File Upload Vulnerability

5 Ways To File Upload Vulnerability Exploitation Pdf Learn how to test and exploit file upload vulnerabilities including detection, attack methods and bypass techniques. Learn how to exploit file upload functions that lack proper validation and allow users to upload dangerous files, such as server side scripts. find out how to bypass common defenses and create a web shell to take full control of a vulnerable web server.
File Upload Vulnerability Learn how uploaded files can be exploited by attackers to execute code, deface websites, or access sensitive data. find out the risk factors, examples, and protection methods for this vulnerability. In this entry of my cybersecurity learning series, i explored file upload vulnerabilities , a key area in web application security. this session involved testing different techniques used to. A file upload vulnerability occurs when a web application allows users to upload files without properly checking their type, content, or purpose. this security flaw can let attackers upload harmful files like scripts or malware instead of safe files such as images or documents. In this article, we review file upload vulnerabilities. we also detail the exploitations and security best practices for protecting against them.
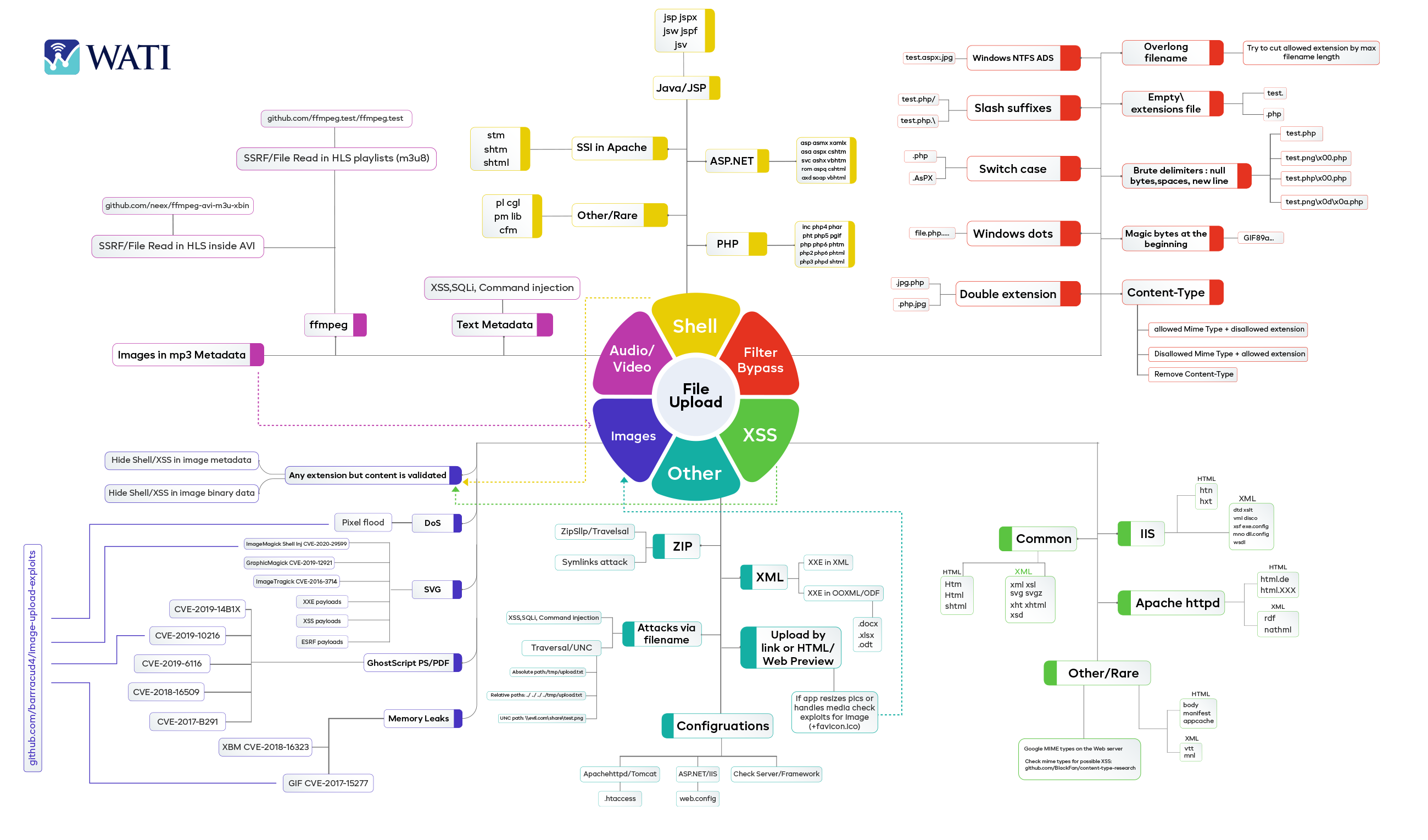
File Upload Vulnerability A file upload vulnerability occurs when a web application allows users to upload files without properly checking their type, content, or purpose. this security flaw can let attackers upload harmful files like scripts or malware instead of safe files such as images or documents. In this article, we review file upload vulnerabilities. we also detail the exploitations and security best practices for protecting against them. Learn about file upload vulnerabilities, arbitrary file upload attacks, mime type bypass techniques, and security best practices. Upload insecure files uploaded files may pose a significant risk if not handled correctly. a remote attacker could send a multipart form data post request with a specially crafted filename or mime type and execute arbitrary code. The ninja forms file uploads plugin for wordpress is vulnerable to arbitrary file uploads due to missing file type validation in the 'nf fu ajax controllers uploads::handle upload' function in all versions up to, and including, 3.3.26. Learn how unrestricted file upload vulnerabilities work, common exploitation techniques like rce and xss, and how to secure your web applications effectively.

File Upload Vulnerability Pptx Learn about file upload vulnerabilities, arbitrary file upload attacks, mime type bypass techniques, and security best practices. Upload insecure files uploaded files may pose a significant risk if not handled correctly. a remote attacker could send a multipart form data post request with a specially crafted filename or mime type and execute arbitrary code. The ninja forms file uploads plugin for wordpress is vulnerable to arbitrary file uploads due to missing file type validation in the 'nf fu ajax controllers uploads::handle upload' function in all versions up to, and including, 3.3.26. Learn how unrestricted file upload vulnerabilities work, common exploitation techniques like rce and xss, and how to secure your web applications effectively.
File Upload Vulnerability How To Prevent Hackers From Exploiting It The ninja forms file uploads plugin for wordpress is vulnerable to arbitrary file uploads due to missing file type validation in the 'nf fu ajax controllers uploads::handle upload' function in all versions up to, and including, 3.3.26. Learn how unrestricted file upload vulnerabilities work, common exploitation techniques like rce and xss, and how to secure your web applications effectively.
Comments are closed.