Figure 4 From Malware Detection Using Control Flow Graphs Semantic
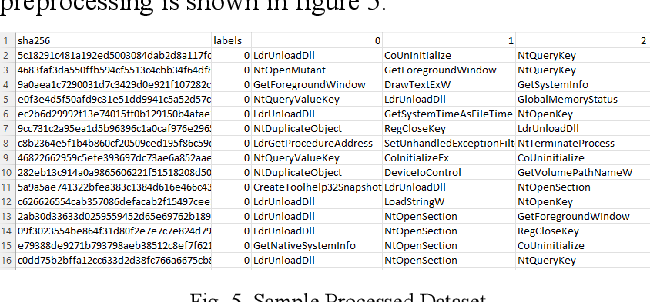
Figure 5 From Malware Detection Using Control Flow Graphs Semantic This survey aims to review some state of the art methods for malware detection through cfgs using ml, focusing on the different ways of extracting, representing, and classifying. Unfortunately, current methods for detecting malware and examining unfamiliar code have notable limitations. to tackle this issue, we propose a system that identifies and analyzes malware by capturing this essential behavior. we generated call flow graphs of the executables in each category.

Cfg Based Malware Detection Methods Pdf Malware Machine Learning In this survey, we aim to review some state of the art methods for malware detection through cfgs using ml, focusing on the different ways of extracting, representing, and classifying. Specifically, we present a comprehensive overview of different types of cfg features used and different ml algorithms applied to cfg based malware detection. Recently, the application of graph representation learning (grl) techniques on graph structured data has demonstrated impressive capabilities in malware detection. In this work, we propose a novel control flow graph (cfg) based malware detection framework using graph convolutional networks (gcns), which can be capable of detecting malware in a more accurate manner.
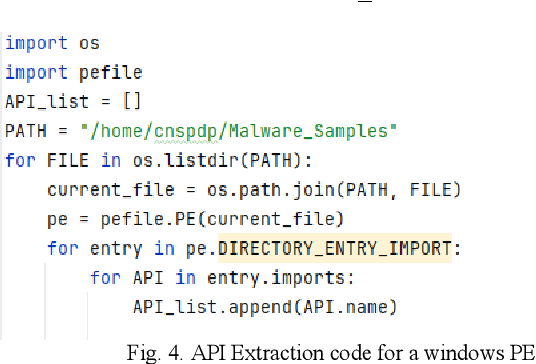
Figure 4 From Malware Detection Using Control Flow Graphs Semantic Recently, the application of graph representation learning (grl) techniques on graph structured data has demonstrated impressive capabilities in malware detection. In this work, we propose a novel control flow graph (cfg) based malware detection framework using graph convolutional networks (gcns), which can be capable of detecting malware in a more accurate manner. The defender is a gnn based malware detection model that takes a control flow graph, derived from disassembling a pe file, as input and outputs the probability that the file is classified. Malware is a significant threat to the security of computer systems and networks, requiring sophisticated techniques to analyze its behavior and functionality f. In this paper, we propose a framework that aims to enhance the performance of gnn based models for malware detection by integrating a graph reduction module into the learning process. To achieve that, we will be classifying applications using control flow graphs and different similarity based methods including k nearest neighbors (knn) as well as random forest classifier to see if different methods can detect certain types of malware or any specific features.
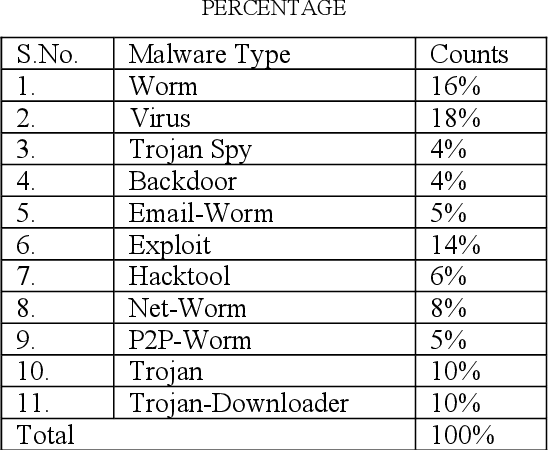
Table Ii From Malware Detection Using Control Flow Graphs Semantic The defender is a gnn based malware detection model that takes a control flow graph, derived from disassembling a pe file, as input and outputs the probability that the file is classified. Malware is a significant threat to the security of computer systems and networks, requiring sophisticated techniques to analyze its behavior and functionality f. In this paper, we propose a framework that aims to enhance the performance of gnn based models for malware detection by integrating a graph reduction module into the learning process. To achieve that, we will be classifying applications using control flow graphs and different similarity based methods including k nearest neighbors (knn) as well as random forest classifier to see if different methods can detect certain types of malware or any specific features.

Pdf Control Flow Graphs As Malware Signatures In this paper, we propose a framework that aims to enhance the performance of gnn based models for malware detection by integrating a graph reduction module into the learning process. To achieve that, we will be classifying applications using control flow graphs and different similarity based methods including k nearest neighbors (knn) as well as random forest classifier to see if different methods can detect certain types of malware or any specific features.
Comments are closed.