Fake Telegram Captcha Forces Users To Run Malicious Powershell Scripts
From Captcha To Catastrophe How Fake Verification Pages Are Spreading Scammers use fake x (formerly twitter) accounts to impersonate the free ross movement and direct users to supposedly official ulbricht telegram channels. after clicking on such a link, victims are prompted to pass a verification test called safeguard captcha. Threat actors on x are exploiting the news around ross ulbricht to direct unsuspecting users to a telegram channel that tricks them into run powershell code that infects them with malware.

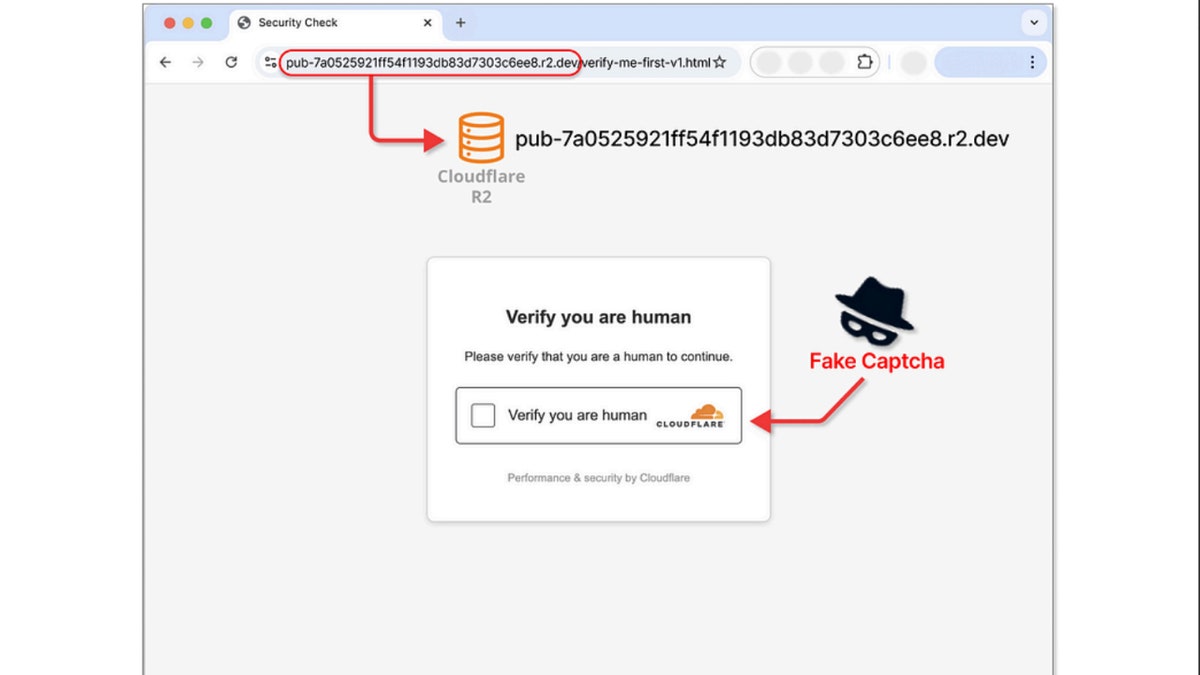
Telegram Captcha Tricks You Into Running Malicious Powershell Scripts Although the bot’s instructions could seem benign, they actually harbor a powershell command that establishes a link to a spiked url and downloads a malicious powershell script. the script then downloads an additional batch of malicious files that propagate the malware on the host system. Cybercriminals are exploiting telegram’s captcha system to trick unsuspecting users into executing malicious powershell scripts, according to cybersecurity experts. this alarming attack targets users by posing as a fake identity verification process, ultimately infecting their devices with malware. A sophisticated malware campaign is targeting windows users through deceptive captcha verification prompts that trick victims into executing malicious powershell scripts. Despite recognizing it as a scam, i decided to investigate further by joining the group to analyze their tactics. upon joining the group, i encountered a verification prompt. after clicking.

Fake Captcha Malware Exploits Windows Users To Run Powershell Commands A sophisticated malware campaign is targeting windows users through deceptive captcha verification prompts that trick victims into executing malicious powershell scripts. Despite recognizing it as a scam, i decided to investigate further by joining the group to analyze their tactics. upon joining the group, i encountered a verification prompt. after clicking. In a recent surge of sophisticated cyberattacks, threat actors have been utilizing fake captcha challenges to trick users into executing malicious powershell commands, leading to malware infections. This campaign demonstrates an evolution from basic fake url based captchas, seen in previous attacks, to a more sophisticated telegram based approach. the primary targets are cryptocurrency communities, where unsuspecting users are deceived into executing malicious scripts. The campaign pairs clearfake with clickfix, a social engineering lure using fake captchas to trick users into executing clipboard delivered commands. its “etherhiding” architecture retrieves payloads from blockchain hosted smart contracts, bypassing static domain blocklists, while a yandex metrika tag (id: 99162160) and smart contract check. Our threat intelligence team discovered an active phishing campaign leveraging fake captcha pages and autohotkey (ahk) droppers to socially engineer users into executing obfuscated powershell commands.

Criminals Exploit Telegram Captcha To Trick Victims Into Installing Malware In a recent surge of sophisticated cyberattacks, threat actors have been utilizing fake captcha challenges to trick users into executing malicious powershell commands, leading to malware infections. This campaign demonstrates an evolution from basic fake url based captchas, seen in previous attacks, to a more sophisticated telegram based approach. the primary targets are cryptocurrency communities, where unsuspecting users are deceived into executing malicious scripts. The campaign pairs clearfake with clickfix, a social engineering lure using fake captchas to trick users into executing clipboard delivered commands. its “etherhiding” architecture retrieves payloads from blockchain hosted smart contracts, bypassing static domain blocklists, while a yandex metrika tag (id: 99162160) and smart contract check. Our threat intelligence team discovered an active phishing campaign leveraging fake captcha pages and autohotkey (ahk) droppers to socially engineer users into executing obfuscated powershell commands.
Comments are closed.