Gal Braun Malware Representation Using Graphs

Malware Detection And Classification Based On Graph Convolutional In this talk, i’ll show how to use graphs to represent malware and how to use graph embeddings and gcn (graph convolutional networks) to tackle such tasks as malware classification and. In this talk, i’ll show how to use graphs to represent malware and how to use graph embeddings and gcn (graph convolutional networks) to tackle such tasks as malware classification and detection, to help security researchers do their job in a faster and more efficient way.

Malware Representation Using Graphs In this talk, i’ll show how to use graphs to represent malware and how to use graph embeddings and gcn (graph convolutional networks) to tackle such tasks as malware classification and detection, to help security researchers do their job in a faster and more efficient way. In this talk, i’ll show how to use graphs to represent malware and how to use graph embeddings and gcn (graph convolutional networks) to tackle such tasks as malware classification and detection, to help security researchers do their job in a faster and more efficient way. Thus, we developed a malware detection and classification method using a graph neural network (gnn) and deep learning. important behavioral features of the malware and malware variants were determined using a developed model with gcn, and the malware and their variants were classified. The dataset represented a diverse range of malware categories, including backdoors, worms, packed malware, potentially unwanted programs (pups), trojans, and other variants.

Gal Braun Posted On Linkedin Thus, we developed a malware detection and classification method using a graph neural network (gnn) and deep learning. important behavioral features of the malware and malware variants were determined using a developed model with gcn, and the malware and their variants were classified. The dataset represented a diverse range of malware categories, including backdoors, worms, packed malware, potentially unwanted programs (pups), trojans, and other variants. By integrating these components, this survey demonstrates how graph learning and explainability contribute to building robust, interpretable, and scalable malware detection systems. Our paper focuses on analyzing recent research studies based on such methods for malware detection, starting from the extraction of graph structured data using reverse engineering tools, to the classification of malware based on graph embeddings. In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. The results show that a combination of reordering malware sections and injecting random data can improve the overall performance of the classification. all the code is publicly available.

Gal Braun Labscon By integrating these components, this survey demonstrates how graph learning and explainability contribute to building robust, interpretable, and scalable malware detection systems. Our paper focuses on analyzing recent research studies based on such methods for malware detection, starting from the extraction of graph structured data using reverse engineering tools, to the classification of malware based on graph embeddings. In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. The results show that a combination of reordering malware sections and injecting random data can improve the overall performance of the classification. all the code is publicly available.
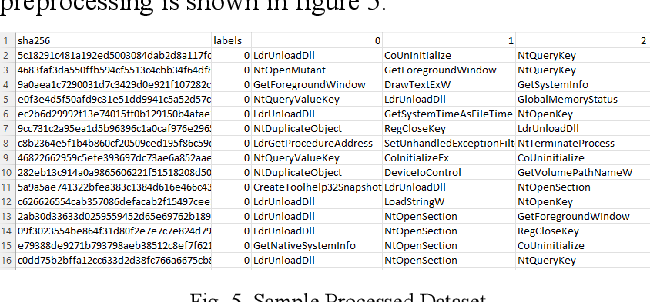
Figure 5 From Malware Detection Using Control Flow Graphs Semantic In this research, we treat malware classification as a graph classification problem. based on local degree profile features, we train a wide range of graph neural network (gnn) architectures to generate embeddings which we then classify. The results show that a combination of reordering malware sections and injecting random data can improve the overall performance of the classification. all the code is publicly available.
Comments are closed.