Forcepoint Gadget Access

Products Gadget Access Forcepoint one is one console with many solutions. from one platform, gain visibility, control access and protect data on all devices. give access to only the apps a user needs rather than the entire network. This setup overview covers setting up private access, configuring private applications, and enabling remote access from your cloud security gateway or standalone users.

Forcepoint Gadget Access Enable secure, scalable remote access to internal and private cloud applications—no vpn required—using a zero trust approach to ensure data protection and operational efficiency. Create account get these benefits when you log into forcepoint support: a personalized support experience for the products and versions you own. access to thousands of knowledge base articles which are updated daily. create cases quickly online. collaborate with forcepoint customers and partners in online community groups. Single set of login policies for controlling access to web, cloud, or private applications based on user location, device type, device posture, user behavior, and user group. Flexera corporate software inspector flexera software vulnerability manager flexera vulnerability intelligence manager forcepoint globalscape guardicore hackhunter.

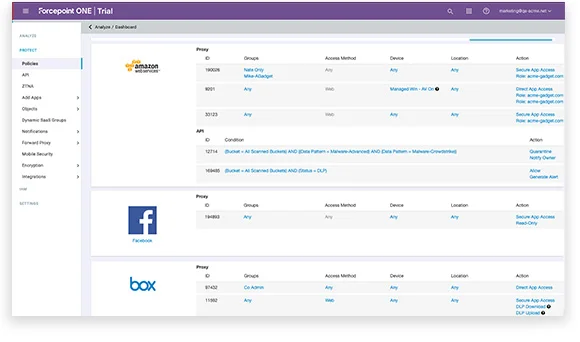
Forcepoint Gadget Access Single set of login policies for controlling access to web, cloud, or private applications based on user location, device type, device posture, user behavior, and user group. Flexera corporate software inspector flexera software vulnerability manager flexera vulnerability intelligence manager forcepoint globalscape guardicore hackhunter. Forcepoint’s zero trust application control enforces strict security policies, ensuring that only authenticated and authorized users and devices can access sensitive applications and resources. Forcepoint offers security appliances with an operating system optimized for analyzing web and email traffic and content. if you have purchased an appliance based solution, the security manager enables you to view details of and easily access multiple appliances. Based on the fact that we may not trust the device, we set a rule in place to allow forcepoint one to secure the web traffic while accessing from that device, applying any dlp policies that we have defined. The article provides an overview of forcepoint endpoint agents f1a, neo, f1e, and smartedge agent, including their functions, installation methods, server requirements, and compatibility.
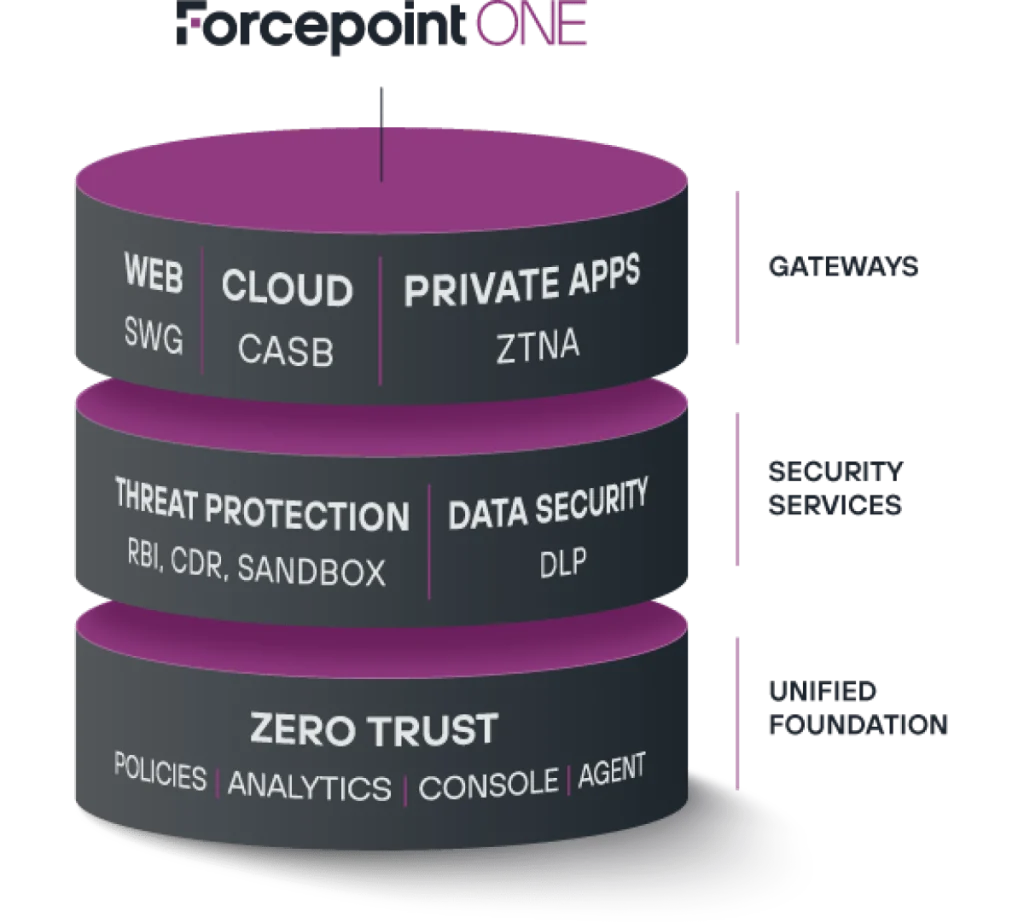
Forcepoint Gadget Access Forcepoint’s zero trust application control enforces strict security policies, ensuring that only authenticated and authorized users and devices can access sensitive applications and resources. Forcepoint offers security appliances with an operating system optimized for analyzing web and email traffic and content. if you have purchased an appliance based solution, the security manager enables you to view details of and easily access multiple appliances. Based on the fact that we may not trust the device, we set a rule in place to allow forcepoint one to secure the web traffic while accessing from that device, applying any dlp policies that we have defined. The article provides an overview of forcepoint endpoint agents f1a, neo, f1e, and smartedge agent, including their functions, installation methods, server requirements, and compatibility.
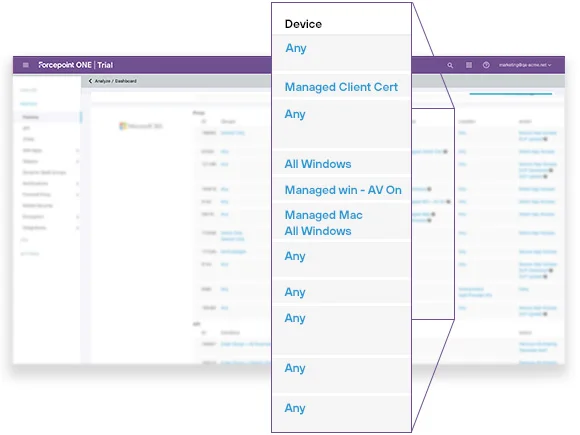
Forcepoint Gadget Access Based on the fact that we may not trust the device, we set a rule in place to allow forcepoint one to secure the web traffic while accessing from that device, applying any dlp policies that we have defined. The article provides an overview of forcepoint endpoint agents f1a, neo, f1e, and smartedge agent, including their functions, installation methods, server requirements, and compatibility.
Forcepoint Gadget Access
Comments are closed.