Figure 1 From A Systematic Analysis Method For 5g Non Access Stratum

Pdf A Systematic Analysis Method For 5g Non Access Stratum Signalling This paper proposes a systematic analysis method for 5g non access stratum signalling security based on formal analysis, which has identified 10 new 5g protocol vulnerabilities, and an improved pki security mechanism targeted at eliminating these vulnerabilities. In this paper, we evaluate the impact of flooding attacks on the performance of 5g slices with different vnf sharing configurations.

Pdf A Systematic Analysis Method For 5g Non Access Stratum Signalling In section iii, we introduce the systematic method used to analyze the security of 5g protocols. section iv presents the vulnerabilities discovered through our method in detail. Abstract publication: ieee access pub date: 2019 doi: 10.1109 access.2019.2937997 bibcode: 2019ieeea 7l5424h full text sources publisher |. It provides free access to secondary information on researchers, articles, patents, etc., in science and technology, medicine and pharmacy. the search results guide you to high quality primary information inside and outside jst. Fig. 1 depicts a simplified 5g network architecture, which consists of user equipment (ue), 5g access network (5g an), 5g core network (5gc) and data network (dn).

Pdf A Systematic Analysis Method For 5g Non Access Stratum Signalling It provides free access to secondary information on researchers, articles, patents, etc., in science and technology, medicine and pharmacy. the search results guide you to high quality primary information inside and outside jst. Fig. 1 depicts a simplified 5g network architecture, which consists of user equipment (ue), 5g access network (5g an), 5g core network (5gc) and data network (dn). In this paper, we provide the first systematic security analysis model for b5g nas protocol under the assumption of network coexistence. we identified 9 protocol vulnerabilities, including one never reported before. this new vulnerability could be exploited to track the target user. In this work, we conduct the first comprehensive investigation of pws security in 5g networks. we demonstrate five practical attacks that may impact the security of 5g based commercial mobile. Hu, x., liu, c., liu, s., you, w., li, y., & zhao, y. (2019). a systematic analysis method for 5g non access stratum signalling security. ieee access, 1–1. doi:10.1109 access.2019.2937997 10.1109 access.2019.2937997. This manuscript presents a summary and analysis of the current state of affairs in 5g protocol security, discussing the main areas that should still be improved further before 5g systems go live.

What Is Difference Between Access Stratum As And Non Access Stratum In this paper, we provide the first systematic security analysis model for b5g nas protocol under the assumption of network coexistence. we identified 9 protocol vulnerabilities, including one never reported before. this new vulnerability could be exploited to track the target user. In this work, we conduct the first comprehensive investigation of pws security in 5g networks. we demonstrate five practical attacks that may impact the security of 5g based commercial mobile. Hu, x., liu, c., liu, s., you, w., li, y., & zhao, y. (2019). a systematic analysis method for 5g non access stratum signalling security. ieee access, 1–1. doi:10.1109 access.2019.2937997 10.1109 access.2019.2937997. This manuscript presents a summary and analysis of the current state of affairs in 5g protocol security, discussing the main areas that should still be improved further before 5g systems go live.
What Is Difference Between Access Stratum As And 45 Off Hu, x., liu, c., liu, s., you, w., li, y., & zhao, y. (2019). a systematic analysis method for 5g non access stratum signalling security. ieee access, 1–1. doi:10.1109 access.2019.2937997 10.1109 access.2019.2937997. This manuscript presents a summary and analysis of the current state of affairs in 5g protocol security, discussing the main areas that should still be improved further before 5g systems go live.
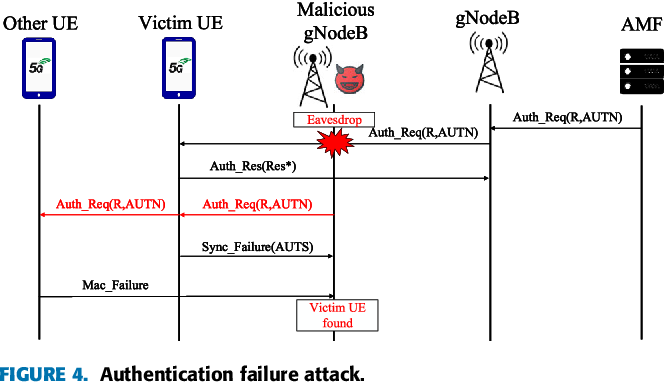
Figure 1 From A Systematic Analysis Method For 5g Non Access Stratum
Comments are closed.