Five Step Process For Zero Trust Implementation
Zero Trust Model Step 2 Choose Zero Trust Implementation On Ramp Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. The five step approach works across your entire enterprise, whether you’re implementing a zero trust strategy in the cloud, on a private network, or on endpoints. the following sections describe each of the five steps and how to accomplish them.

Few Step Framework Towards Zero Trust Implementation Vtech A practical, stage by stage zero trust implementation guide. learn how to move from legacy perimeter security to zero trust without disrupting operations—with real milestones and decision criteria. Implement zero trust with five steps: assess assets, analyze dependencies, design policies, enforce access controls, and continuously monitor for evolving threats. Follow our proven five step roadmap, deployment checklist, and expert faqs to roll out a zero trust security model without derailing operations. We discuss the history of zero trust, the tenets of zero trust, the five step implementation process for zero trust, and its adoption for smart home devices and internet of things, and we provide suggestions for future research.
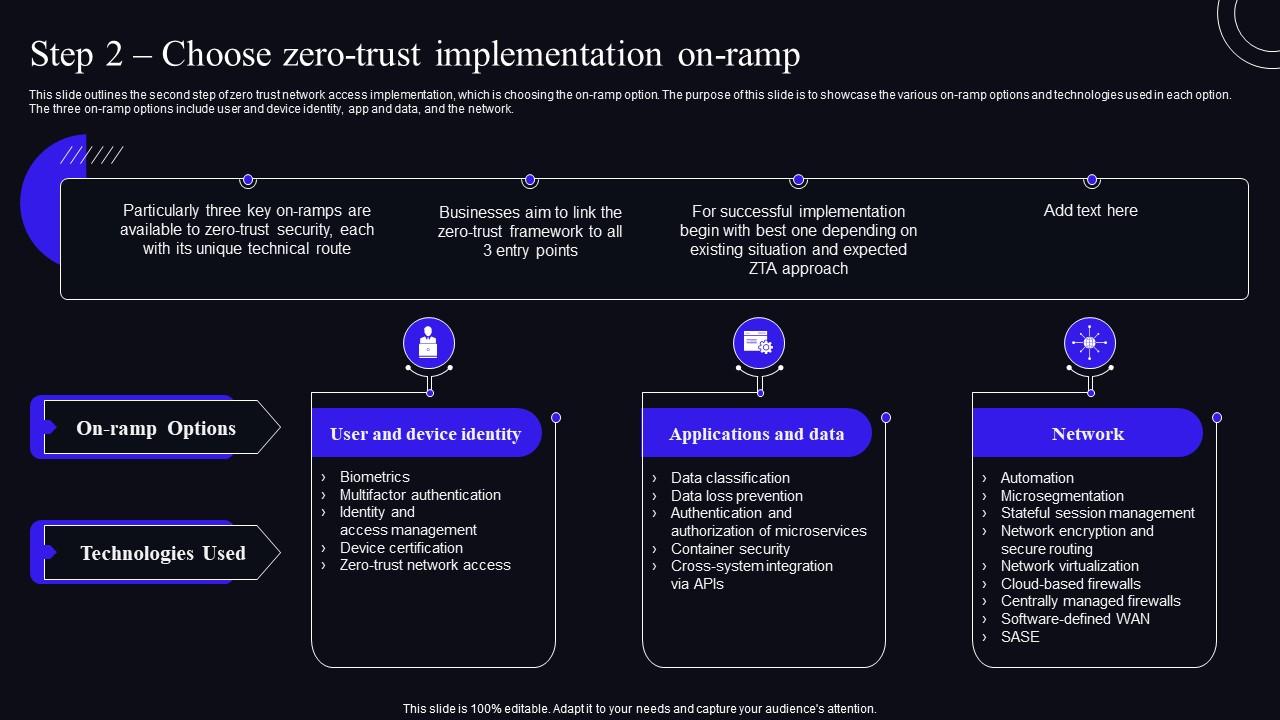
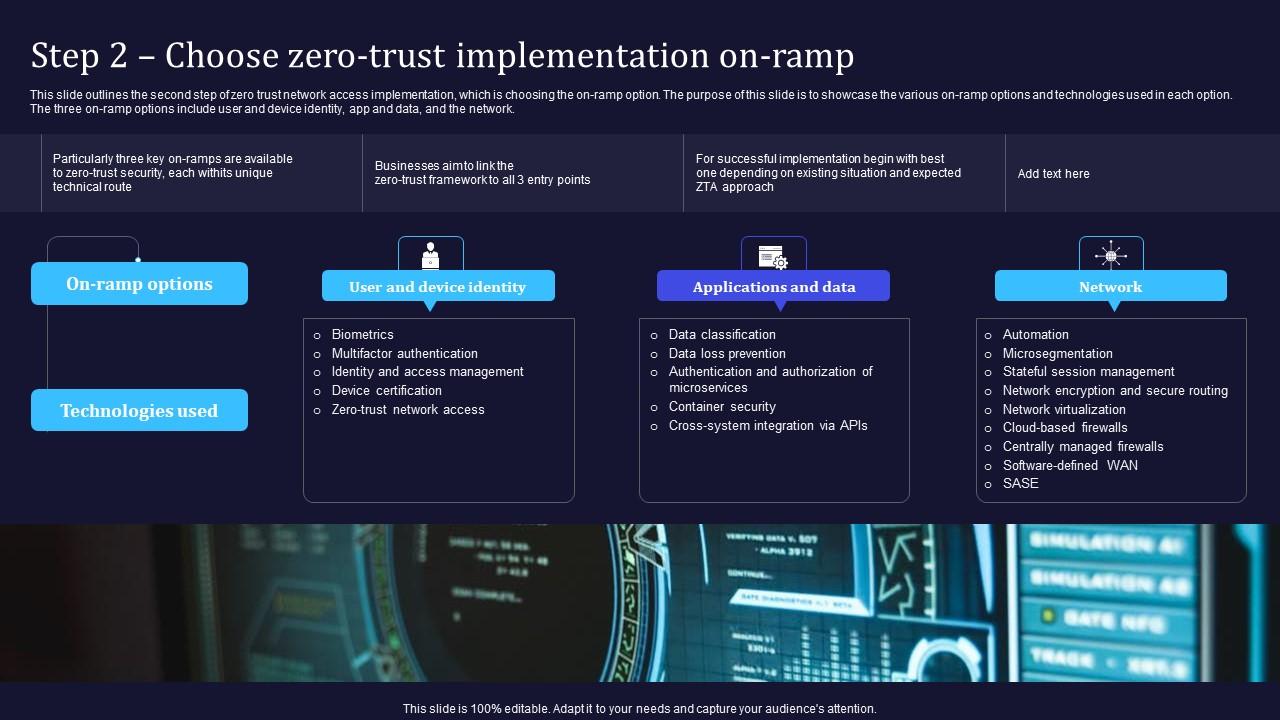
Step 2 Choose Zero Trust Implementation On Ramp Zero Trust Security Follow our proven five step roadmap, deployment checklist, and expert faqs to roll out a zero trust security model without derailing operations. We discuss the history of zero trust, the tenets of zero trust, the five step implementation process for zero trust, and its adoption for smart home devices and internet of things, and we provide suggestions for future research. Below is a guide to a zero trust implementation that government agencies can use to understand how to implement zero trust. Our expert consultants will work with your team to step through the five steps of zero trust implementation to maximize protection for your most valuable assets. Zero trust redefines the security architecture by continuously validating identity, context and risk before access is allowed. cisas zero trust security model outlines five pillars that organizations can focus on during a zero trust implementation. Zero trust implementation typically includes at least five steps, which include adding microsegmentation to the network, adding multi factor authentication, and validating endpoint devices.

How Zero Trust Implementation Reinforces Network Security Below is a guide to a zero trust implementation that government agencies can use to understand how to implement zero trust. Our expert consultants will work with your team to step through the five steps of zero trust implementation to maximize protection for your most valuable assets. Zero trust redefines the security architecture by continuously validating identity, context and risk before access is allowed. cisas zero trust security model outlines five pillars that organizations can focus on during a zero trust implementation. Zero trust implementation typically includes at least five steps, which include adding microsegmentation to the network, adding multi factor authentication, and validating endpoint devices.

Zero Trust Implementation Five Things You Can Do On Day 1 Barracuda Zero trust redefines the security architecture by continuously validating identity, context and risk before access is allowed. cisas zero trust security model outlines five pillars that organizations can focus on during a zero trust implementation. Zero trust implementation typically includes at least five steps, which include adding microsegmentation to the network, adding multi factor authentication, and validating endpoint devices.
Comments are closed.