Generic Unpacking For Apk Jeb In Action

Generic Unpacking For Apk Jeb In Action This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. Jeb 5.9 ships with a new component for android app (apk) reverse engineering: the generic unpacker. the generic unpacker will attempt to emulate the apk to collect dex files that would be generated dynamically, at runtime (i.e. not classes [n].dex).

Unpacking V1 1 Mod Apk Paid For Free For Android This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime.
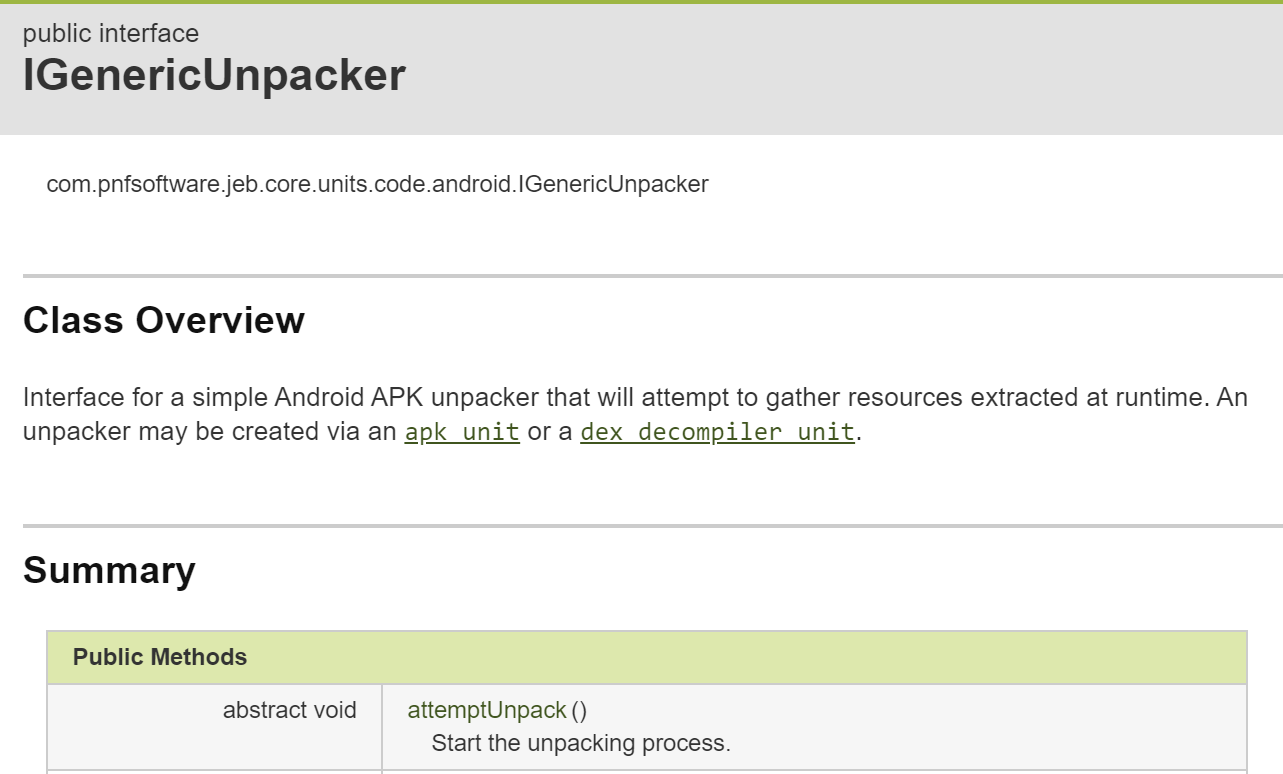
Generic Unpacking For Apk Jeb In Action This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. This post presents one of jeb components used for android app reverse engineering: the generic unpacker for apk. 1 the unpacker will attempt to emulate the app’s execution in order to collect dex files and native libraries (so files, arm64 only) that would be dynamically generated at runtime. A (hopefully) generic unpacker for packed android apps. checkpointsw android unpacker. 本课时我们就来介绍一下逆向相关的操作,通过逆向操作获得 apk 反编译后的代码,然后追踪这个 token 的生成逻辑是怎样的,最后我们再用代码把这个逻辑实现出来。 app 逆向其实多数情况下就是反编译得到 app 的源码,然后从源码里面找寻特定的逻辑,本课时就来演示一下 app 的反编译和入口点查找操作。 在这里我们使用的逆向工具叫作 jeb。 jeb 是一款专业的安卓应用程序的反编译工具,适用于逆向和审计工程,功能非常强大,可以帮助逆向人员节省很多逆向分析时间。 利用这个工具我们能方便地获取到 apk 的源码信息,逆向一个 apk 不在话下。. For a project, i needed to decompile programmatically certain classes from an android apk file. usually this is done by first extracting the dex file using apktool, then converting it to a jar file using dex2jar, and finally decompiling it using tools like jad or cfr. Procedure for decoding .apk files, step by step method: make a new folder and copy over the .apk file that you want to decode. now rename the extension of this .apk file to .zip (rename from filename.apk to filename.zip) and save it. now you can access the classes.dex files.
Comments are closed.