Github Carlos Al User Kernel Syscall Hook
Linux Rootkits Explained Part 2 Loadable Kernel Modules Wiz Blog Combining kernel and user mode hooks for enhanced system monitoring this project implements techniques for both user mode and kernel mode system call hooking on windows 11. Contribute to carlos al user kernel syscall hook development by creating an account on github.
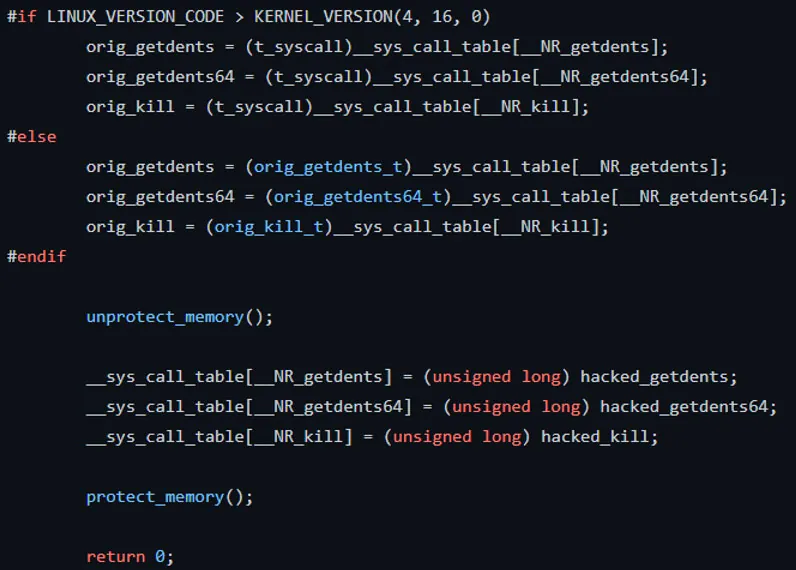
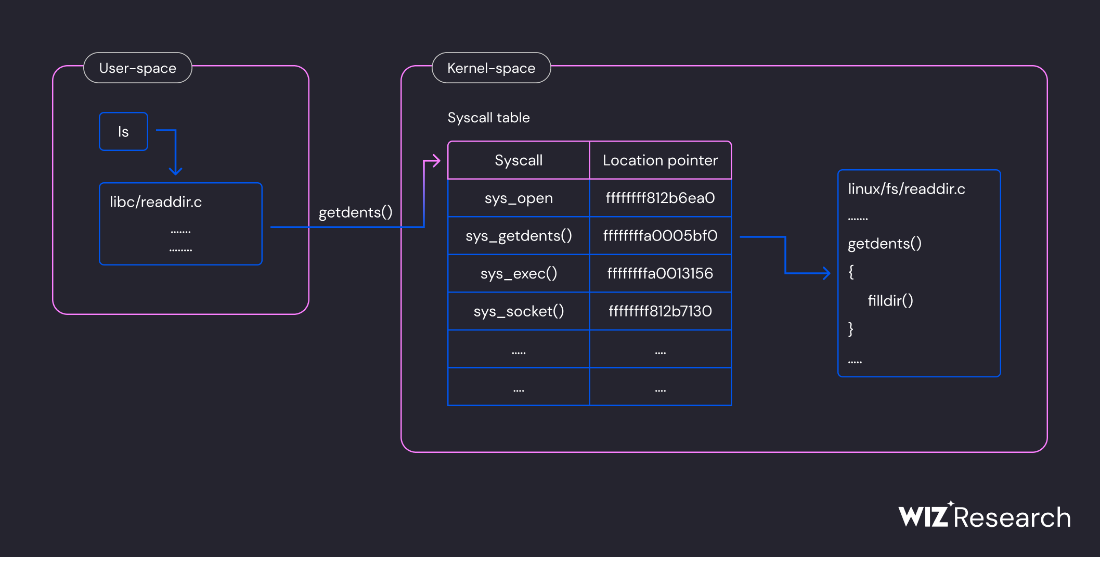
Hunting Rootkits With Ebpf Detecting Linux Syscall Hooking Popular repositories user kernel syscall hook public rust 95 15 windows kernel rs public rust 21 3 platform solutions. Contribute to carlos al user kernel syscall hook development by creating an account on github. Contemporary methods for hooking system calls in user and kernel mode on windows 11 lnkd.in def4 3nc #kernelmode #usermode #windowsdevelopment #cybersecurity #reverseengineering #. Not really, the purpose of the exercise is to load a kernel module that will hook a system call for the entire system. it doesn't really matter what it does at that point.
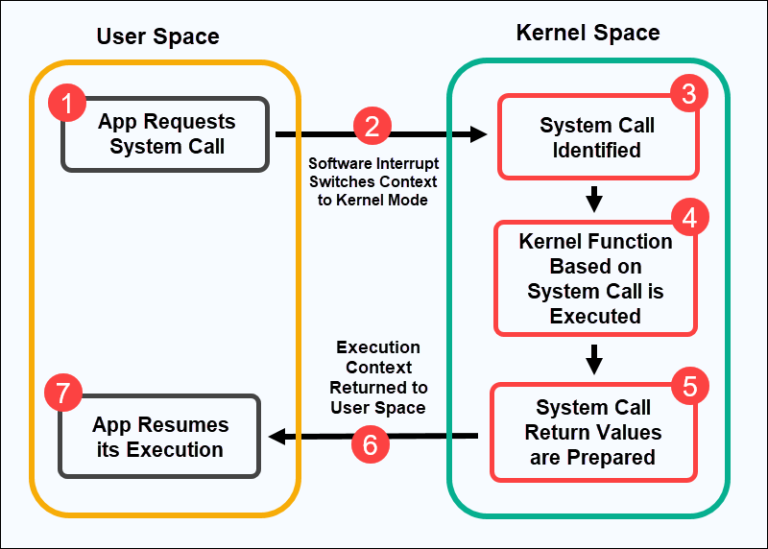
System Calls In Operating System Explained Phoenixnap Kb Contemporary methods for hooking system calls in user and kernel mode on windows 11 lnkd.in def4 3nc #kernelmode #usermode #windowsdevelopment #cybersecurity #reverseengineering #. Not really, the purpose of the exercise is to load a kernel module that will hook a system call for the entire system. it doesn't really matter what it does at that point. Syscall user dispatch provides functionality for compatibility layers to quickly capture system calls issued by a non native part of the application, while not impacting the linux native regions of the process. In this section, you will download all necessary tools to add a basic system call to the linux kernel and run it. this is the only part of the entire process where network connectivity is necessary. The xv6 kernel isolates user programs from each other and isolates the kernel from user programs. as you saw in the above assignments, an application cannot directly call a function in the kernel or in another user program; instead, interactions occur only through system calls. Turns out there is some hidden logic behind this little bit. when kisystemcall64 gets called it can be redirected to an "alternative" handler. this feature is apparently made and reserved for windows defender. if kthread >header.altsyscall is set to true, pspicoaltsystemcalldispatch will be called.
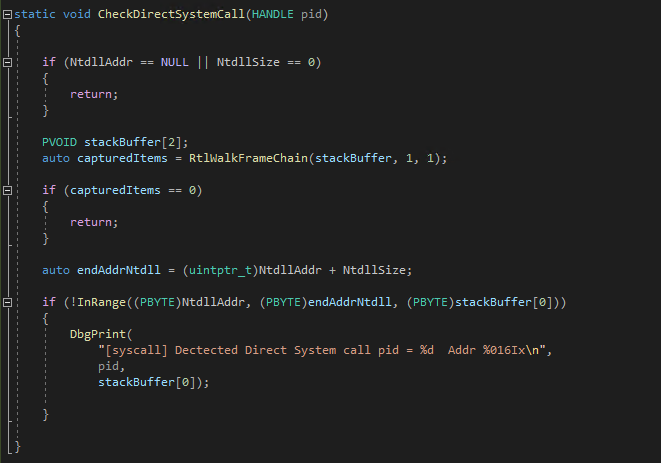
Detecting Malicious Artifacts Etw Consumer In Kernel Mode Countercraft Syscall user dispatch provides functionality for compatibility layers to quickly capture system calls issued by a non native part of the application, while not impacting the linux native regions of the process. In this section, you will download all necessary tools to add a basic system call to the linux kernel and run it. this is the only part of the entire process where network connectivity is necessary. The xv6 kernel isolates user programs from each other and isolates the kernel from user programs. as you saw in the above assignments, an application cannot directly call a function in the kernel or in another user program; instead, interactions occur only through system calls. Turns out there is some hidden logic behind this little bit. when kisystemcall64 gets called it can be redirected to an "alternative" handler. this feature is apparently made and reserved for windows defender. if kthread >header.altsyscall is set to true, pspicoaltsystemcalldispatch will be called.
Comments are closed.