Find Vulnerable Services Hidden Info Using Google Dorks Tutorial

What Are Google Dorks And How Are Google Hacks Used By leveraging advanced search operators, ethical hackers, bug bounty hunters, and security researchers can uncover hidden information, exposed assets, and potential vulnerabilities on websites without direct interaction. In this article, we will showcase how to effectively use google dorking to uncover hidden and sensitive information on websites.

Google Dorks An Easy Way Of Hacking Cybrary If you own a website or manage sensitive information online, understanding google dorking can help you secure your data. here are some steps you can take to protect yourself:. Google dorking is another way to leverage search engines to discover hidden assets and endpoints to increase your chances of finding vulnerabilities. this article is a guide specifically for beginners with no prior knowledge about using search engines to find exposed files. Google dorking is a technique that uses advanced search operators to find very specific content that ordinarily won't show up with a normal search query. these operators allow you to pinpoint. Whether you're a security professional, a researcher, or simply curious, google dorks can be a powerful tool for uncovering hidden data and potential vulnerabilities on the web.

What Are Google Dorks Google dorking is a technique that uses advanced search operators to find very specific content that ordinarily won't show up with a normal search query. these operators allow you to pinpoint. Whether you're a security professional, a researcher, or simply curious, google dorks can be a powerful tool for uncovering hidden data and potential vulnerabilities on the web. Learn google dorking & osint techniques to uncover hidden data, enhance reconnaissance, and boost your cybersecurity skills. Unlock hidden endpoints and parameters with google dorks. learn how to find exposed access points to uncover vulnerabilities for bug bounty hunting. However, google offers advanced techniques when searching which can offer a treasure trove of hidden and vulnerable services if used correctly. today, we'll introduce you to google. By using specific search strings, you can filter results to uncover sensitive information, hidden webpages, confidential files and more that are publicly accessible but difficult to find.
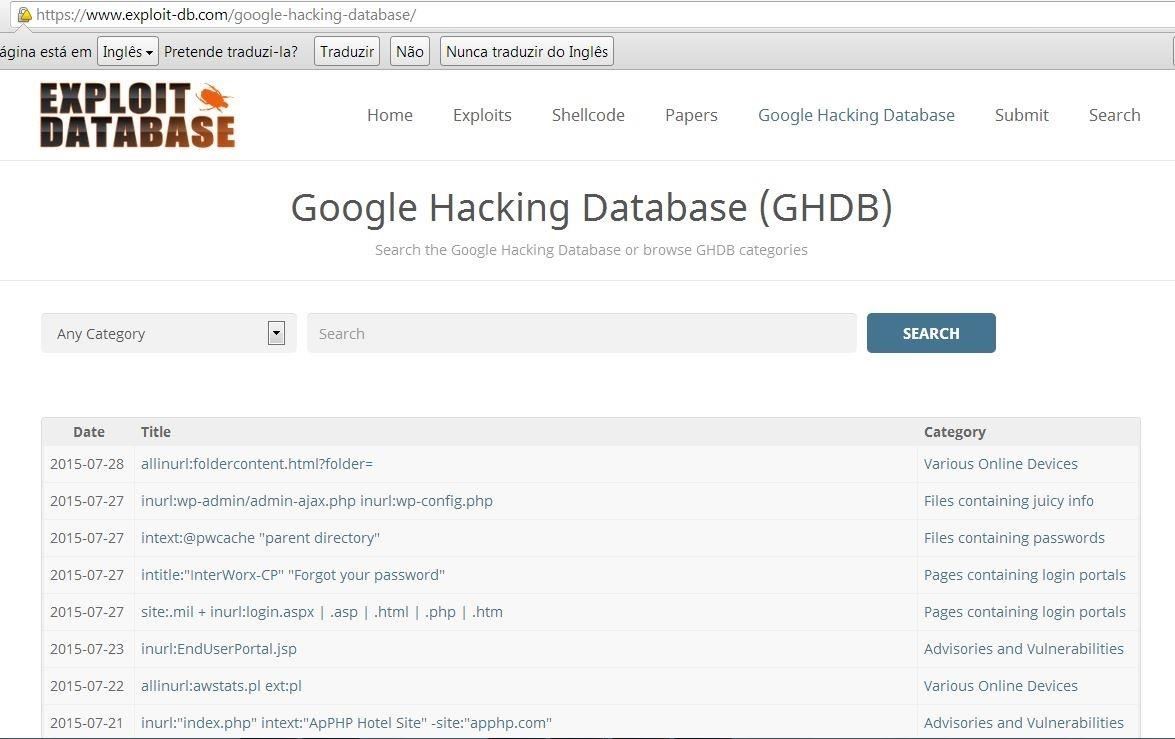
Comment Utiliser Google Hack Googledorks Learn google dorking & osint techniques to uncover hidden data, enhance reconnaissance, and boost your cybersecurity skills. Unlock hidden endpoints and parameters with google dorks. learn how to find exposed access points to uncover vulnerabilities for bug bounty hunting. However, google offers advanced techniques when searching which can offer a treasure trove of hidden and vulnerable services if used correctly. today, we'll introduce you to google. By using specific search strings, you can filter results to uncover sensitive information, hidden webpages, confidential files and more that are publicly accessible but difficult to find.

Find Vulnerable Services Hidden Info Using Google Dorks Tutorial However, google offers advanced techniques when searching which can offer a treasure trove of hidden and vulnerable services if used correctly. today, we'll introduce you to google. By using specific search strings, you can filter results to uncover sensitive information, hidden webpages, confidential files and more that are publicly accessible but difficult to find.
Comments are closed.