Falco Rules Open Source
Falco Rules Open Source This repository has been created upon this proposal and contains the officially managed falco rules by the falco project, along with the falco rules files registry. The falco organization maintains a rules repository that provides easy to install rules and examples for rule writers. you can learn more about the default and custom rulesets in the documentation.
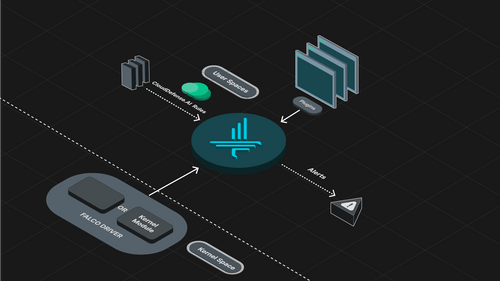
Falco Rules Open Source At its core, falco is a monitoring and detection agent that observes events (such as linux kernel events and other data sources through plugins) and delivers real time alerts based on custom rules. Enter falco, the open source runtime security tool that is purpose built for modern container ecosystems like kubernetes, docker, and cloud native platforms. in this comprehensive guide, we’ll go beyond the basics. Falco is an open source runtime security tool designed for cloud native environments. below are answers to some of the most common questions about using and configuring falco. In this manual, we will explain to you the falco rules, which we can apply in our security checking, the programming and configuration of which will be verbally described.
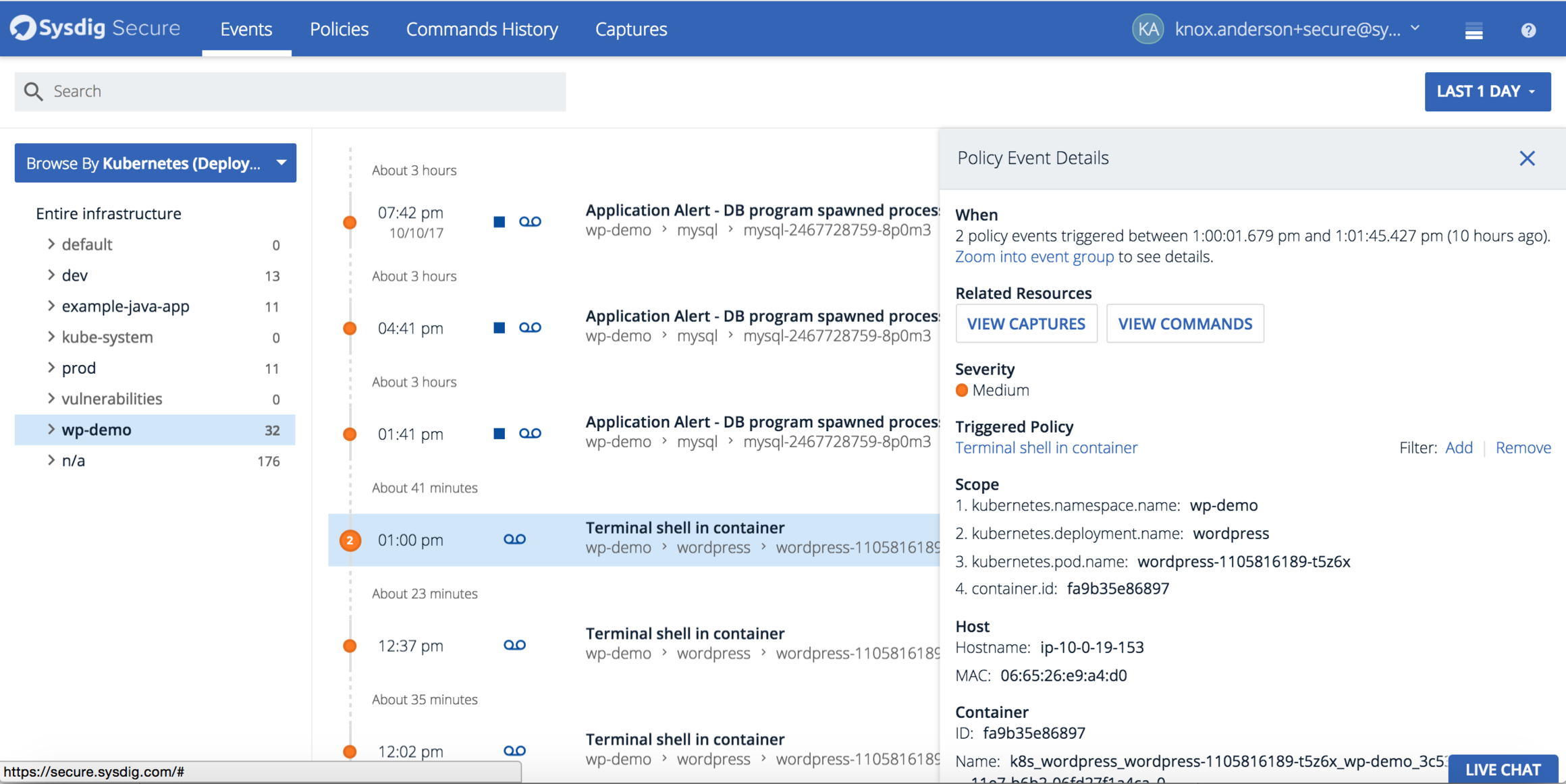
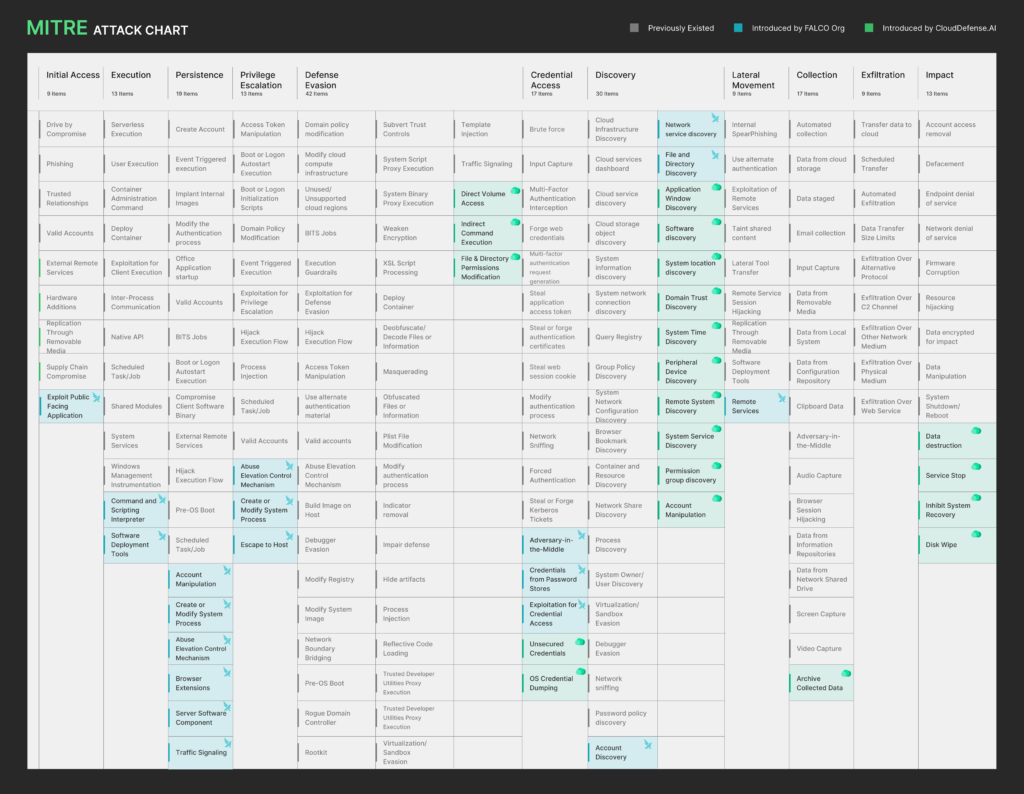
Sysdig Falco Open Source Container Runtime Security Falco is an open source runtime security tool designed for cloud native environments. below are answers to some of the most common questions about using and configuring falco. In this manual, we will explain to you the falco rules, which we can apply in our security checking, the programming and configuration of which will be verbally described. Falco has a rich set of security rules specifically built for kubernetes, linux, and cloud native. if a rule is violated in a system, falco will send an alert notifying the user of the violation and its severity. falco started life as an open source behavioral activity monitoring agent. The registry contains metadata and information about every rule known and recognized by the falcosecurity organization. these rules are developed for falco and made available to the community. Falco is a cloud native security tool that provides runtime security across hosts, containers, kubernetes, and cloud environments. it leverages custom rules on linux kernel events and other data sources through plugins, enriching event data with contextual metadata to deliver real time alerts. A repository of officially managed detection rules for the falco runtime security monitoring system that identifies threats, abnormal behaviors, and compliance violations through syscall and container event analysis.
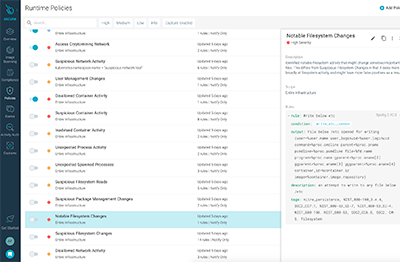
Open Source Container Security Tools Falco Sysdig Falco has a rich set of security rules specifically built for kubernetes, linux, and cloud native. if a rule is violated in a system, falco will send an alert notifying the user of the violation and its severity. falco started life as an open source behavioral activity monitoring agent. The registry contains metadata and information about every rule known and recognized by the falcosecurity organization. these rules are developed for falco and made available to the community. Falco is a cloud native security tool that provides runtime security across hosts, containers, kubernetes, and cloud environments. it leverages custom rules on linux kernel events and other data sources through plugins, enriching event data with contextual metadata to deliver real time alerts. A repository of officially managed detection rules for the falco runtime security monitoring system that identifies threats, abnormal behaviors, and compliance violations through syscall and container event analysis.
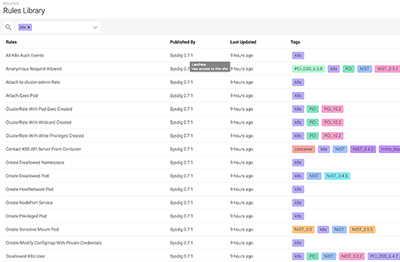
Open Source Container Security Tools Falco Sysdig Falco is a cloud native security tool that provides runtime security across hosts, containers, kubernetes, and cloud environments. it leverages custom rules on linux kernel events and other data sources through plugins, enriching event data with contextual metadata to deliver real time alerts. A repository of officially managed detection rules for the falco runtime security monitoring system that identifies threats, abnormal behaviors, and compliance violations through syscall and container event analysis.
Comments are closed.