Github 0sha0 Simplebypass Simple Shellcode Loader Using Syscall

D1rklrd Shellcode Loader With Indirect Dynamic Syscall Implementation Simple shellcode loader using 'syscall' 'detours' 'simple hijacking shellcode' 'dynamic function' to bypass 0sha0 simplebypass. Simple shellcode loader using 'syscall' 'detours' 'simple hijacking shellcode' 'dynamic function' to bypass simplebypass readme.md at main · 0sha0 simplebypass.
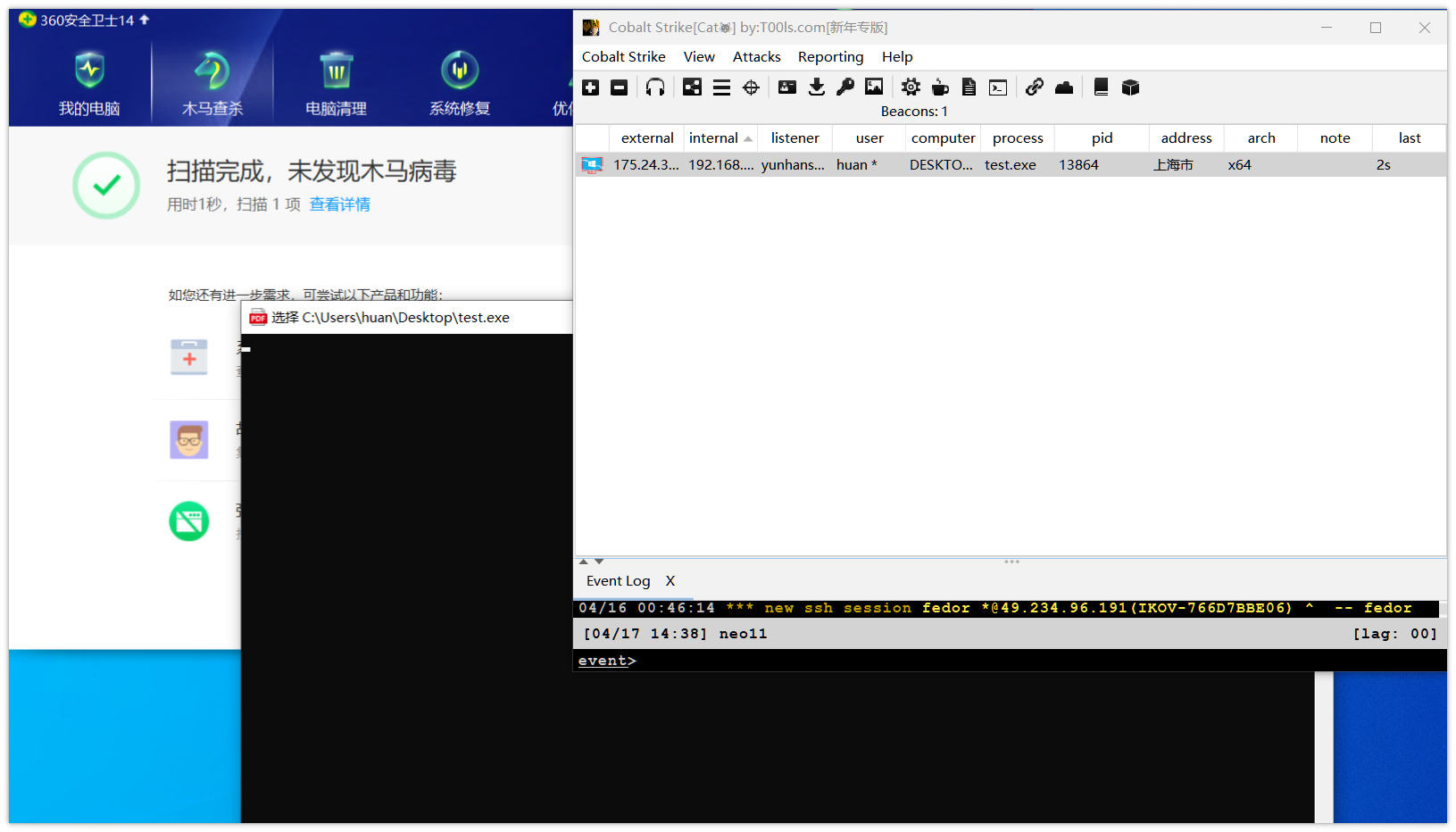
免杀技术 Go Shellcode加载bypassav 腾讯云开发者社区 腾讯云 You can create a release to package software, along with release notes and links to binary files, for other people to use. learn more about releases in our docs. Follow their code on github. Simple shellcode loader using 'syscall' 'detours' 'simple hijacking shellcode' 'dynamic function' to bypass simplebypass simplebypass.sln at main · 0sha0 simplebypass. In this module, we’re gonna write a simple shellcode loader also known as local shellcode injection using c and win32 api. if i get enough free time, i’ll continue this as a malware development series.
Github Susmdt Indirect Syscall Shellcode Loader Simple shellcode loader using 'syscall' 'detours' 'simple hijacking shellcode' 'dynamic function' to bypass simplebypass simplebypass.sln at main · 0sha0 simplebypass. In this module, we’re gonna write a simple shellcode loader also known as local shellcode injection using c and win32 api. if i get enough free time, i’ll continue this as a malware development series. With our shellcode in hand, we now need to encrypt it using xor and a key of our choice. to do this, i created a simple python script that encrypts the data entered into it using a key (0x5a):. This guide aims to provide a step by step tutorial on creating a minimal shellcode loader using the c programming language. by understanding the concepts presented here, you'll gain insights into low level system interactions and enhance your skills in offensive and defensive security practices. There is a github project called syswhispers which aids greatly in developing software that uses syscalls. this project allows you to easily just reference the ntdll.dll api calls and have it easily changed into a syscall. the project site describes it well. In short, we can generate some raw shellcode from the software of our choice (cobalt strike, metasploit, poshc2, etc) and pass it to the homie to get a loader back that will implement some common edr evasion techniques.
Github Joshfaust Simple Loader Windows Defender Shellcode Execution With our shellcode in hand, we now need to encrypt it using xor and a key of our choice. to do this, i created a simple python script that encrypts the data entered into it using a key (0x5a):. This guide aims to provide a step by step tutorial on creating a minimal shellcode loader using the c programming language. by understanding the concepts presented here, you'll gain insights into low level system interactions and enhance your skills in offensive and defensive security practices. There is a github project called syswhispers which aids greatly in developing software that uses syscalls. this project allows you to easily just reference the ntdll.dll api calls and have it easily changed into a syscall. the project site describes it well. In short, we can generate some raw shellcode from the software of our choice (cobalt strike, metasploit, poshc2, etc) and pass it to the homie to get a loader back that will implement some common edr evasion techniques.
Comments are closed.