Firewall Configuration Security Analysis Pdf Port Computer

Ebook Firewall Pdf Pdf Firewall Computing Computer Network Hands on lab windows firewall with advanced security free download as pdf file (.pdf), text file (.txt) or read online for free. this document outlines a hands on lab focused on configuring windows firewall with advanced security to enhance the security of a windows operating system. This project investigates practical firewall configuration strategies using both uncomplicated firewall (ufw) and pfsense. a virtual lab environment was created in virtualbox to simulate real world network conditions.
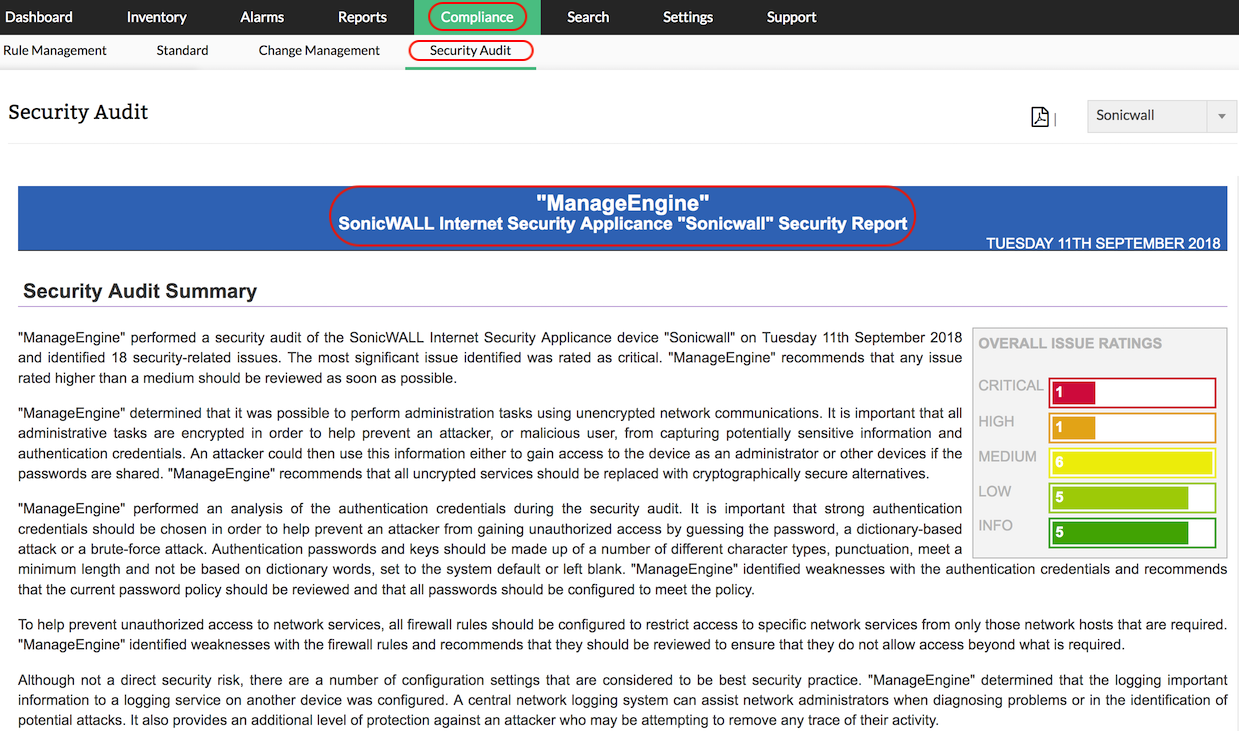
Firewall Security Audit Firewall Rule Configuration Analysis Tool For firewall design, we present two methods for designing stateless firewalls, namely the method of structured firewall design and the method of diverse firewall design, and a model for specifying stateful firewalls. Computer network security plays a crucial role in ensuring the integrity, confidentiality, and availability of data in the modern digital era. one of the primary tools used to safeguard. Port numbers: identify specific applications running on the computer. the most common firewall rules use port numbers to specify the types of application traffic the computer is allowed to send and receive. If a port on a remote host is closed and your computer sends it a syn packet, the remote host will respond back with a rst packet (see lecture 16 for a discussion of this).

Firewall Pdf Firewall Computing Computer Network Port numbers: identify specific applications running on the computer. the most common firewall rules use port numbers to specify the types of application traffic the computer is allowed to send and receive. If a port on a remote host is closed and your computer sends it a syn packet, the remote host will respond back with a rst packet (see lecture 16 for a discussion of this). This book presents scientifically sound and practically useful methods for designing and analyzing firewall policies. this book is useful to a variety of readers. first, it can be used as a handbook for network firewall administrators and network security professionals. Tirta kencana tata warna yang meliputi beberapa perubahan yang meliputi subneting ip address, perubahan desain server, implementasi firewall dengan cara memanfaatkan fitur access list pada router cisco 1600s dan security port pada switch. Since the tunnel traffic is encrypted, firewalls are not able to see what is inside this tunnel and cannot conduct filtering. this topic is covered in detail late in vpn topic. A distributed firewall configuration involves stand alone firewall devices plus host based firewalls working together under a central administrative control. figure 22.5 suggests a distributed firewall configuration.

Panduan Setting Firewall Pdf This book presents scientifically sound and practically useful methods for designing and analyzing firewall policies. this book is useful to a variety of readers. first, it can be used as a handbook for network firewall administrators and network security professionals. Tirta kencana tata warna yang meliputi beberapa perubahan yang meliputi subneting ip address, perubahan desain server, implementasi firewall dengan cara memanfaatkan fitur access list pada router cisco 1600s dan security port pada switch. Since the tunnel traffic is encrypted, firewalls are not able to see what is inside this tunnel and cannot conduct filtering. this topic is covered in detail late in vpn topic. A distributed firewall configuration involves stand alone firewall devices plus host based firewalls working together under a central administrative control. figure 22.5 suggests a distributed firewall configuration.

Computer Firewalls Pdf Proxy Server Firewall Computing Since the tunnel traffic is encrypted, firewalls are not able to see what is inside this tunnel and cannot conduct filtering. this topic is covered in detail late in vpn topic. A distributed firewall configuration involves stand alone firewall devices plus host based firewalls working together under a central administrative control. figure 22.5 suggests a distributed firewall configuration.
Comments are closed.