Final Ict Disaster Pdf Disaster Recovery Backup

Ict Disaster Recovery Plan Pdf Backup Disaster Recovery Final ict disaster (1) free download as pdf file (.pdf), text file (.txt) or read online for free. It presents practical strategies, methods, and tools to ensure that organizations can recover quickly and effectively from system failures, cyber attacks, or natural disasters.
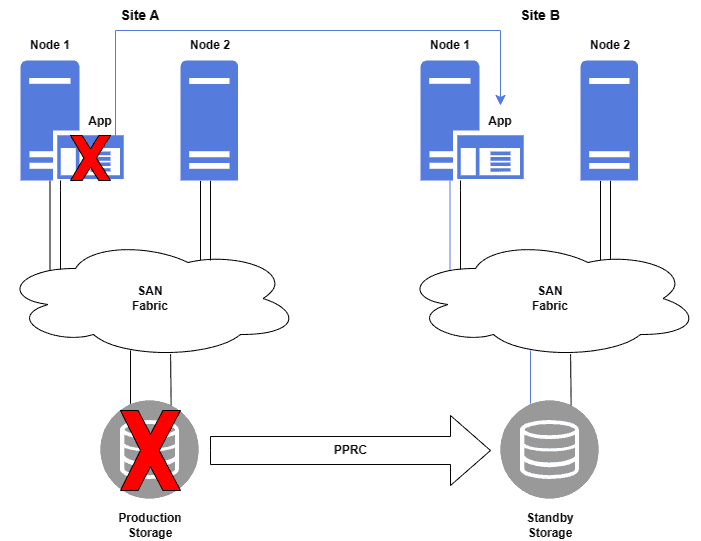
Ict Disaster Recovery Management Resiliex This disaster recovery plan establishes procedures to protect, backup, and restore your organization's critical systems and data in the event of hardware failure, cyberattack, natural disaster, or other disruptions. The fundamental components of the plan, including disaster recovery strategies and procedures, data restoration times, rpos and rtos, data and system backups, and risk management assessments. This disaster recovery plan serves to guide the moe in the recovery and restoration of critical information technology systems in the event of a disaster assuming that the primary site is not recoverable for some time and as such ict services need to be restored to a secondary survived site. Encrypt backup data both in transit and at rest to ensure confidentiality and integrity. perform routine backup verification and recovery testing to confirm data availability. retain backup copies for an appropriate period in line with regulatory and compliance requirements.
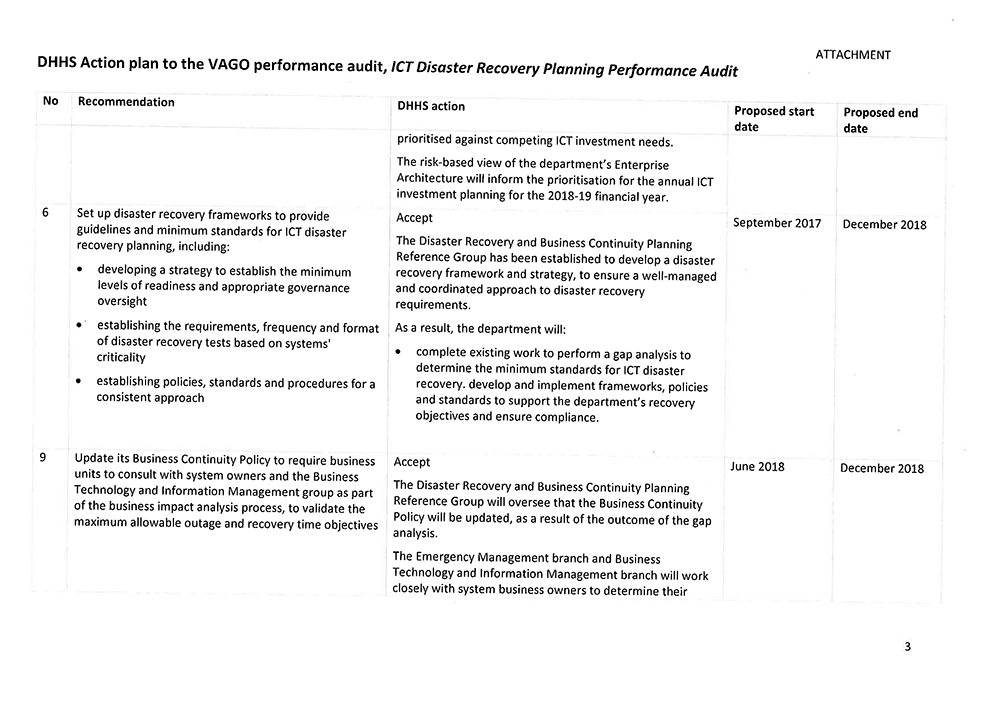
Ict Disaster Recovery Planning Victorian Auditor General S Office This disaster recovery plan serves to guide the moe in the recovery and restoration of critical information technology systems in the event of a disaster assuming that the primary site is not recoverable for some time and as such ict services need to be restored to a secondary survived site. Encrypt backup data both in transit and at rest to ensure confidentiality and integrity. perform routine backup verification and recovery testing to confirm data availability. retain backup copies for an appropriate period in line with regulatory and compliance requirements. Recovering from a disaster is never easy but with the right plan, you can restore your systems — and peace of mind — with as few missteps as possible. avoiding these five common mistakes will help to make your disaster recovery solution a success. This document delineates our policies and procedures for technology disaster recovery as well as data retention and data management. for each process plans for recovering critical technology platforms and infrastructure have been drafted. Each member of the disaster recovery team and the business recovery team will be issued a cd and hard copy of this plan. a master protected copy will be stored on specific resources established for this purpose. key business processes and the agreed backup strategy for each are listed below. Disaster recovery playbook in the immortal words of arthur conan doyle, the creator of sherlock holmes, “it is easy. to be wise after the event.” every it team knows that feeling; the flood or breach or hardware failure has hit and left in its wake a map of actions that shoul.
Differences Between Disaster Recovery And Backup Baeldung On Computer Recovering from a disaster is never easy but with the right plan, you can restore your systems — and peace of mind — with as few missteps as possible. avoiding these five common mistakes will help to make your disaster recovery solution a success. This document delineates our policies and procedures for technology disaster recovery as well as data retention and data management. for each process plans for recovering critical technology platforms and infrastructure have been drafted. Each member of the disaster recovery team and the business recovery team will be issued a cd and hard copy of this plan. a master protected copy will be stored on specific resources established for this purpose. key business processes and the agreed backup strategy for each are listed below. Disaster recovery playbook in the immortal words of arthur conan doyle, the creator of sherlock holmes, “it is easy. to be wise after the event.” every it team knows that feeling; the flood or breach or hardware failure has hit and left in its wake a map of actions that shoul.
Disaster Recovery Solution Webpage Pdf Each member of the disaster recovery team and the business recovery team will be issued a cd and hard copy of this plan. a master protected copy will be stored on specific resources established for this purpose. key business processes and the agreed backup strategy for each are listed below. Disaster recovery playbook in the immortal words of arthur conan doyle, the creator of sherlock holmes, “it is easy. to be wise after the event.” every it team knows that feeling; the flood or breach or hardware failure has hit and left in its wake a map of actions that shoul.

Final Ict Disaster Pdf Disaster Recovery Backup
Comments are closed.