Fuzzing Stack Overflow Perl Msf Spike
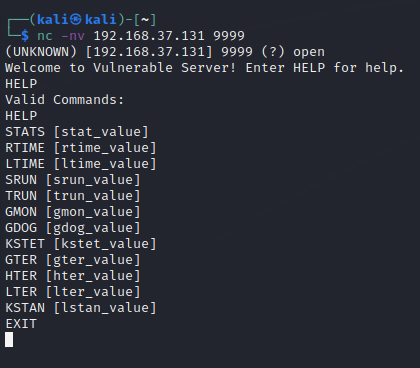
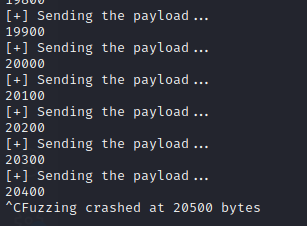
Buffer Overflow Steps Spiking Fuzzing Simple fuzzing excercise on vulnerserver to show funzzing and shellcoding using perl and msf framework. Before you attempt to spike, you're going to want to find an executable file. in the instance of vulnserver, you will download the file. in a realistic scenario, you're going to want to perform enumeration methodology and look for an executable file to download.
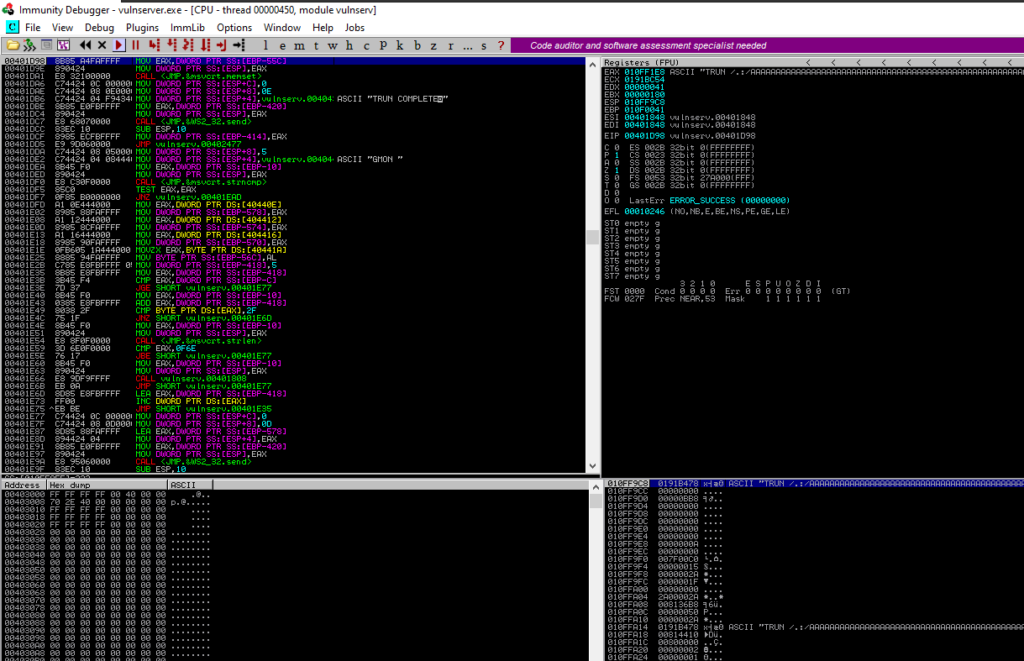
Buffer Overflow Steps Spiking Fuzzing In this article, we will understand and perform spiking and fuzzing in detail. before proceeding, disable defender’s real time protection so we don’t face issues during the process. Part 1: spiking and fuzzing in this first part, we’re aiming to make the application crash by sending data to a specific input variable. When you need to analyze a new network protocol for buffer overflows or similar weaknesses, the spike is the tool of choice for professionals. while it requires a strong knowledge of c to use, it produces results second to none in the field. Spike is an api that enables the hacker security researcher to quickly develop protocol stress tests. since many protocols are built around similar data primitives, spike enables us to create those primitives and then vary them in ways that will hopefully crash the protocol or application.
Buffer Overflow Steps Spiking Fuzzing When you need to analyze a new network protocol for buffer overflows or similar weaknesses, the spike is the tool of choice for professionals. while it requires a strong knowledge of c to use, it produces results second to none in the field. Spike is an api that enables the hacker security researcher to quickly develop protocol stress tests. since many protocols are built around similar data primitives, spike enables us to create those primitives and then vary them in ways that will hopefully crash the protocol or application. @nevilad it is present in spike.h. i don't include, but when i did i got an error about permission. it worked perfectly in this way two weeks ago. Buffer overflow steps 1. fuzzing parameters 2. controlling eip 3. identifying bad characters 4. finding a return instruction. Previously we looked at fuzzing an imap server in the simple imap fuzzer section. at the end of that effort we found that we could overwrite eip, making esp the only register pointing to a memory location under our control (4 bytes after our return address). This will allow us to overflow the buffer, but it wont jump yet because we have not given it anywhere to jump. it will hit the break point and await further instructions.
Buffer Overflow Steps Spiking Fuzzing @nevilad it is present in spike.h. i don't include, but when i did i got an error about permission. it worked perfectly in this way two weeks ago. Buffer overflow steps 1. fuzzing parameters 2. controlling eip 3. identifying bad characters 4. finding a return instruction. Previously we looked at fuzzing an imap server in the simple imap fuzzer section. at the end of that effort we found that we could overwrite eip, making esp the only register pointing to a memory location under our control (4 bytes after our return address). This will allow us to overflow the buffer, but it wont jump yet because we have not given it anywhere to jump. it will hit the break point and await further instructions.

Buffer Overflow Steps Spiking Fuzzing Previously we looked at fuzzing an imap server in the simple imap fuzzer section. at the end of that effort we found that we could overwrite eip, making esp the only register pointing to a memory location under our control (4 bytes after our return address). This will allow us to overflow the buffer, but it wont jump yet because we have not given it anywhere to jump. it will hit the break point and await further instructions.
Buffer Overflow Steps Spiking Fuzzing
Comments are closed.