Figure 11 Posta Phishing2
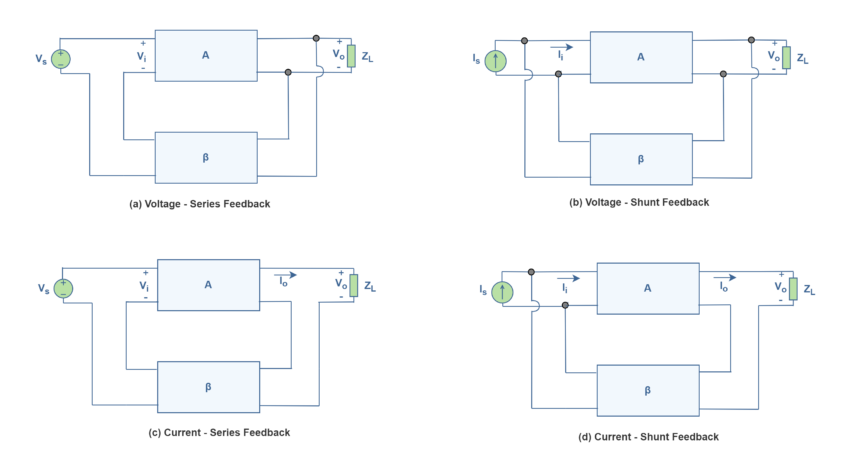
Figure 11 0 Electronics Lab Phishing pot is a collection of real phishing samples collected via honey pots. the purpose of this repository is to provide a reliable database for researchers and developers of detection solutions. pentesters and red teamers: this is not a repository of phishing templates!. Panduan ini berisi langkah langkah yang harus diambil apabila terjadi serangan phishing, yang dimulai dari tahap persiapan sampai dengan tahap pembuatan laporan dari penanganan serangan.

Mesa Posta 11 Renderize Ngan phishing 1. pendahuluan serangan phising adalah serangan yang dilakukan untuk menipu memancing korban agar mau mengklik tautan serta menginput informasi kredential s. perti username dan password. cara kerja phising umumnya dilakukan melalui penggunaan email palsu mengatasnamakan admin, atau melalui situs web palsu yang sangat miri. d. Smishing dan vishing : smishing dan vishing adalah dua bentuk serangan phising yang menggunakan metode komunikasi selain email, yakni sms (smishing) yang memiliki metode penyerang mengirimkan pesan teks ke ponsel korban dengan pesan yang seakan akan berasal dari institute resmi. Embark on a comprehensive journey to explore the fundamentals of phishing analysis, delving into email addresses, delivery mechanisms, headers, body content, and various types of phishing. Phishing is a growing form of cybercrime that poses a serious threat to information security in the digital world. this article aims to analyze the latest trends in phishing attacks and.

Posta2 Embark on a comprehensive journey to explore the fundamentals of phishing analysis, delving into email addresses, delivery mechanisms, headers, body content, and various types of phishing. Phishing is a growing form of cybercrime that poses a serious threat to information security in the digital world. this article aims to analyze the latest trends in phishing attacks and. In this campaign, the html attachment uses various obfuscation techniques and shows an intermediate page before loading the final phishing page. this is the key characteristic of the campaign. Gambar 1.2 halaman phishing bank mandiri sumber: (pt bank mandiri tbk., 2010) kasus phishing marak terjadi pada layanan online bankingpada bank di indonesia. kepala otoritas jasa keuangan mengungkapkan bahwa sejak tahun 2013 pengguna dirugikan rp 100 miliar akibat pencurian kasus "phishing" (pt. kompas cyber media , 2015). pada tahun 2015, dua bank besar di indonesia yaitu bank bca dan bank. Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call. The anatomy, as shown in the figure, illustrates a set of vulnerabilities that the attacker can exploit and the mediums used to conduct the attack.
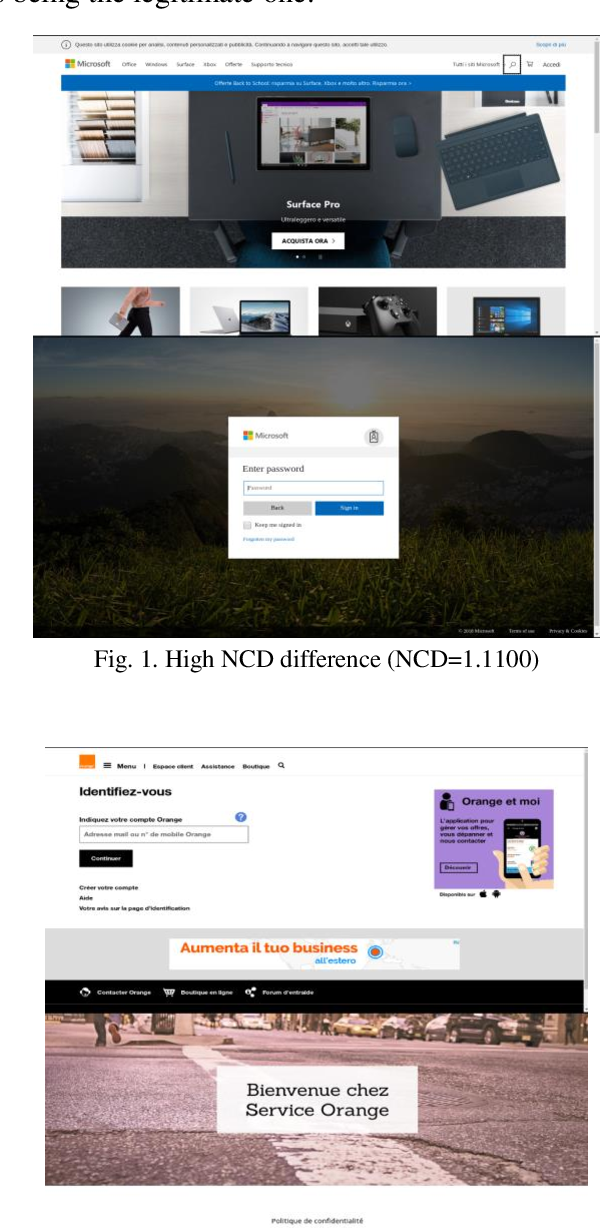
Table 1 From How Phishing Pages Look Like Semantic Scholar In this campaign, the html attachment uses various obfuscation techniques and shows an intermediate page before loading the final phishing page. this is the key characteristic of the campaign. Gambar 1.2 halaman phishing bank mandiri sumber: (pt bank mandiri tbk., 2010) kasus phishing marak terjadi pada layanan online bankingpada bank di indonesia. kepala otoritas jasa keuangan mengungkapkan bahwa sejak tahun 2013 pengguna dirugikan rp 100 miliar akibat pencurian kasus "phishing" (pt. kompas cyber media , 2015). pada tahun 2015, dua bank besar di indonesia yaitu bank bca dan bank. Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call. The anatomy, as shown in the figure, illustrates a set of vulnerabilities that the attacker can exploit and the mediums used to conduct the attack.

Beware Of Phishing Mails Id Blog Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call. The anatomy, as shown in the figure, illustrates a set of vulnerabilities that the attacker can exploit and the mediums used to conduct the attack.
Comments are closed.