Fixing A Memory Forensics Blind Spot Linux Kernel Tracing

Black Hat Talk Fixing A Memory Forensics Blind Spot Linux Kernel In this paper, we document the internal data structures and algorithms of these tracing features along with new memory forensic techniques that can analyze the various tracing subsystems. To close this gap, we developed new memory forensic techniques that can analyze the various tracing subsystems and report on potential abuses.
Linux Kernel Tracing Pdf Final run showed 5,191 of the 5,368 (96.3%) of the kernels had all features the few still missing are an ubuntu variant (kvm) that would not be seen in normal production environments. Unfortunately, these research efforts have not adequately kept pace with advances in linux kernel development, leaving blind spots for attackers to remain undetected. in this presentation,. Explore a critical defensive research gap in linux memory forensics through this 25 minute black hat conference talk. delve into the efforts to address a significant blind spot in the linux kernel's tracing infrastructure, which has implications for server and cloud instance security. Richard iii, "every step you take, i'll be tracking you: forensic analysis of the tile tracker application," proceedings of the 2023 digital forensics research conference (dfrws 2023), july 2023.
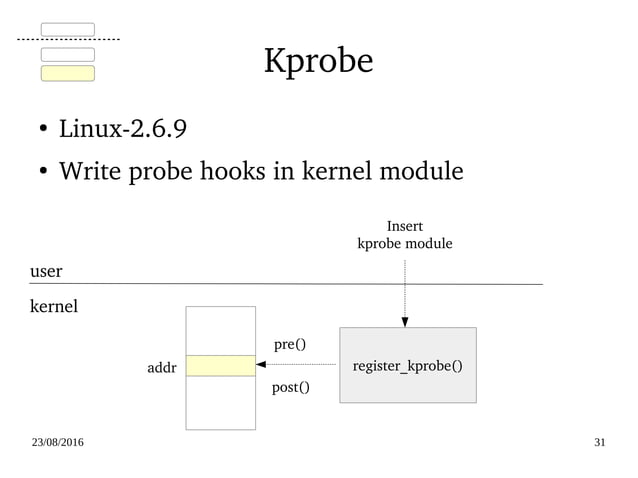
Linux Kernel Tracing Pdf Explore a critical defensive research gap in linux memory forensics through this 25 minute black hat conference talk. delve into the efforts to address a significant blind spot in the linux kernel's tracing infrastructure, which has implications for server and cloud instance security. Richard iii, "every step you take, i'll be tracking you: forensic analysis of the tile tracker application," proceedings of the 2023 digital forensics research conference (dfrws 2023), july 2023. Tracing in the linux kernel is a powerful mechanism that allows developers and system administrators to analyze and debug system behavior. this guide provides documentation on various tracing frameworks and tools available in the linux kernel. The rootkit employs advanced anti forensics by filtering critical kernel data files such as proc kcore and proc kallsyms to evade memory analysis. analyzing the techniques used by singularity is essential for security developers building next generation kernel defense and edr solutions. Due to the fact that i have been practicing the red vs blue approach for years, the material below will allow you to see the scale of the number of projects, techniques and tactics in the scope of linux kubernetes offensive detection dfir. In kernel trace event api. 1. slab allocation of small objects of unknown type. 2. slab allocation of small objects of known type. 3. page allocation. 4. per cpu allocator activity. 5. external fragmentation. 1. power state switch events.
Comments are closed.