Framework For Zero Trust Architecture Security Ppt Example

Zero Trust Architecture Pdf Computer Security Security Zero trust architecture detailed presentation free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. The topics discussed in these slides are access identities, execution security policy, threat assessment. this is an immediately available powerpoint presentation that can be conveniently customized.
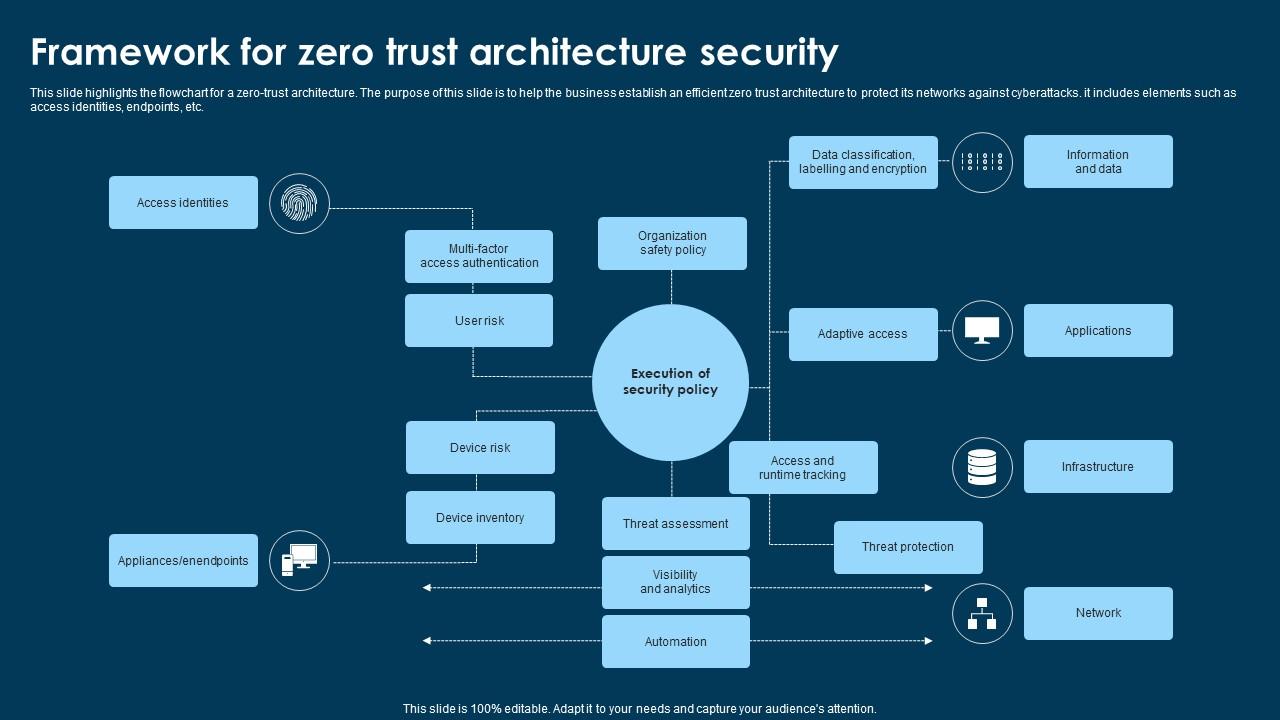
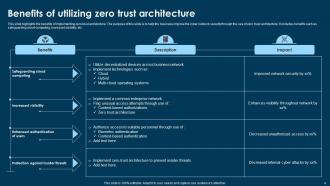
Framework For Zero Trust Architecture Security Ppt Example This document discusses zero trust security and how to implement a zero trust network architecture. it begins with an overview of zero trust and why it is important given limitations of traditional perimeter based networks. Zero trust architecture (zta) powerpoint is a cybersecurity model that requires strict identity verification for every user and device accessing resources. Download our zero trust architecture template for powerpoint and google slides to describe how this cybersecurity model helps improve security posture and protect from costly breaches. Contribute to hasecuritysolutions presentations development by creating an account on github.

Zero Trust Architecture Presentation Free To Download Download our zero trust architecture template for powerpoint and google slides to describe how this cybersecurity model helps improve security posture and protect from costly breaches. Contribute to hasecuritysolutions presentations development by creating an account on github. Fully automated data tagging via ml ai data rights management (drm) discovery & baselining security and information event management (siem) machine learning api standards incident response. Implementing a zero trust access model should be a core component of an organization’s security transformation. using multiple clouds for corporate applications – be it private, public or hybrid, can reduce costs, enable flexibility, and accelerate digital transformation. This slide compares the two security models, such as zero trust network architecture and secure access service edge. the purpose of this slide is to highlight the difference between ztna and sase based on definition, key features, deployment, use cases, benefits and challenges. This illustration shows the set of zero trust identity and device access policies for three levels of protection: starting point, enterprise, and specialized security.

Zero Trust Architecture Powerpoint Ppt Template Bundles Ppt Template Fully automated data tagging via ml ai data rights management (drm) discovery & baselining security and information event management (siem) machine learning api standards incident response. Implementing a zero trust access model should be a core component of an organization’s security transformation. using multiple clouds for corporate applications – be it private, public or hybrid, can reduce costs, enable flexibility, and accelerate digital transformation. This slide compares the two security models, such as zero trust network architecture and secure access service edge. the purpose of this slide is to highlight the difference between ztna and sase based on definition, key features, deployment, use cases, benefits and challenges. This illustration shows the set of zero trust identity and device access policies for three levels of protection: starting point, enterprise, and specialized security.
Zero Trust Architecture Powerpoint Ppt Template Bundles Ppt Template This slide compares the two security models, such as zero trust network architecture and secure access service edge. the purpose of this slide is to highlight the difference between ztna and sase based on definition, key features, deployment, use cases, benefits and challenges. This illustration shows the set of zero trust identity and device access policies for three levels of protection: starting point, enterprise, and specialized security.

Zero Trust Architecture Powerpoint Ppt Template Bundles Ppt Template
Comments are closed.