Github Byoniq Bugbountymethod Bug Bounty Methodology
Github Byoniq Bugbountymethod Bug Bounty Methodology This checklist provides a systematic approach to finding and exploiting vulnerabilities in bug bounty programs. it serves as a quick reference to ensure you cover all critical aspects during your testing process. This methodology outlines the steps and tools necessary for various scopes in bug bounty hunting, including reconnaissance, user management, input handling, and application logic checks.
Github Anonx Hunter Bug Bounty Methodology Bug Bounty Methodology This checklist provides a systematic approach to finding and exploiting vulnerabilities in bug bounty programs. it serves as a quick reference to ensure you cover all critical aspects during your testing process. Thoroughly read and understand the bug bounty program's policy (scope, out of scope, rewards, disclosure rules). My bug bounty hunting methodology 2025 dives into the refined strategies and tools i’ve developed over years of experience, tailored to uncover vulnerabilities efficiently in modern web. Here i'm documenting all the methodologies i found on internet so you can learn from them and make your own unique methodology from it.
Github Amrelsagaei Bug Bounty Hunting Methodology 2025 Bug Bounty My bug bounty hunting methodology 2025 dives into the refined strategies and tools i’ve developed over years of experience, tailored to uncover vulnerabilities efficiently in modern web. Here i'm documenting all the methodologies i found on internet so you can learn from them and make your own unique methodology from it. A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters. Whether you’re uncovering subdomains, analyzing javascript files, or identifying high impact vulnerabilities, this methodology is tailored to get you started on the right track. A structured approach is key to efficient bug hunting. based on proven frameworks, here’s a step by step methodology that combines reconnaissance, enumeration, testing, and reporting. If you are reading this post, you probably want to improve your bug bounty methodology or find out what bug bounty methodology is. at the most fundamental level, methodology is simply how a hacker approaches and attacks a target.
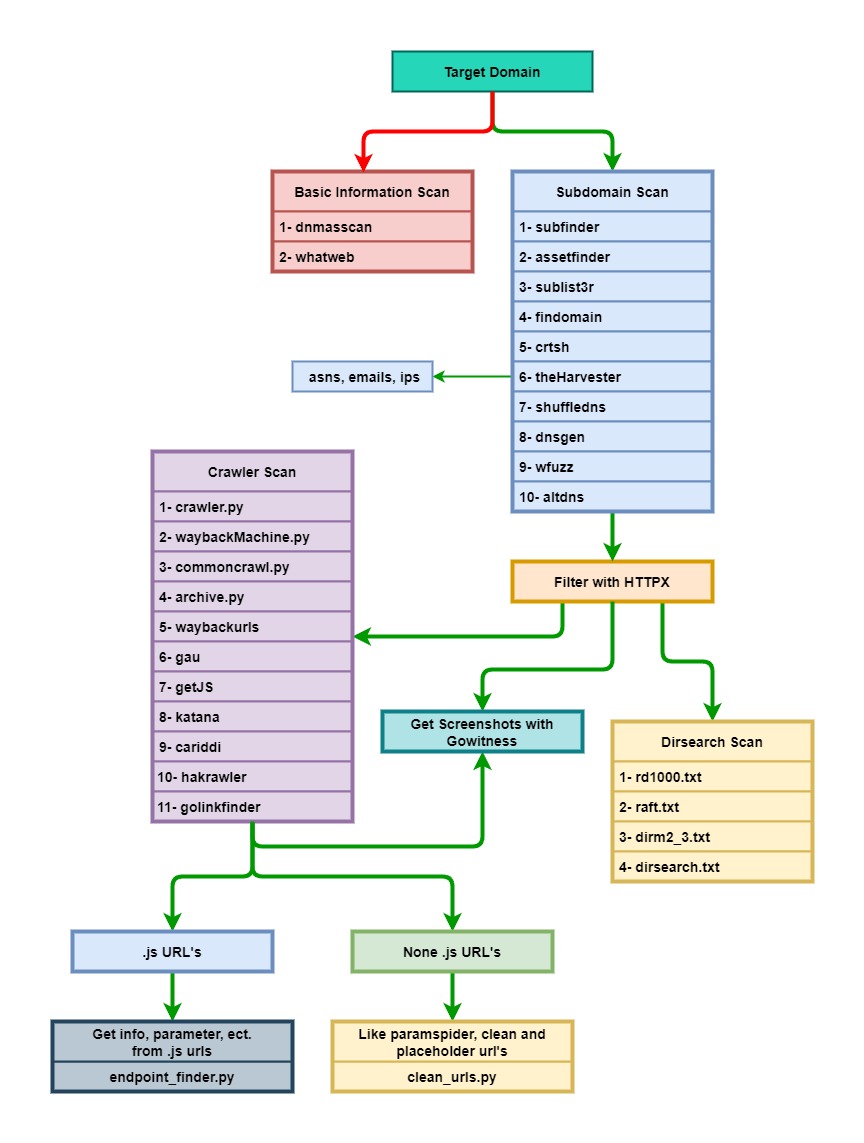
Bug Bounty Methodology Otorecon Mr0wido S Blog A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters. Whether you’re uncovering subdomains, analyzing javascript files, or identifying high impact vulnerabilities, this methodology is tailored to get you started on the right track. A structured approach is key to efficient bug hunting. based on proven frameworks, here’s a step by step methodology that combines reconnaissance, enumeration, testing, and reporting. If you are reading this post, you probably want to improve your bug bounty methodology or find out what bug bounty methodology is. at the most fundamental level, methodology is simply how a hacker approaches and attacks a target.
Bugbounty Github Topics Github A structured approach is key to efficient bug hunting. based on proven frameworks, here’s a step by step methodology that combines reconnaissance, enumeration, testing, and reporting. If you are reading this post, you probably want to improve your bug bounty methodology or find out what bug bounty methodology is. at the most fundamental level, methodology is simply how a hacker approaches and attacks a target.
Comments are closed.