Get Started With Splunk Threat Intelligence Management

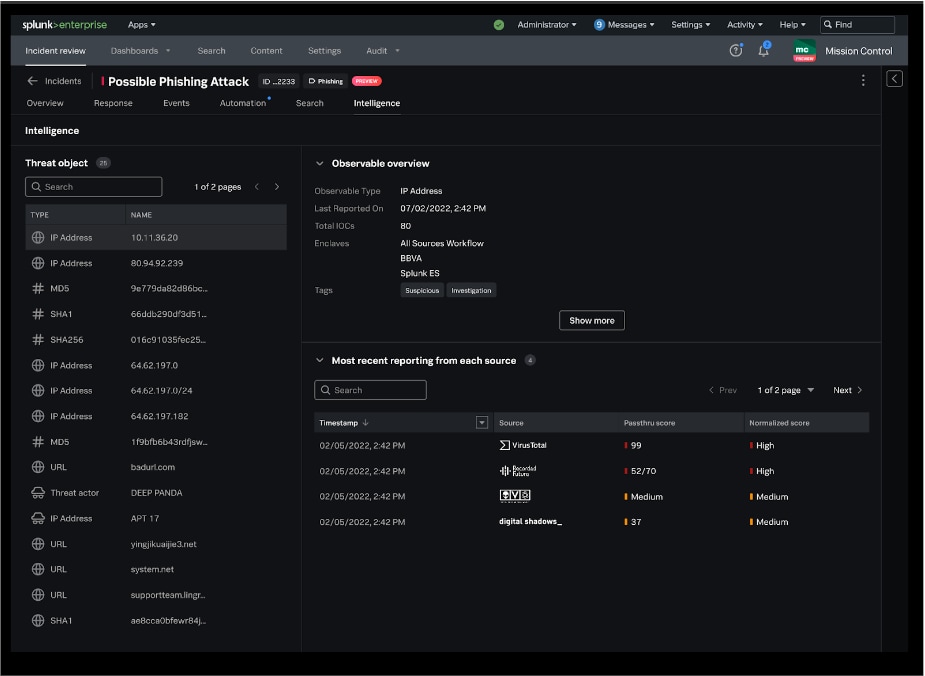
Threat Intelligence Management Feature Brief Splunk Splunk threat intelligence management centralizes and streamlines the collection, normalization, and enrichment of threat intelligence from multiple sources, making it actionable and accessible for security teams. Learn how to configure splunk’s threat intelligence management and see how it can help your team run more effective detections and investigations within splunk.

Splunk Threat Intelligence Management Splunk Learn how to configure splunk’s threat intelligence management and see how it can help your team run more effective detections and investigations within splu. Learn how to configure and manage threat intelligence in splunk enterprise security. this guide covers data enrichment, threat matching, intel collections, correlation searches, dashboards, and more. Splunk enterprise security (es) solves many problems within our socs, including efficient operations. in this course, configuring threat intelligence in splunk enterprise security, you’ll learn how to get this information into the tool from various sources. This guide will walk through the steps of using osint tools like shodan and virustotal, ingesting security logs into splunk, and analyzing the data to identify potential threats.

Splunk Threat Intelligence Management Splunk Splunk enterprise security (es) solves many problems within our socs, including efficient operations. in this course, configuring threat intelligence in splunk enterprise security, you’ll learn how to get this information into the tool from various sources. This guide will walk through the steps of using osint tools like shodan and virustotal, ingesting security logs into splunk, and analyzing the data to identify potential threats. This course will teach you how to configure various threat intelligence sources for use within splunk enterprise security. splunk enterprise security (es) solves many problems within our socs, including efficient operations. The course covers threat hunting with splunk from beginner to advanced levels, based on the latest cybersecurity standard educational topics in the world. This article provides a hands on approach to mastering splunk, covering log analysis, threat detection, and threat hunting. whether you’re a beginner or an experienced professional, this guide will help you upskill your cybersecurity career. Threat hunting with splunk: a how to guide to proactive cyber threat detection and automation. learn how to use splunk powerful data analytics capabilities to identify and mitigate malicious activity.

Splunk Threat Intelligence Management Splunk This course will teach you how to configure various threat intelligence sources for use within splunk enterprise security. splunk enterprise security (es) solves many problems within our socs, including efficient operations. The course covers threat hunting with splunk from beginner to advanced levels, based on the latest cybersecurity standard educational topics in the world. This article provides a hands on approach to mastering splunk, covering log analysis, threat detection, and threat hunting. whether you’re a beginner or an experienced professional, this guide will help you upskill your cybersecurity career. Threat hunting with splunk: a how to guide to proactive cyber threat detection and automation. learn how to use splunk powerful data analytics capabilities to identify and mitigate malicious activity.

Splunk Threat Intelligence Management Splunk This article provides a hands on approach to mastering splunk, covering log analysis, threat detection, and threat hunting. whether you’re a beginner or an experienced professional, this guide will help you upskill your cybersecurity career. Threat hunting with splunk: a how to guide to proactive cyber threat detection and automation. learn how to use splunk powerful data analytics capabilities to identify and mitigate malicious activity.
Splunk Threat Intelligence Management Splunk
Comments are closed.