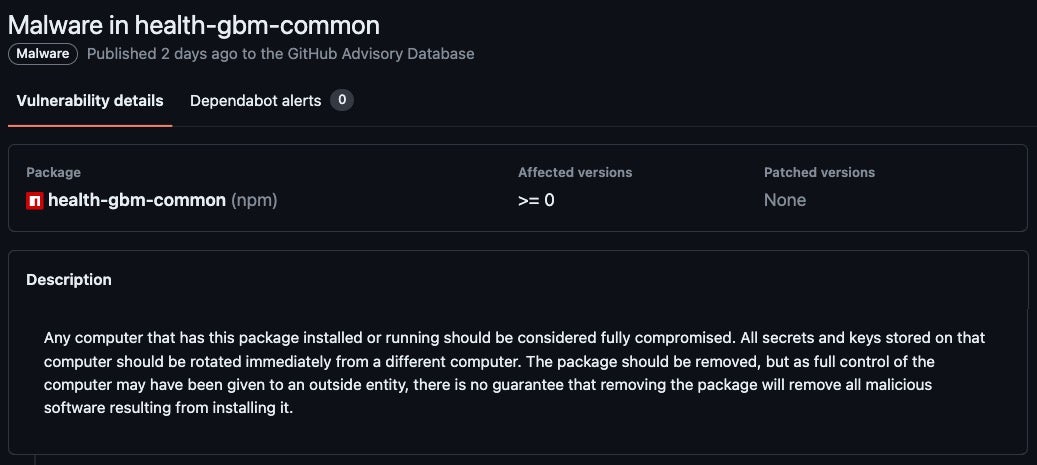
Abuse Of Github For Malicious Purposes A Stealthy Cyber Threat "suite exploit focuses on the dynamics of exploits." cyberheroess suite exploit. "suite exploit focuses on the dynamics of exploits." suite exploit readme.md at main · cyberheroess suite exploit. A curated repository of over 180,000 exploitable vulnerabilities and vetted computer software exploits. exploits are all included in the metasploit framework. this database is updated frequently and contains the most recent security research. The exploit database exploits, shellcode, 0days, remote exploits, local exploits, web apps, vulnerability reports, security articles, tutorials and more. The ai bot, still active on github, is hacking one repo after another, curating its own brag page, and claiming to have scanned over 47,000 repositories. in just one week, it targeted at least six popular open source projects, including those from microsoft and datadog. This article close this series of github action exploitation, we showcase how dangerous it can be to allow external user to execute arbitrary code in self hosted runners through example of vulnerable repository such as haskell and scroll.
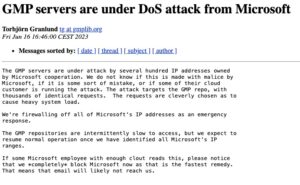
Exploiting Repos 6 Ways Threat Actors Abuse Devops Platforms A curated repository of over 180,000 exploitable vulnerabilities and vetted computer software exploits. exploits are all included in the metasploit framework. this database is updated frequently and contains the most recent security research. The exploit database exploits, shellcode, 0days, remote exploits, local exploits, web apps, vulnerability reports, security articles, tutorials and more. The ai bot, still active on github, is hacking one repo after another, curating its own brag page, and claiming to have scanned over 47,000 repositories. in just one week, it targeted at least six popular open source projects, including those from microsoft and datadog. This article close this series of github action exploitation, we showcase how dangerous it can be to allow external user to execute arbitrary code in self hosted runners through example of vulnerable repository such as haskell and scroll.

Exploiting Repos 6 Ways Threat Actors Abuse Devops Platforms The ai bot, still active on github, is hacking one repo after another, curating its own brag page, and claiming to have scanned over 47,000 repositories. in just one week, it targeted at least six popular open source projects, including those from microsoft and datadog. This article close this series of github action exploitation, we showcase how dangerous it can be to allow external user to execute arbitrary code in self hosted runners through example of vulnerable repository such as haskell and scroll.
Exploiting Repos 6 Ways Threat Actors Abuse Devops Platforms
Comments are closed.