Four Levels Of Data Encryption
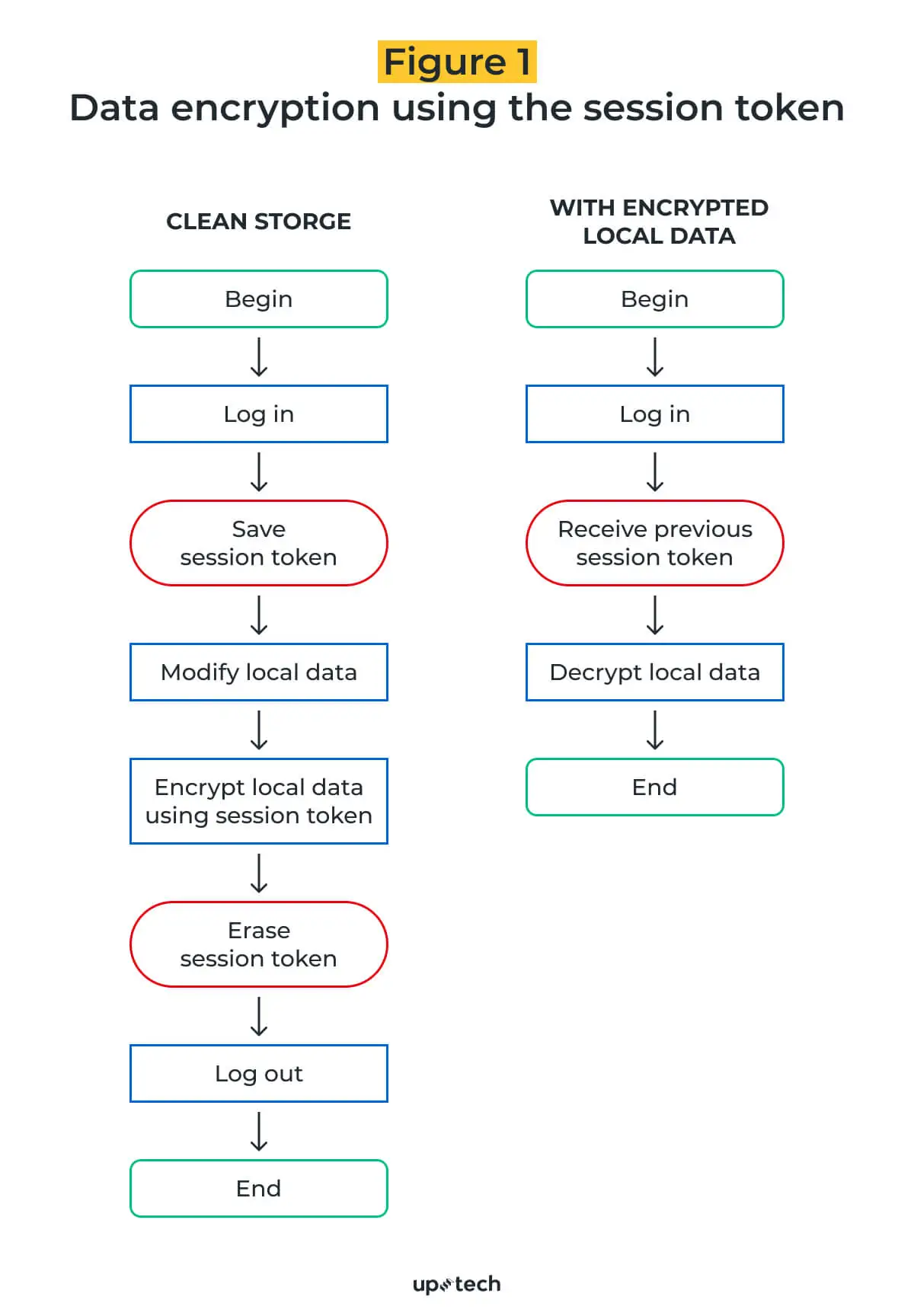
4 Levels Of Data Encryption You Need To Know Here are the different types of encryptions that can be deployed at various levels. 1. link level encryption. a network comprises multiple links interconnected to facilitate data transmission. link level encryption (lle) ensures data privacy by offering encryption across different links. Which data encryption solution best meets your requirements full disk or media, file system, database, and application? break it out by where it's employed in the tech stack.

Data Encryption Vector Infographic In Minimal Outline Style Stock Encryption can be performed at four levels: application level encryption —data is encrypted by the application that modifies or generates the data, before it is written to the database. this makes it possible to customize the encryption process for each user, based on user roles and permissions. The triple data encryption standard (des), often written 3des, is a version of the original des encryption algorithm that encrypts data three times. the triple des uses three 64 bit keys, so the key length is 192 bits. Data encryption keeps our personal, business, health and banking data online. but how is it really kept secure?. In this guide, we’ll break down 11 types of data encryption, explain how each algorithm works, compare their pros, and cons, and show how extending encryption with in line data protection helps maintain compliance, governance, and visibility everywhere your data flows.
What Are The Different Levels Of Data Encryption 1centre Data encryption keeps our personal, business, health and banking data online. but how is it really kept secure?. In this guide, we’ll break down 11 types of data encryption, explain how each algorithm works, compare their pros, and cons, and show how extending encryption with in line data protection helps maintain compliance, governance, and visibility everywhere your data flows. Below, i'll go through some types of encryptions, share the leading encryption algorithms and explain why symmetric encryption remains a reliable method for secure data exchange. If you do not know where all of your sensitive data resides then you might choose to broadly encrypt all data at rest with data set encryption and full disk & tape encryption. Unlock the future of cybersecurity—aes, rsa, ecc, and post quantum encryption explained with zero fluff, pure tech value. Data encryption is a method of converting data into a form that is unreadable by unauthorized users. it’s a crucial component of cybersecurity, protecting sensitive information from being.
What Are The Different Levels Of Data Encryption 1centre Below, i'll go through some types of encryptions, share the leading encryption algorithms and explain why symmetric encryption remains a reliable method for secure data exchange. If you do not know where all of your sensitive data resides then you might choose to broadly encrypt all data at rest with data set encryption and full disk & tape encryption. Unlock the future of cybersecurity—aes, rsa, ecc, and post quantum encryption explained with zero fluff, pure tech value. Data encryption is a method of converting data into a form that is unreadable by unauthorized users. it’s a crucial component of cybersecurity, protecting sensitive information from being.
Data Encryption In Data Encryption Examples Xncuc Unlock the future of cybersecurity—aes, rsa, ecc, and post quantum encryption explained with zero fluff, pure tech value. Data encryption is a method of converting data into a form that is unreadable by unauthorized users. it’s a crucial component of cybersecurity, protecting sensitive information from being.
Data Encryption Advanced Algorithms On Android Devices
Comments are closed.