Github Com Secret You Did Not Know About
Github Activation Secret Secret Security researcher sharon brizinov, in collaboration with truffle security, has conducted a sweeping investigation of github's "oops commits", force pushed or deleted commits that remain. Today, we’re unveiling hasmysecretleaked, a free toolset to help security and devops engineers verify if their organization’s secrets have leaked on github .
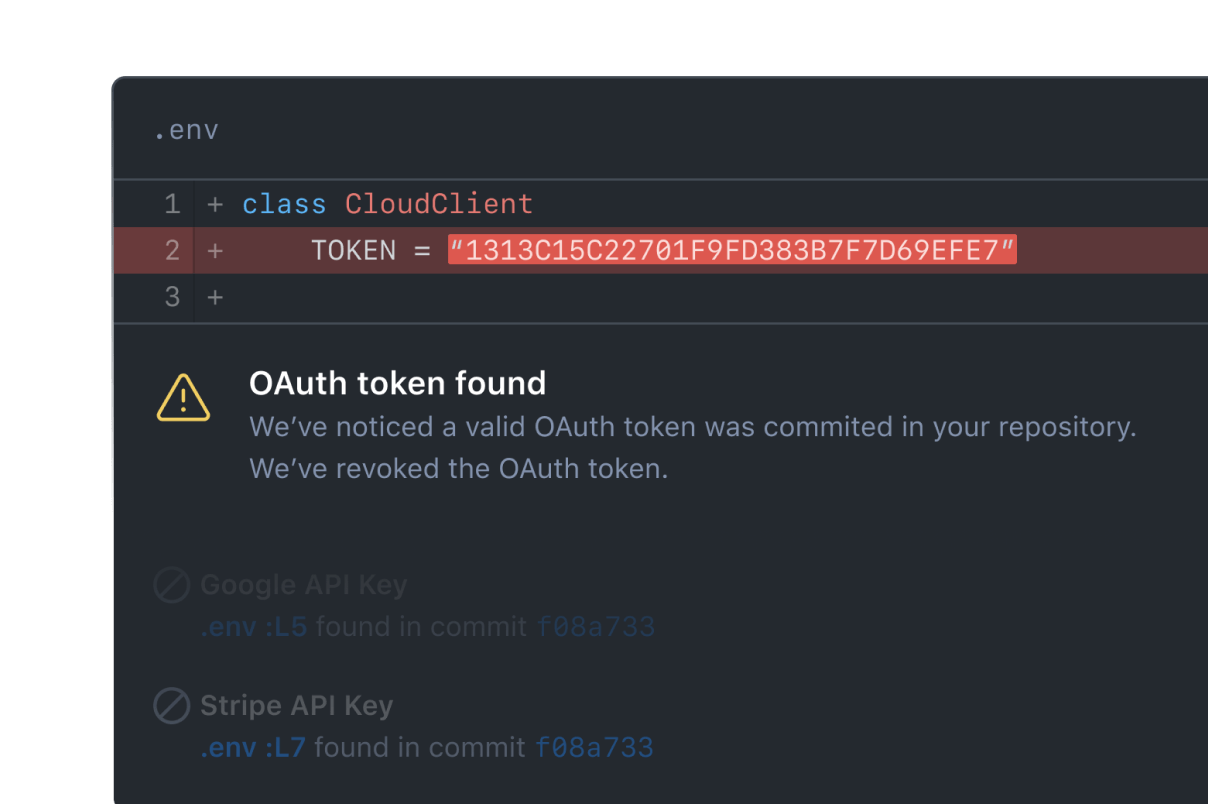
Github Let S Build From Here Github Your secrets, your business. detect, prevent, and remediate leaked secrets across your organization. from planning and discussion to code review, github keeps your team’s conversation and context next to your code. plan with clarity. organize everything from high level roadmaps to everyday tasks. Once you've published a secret to a public git repository you should assume breach, meaning that you should treat the secret as compromised no matter if it's only been online for a few minutes. Here's what it finds: → known vulnerabilities in every package and dependency you use → passwords, api keys, and secrets accidentally buried in your code → cloud and container misconfigs that would fail any audit → license problems you didn't know existed → a full software inventory of everything you ship here's the wildest part: brew. Learn how github is making it easier to protect yourself from exposed secrets, including today’s launches of standalone secret protection, org wide scanning, and better access for teams of all sizes.
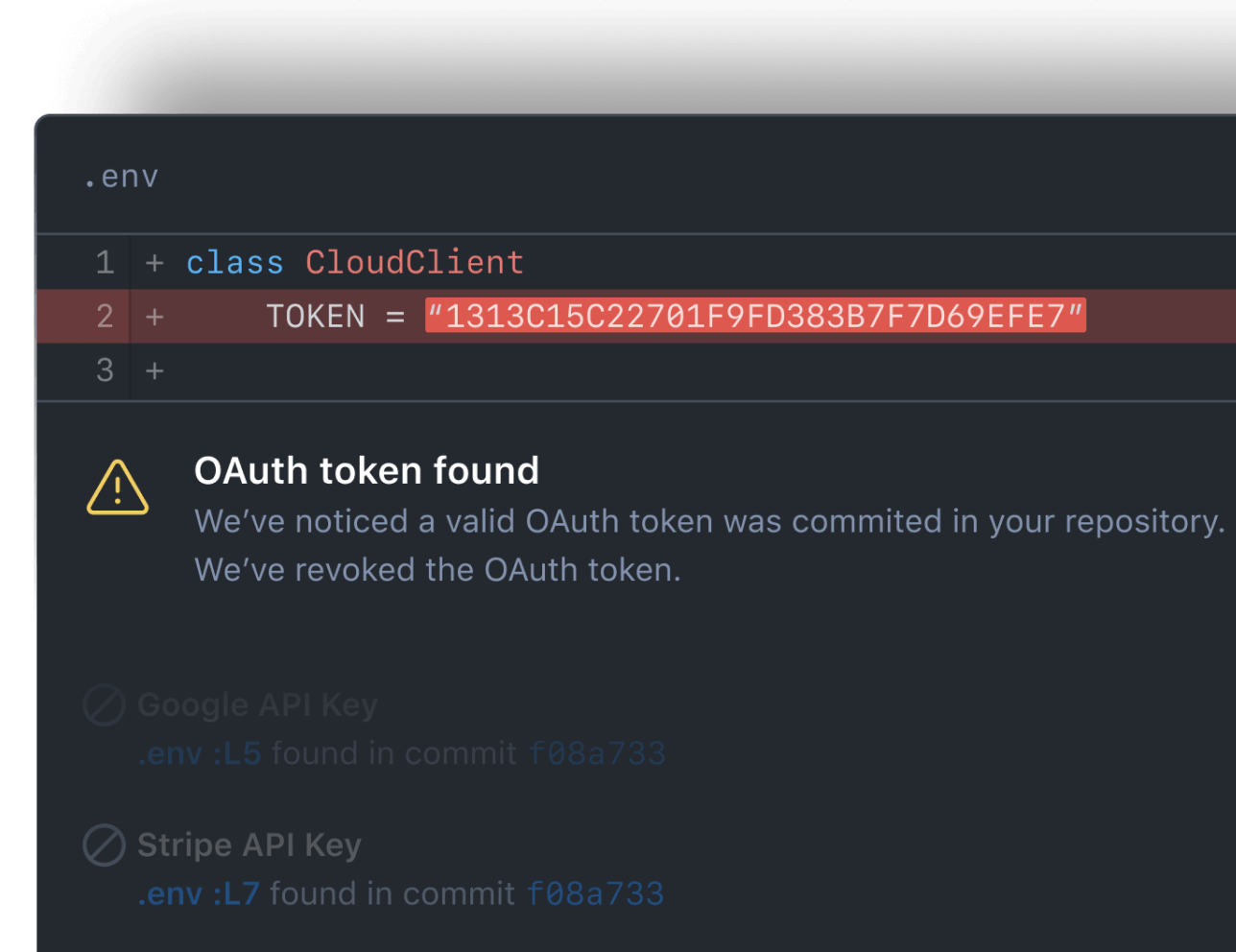
Github Let S Build From Here Github Here's what it finds: → known vulnerabilities in every package and dependency you use → passwords, api keys, and secrets accidentally buried in your code → cloud and container misconfigs that would fail any audit → license problems you didn't know existed → a full software inventory of everything you ship here's the wildest part: brew. Learn how github is making it easier to protect yourself from exposed secrets, including today’s launches of standalone secret protection, org wide scanning, and better access for teams of all sizes. Secrets in git history remain highly vulnerable, contributing to the surge in accidental exposures. github blocks several secrets per minute using automated push protection. despite ongoing efforts, secret leakage is still a leading cause of security incidents—and it’s largely preventable. That link provides instructions on how to access commits from the reflog of a github repository, not how to expire or otherwise delete them. you don’t even need the pushes api to see commits that were force pushed away. A white hat hacker discovered thousands of active secrets, including admin access tokens, by scanning deleted github commits. Gitguardian just published their 2026 secrets sprawl report, and one number stopped me cold: ai assisted commits on public github leak secrets at 3.2%, roughly double the 1.5% baseline for all.
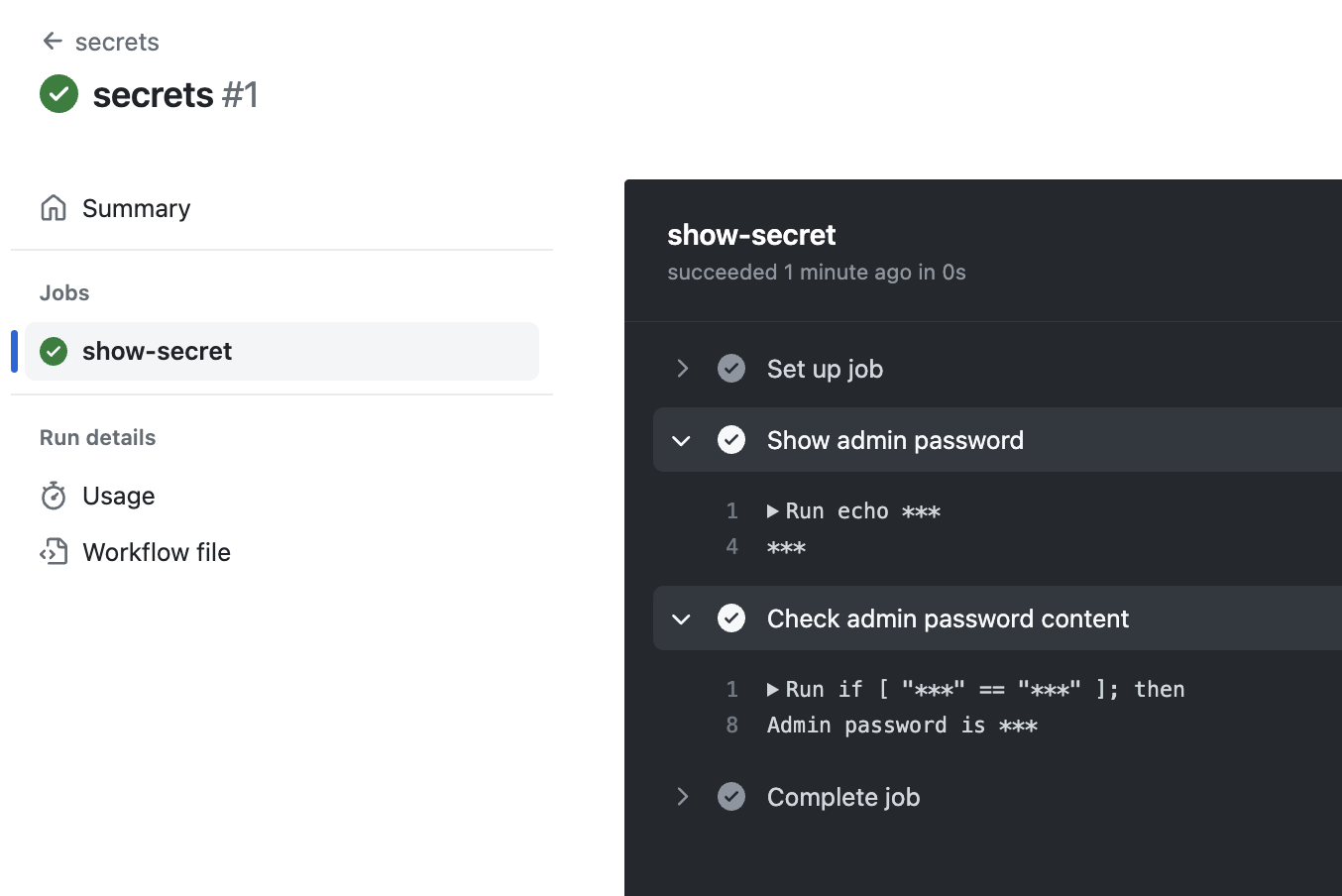
Github Actions Secrets Christos Galanopoulos Secrets in git history remain highly vulnerable, contributing to the surge in accidental exposures. github blocks several secrets per minute using automated push protection. despite ongoing efforts, secret leakage is still a leading cause of security incidents—and it’s largely preventable. That link provides instructions on how to access commits from the reflog of a github repository, not how to expire or otherwise delete them. you don’t even need the pushes api to see commits that were force pushed away. A white hat hacker discovered thousands of active secrets, including admin access tokens, by scanning deleted github commits. Gitguardian just published their 2026 secrets sprawl report, and one number stopped me cold: ai assisted commits on public github leak secrets at 3.2%, roughly double the 1.5% baseline for all.
Comments are closed.