Finding Exploiting Unusual Api Endpoint Infosec Write Ups

Lab Exploiting An Api Endpoint Using Documentation Infosec Writeups A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters. An application programming interface (api) allows different software systems to communicate with each other by calling features and accessing data. apis make it possible for applications to.
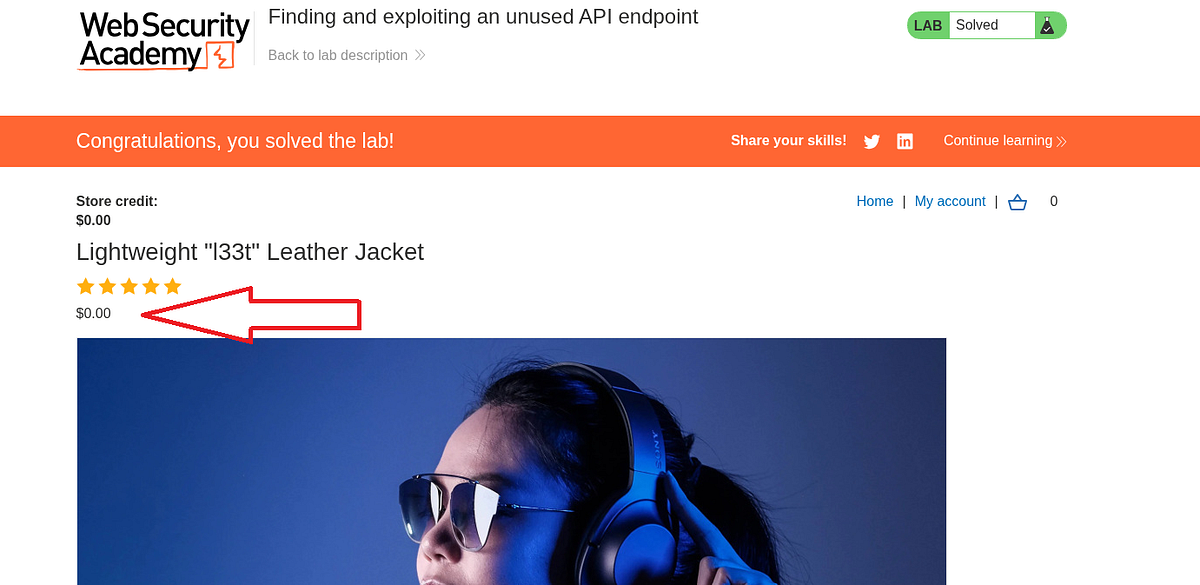
Lab 3 Finding And Exploiting An Unused Api Endpoint Api Testing Required knowledge to solve this lab, you'll need to know: how to use error messages to construct a valid request. how http methods are used by restful apis. how changing the http method can reveal additional functionality. these points are covered in our api testing academy topic. Let’s start by reading the lab description where we have to identify and exploit a hidden api endpoint to buy a product without spending any money. for this, we are provided with a credential pair. We can use burp scanner to crawl the application, then manually investigate interesting attack surface using burp's browser. while browsing the application, look for patterns that suggest api endpoints in the url structure, such as api . also look out for javascript files. To solve the lab, exploit a hidden api endpoint to buy a lightweight l33t leather jacket. you can log in to your own account using the following credentials: wiener:peter.
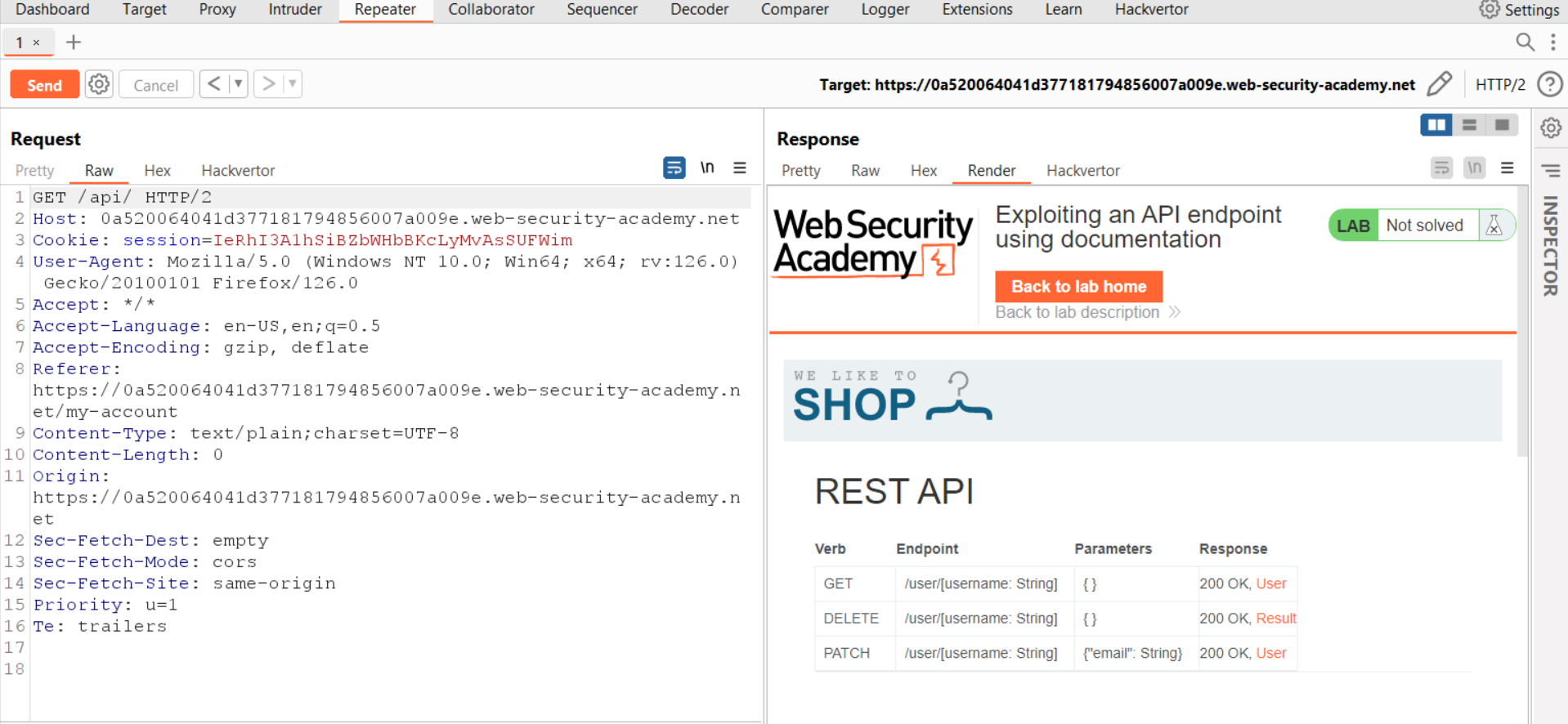
Exploiting An Api Endpoint Using Documentation Cyberiumx We can use burp scanner to crawl the application, then manually investigate interesting attack surface using burp's browser. while browsing the application, look for patterns that suggest api endpoints in the url structure, such as api . also look out for javascript files. To solve the lab, exploit a hidden api endpoint to buy a lightweight l33t leather jacket. you can log in to your own account using the following credentials: wiener:peter. 🚨 new writeup alert! 🚨 "lab: finding and exploiting an unused api endpoint" is published in infosec writeups #hacking #bugbountywriteup #college #cybersecurity. Learn how an exposed and unused api endpoint allowed direct price manipulation in an e commerce application. This lab from portswigger’s web security academy teaches us how to identify and exploit an unused but accessible api endpoint using http method tampering and basic json manipulation. The post provides step by step lab exercises that outline key areas in api security which cover endpoint discovery techniques and the correct handling of http methods along with an evaluation of mass assignment vulnerability threats.

Exploiting An Api Endpoint Using Documentation Cyberiumx 🚨 new writeup alert! 🚨 "lab: finding and exploiting an unused api endpoint" is published in infosec writeups #hacking #bugbountywriteup #college #cybersecurity. Learn how an exposed and unused api endpoint allowed direct price manipulation in an e commerce application. This lab from portswigger’s web security academy teaches us how to identify and exploit an unused but accessible api endpoint using http method tampering and basic json manipulation. The post provides step by step lab exercises that outline key areas in api security which cover endpoint discovery techniques and the correct handling of http methods along with an evaluation of mass assignment vulnerability threats.
Finding Exploiting Unusual Api Endpoint Infosec Write Ups This lab from portswigger’s web security academy teaches us how to identify and exploit an unused but accessible api endpoint using http method tampering and basic json manipulation. The post provides step by step lab exercises that outline key areas in api security which cover endpoint discovery techniques and the correct handling of http methods along with an evaluation of mass assignment vulnerability threats.
Comments are closed.