F5 Data Center Firewall Implementation Part 3 Access Control Lists

Chapter 5 Access Control Lists Pdf I Pv6 Router Computing In this video, josh michaels from f5 continues the series on data center firewall implementation, focusing on access control lists (acls). If you also add a network access resource to the policy, you must create and assign acls that allow users access to all the hosts and all parts of the web sites that you want them to access. otherwise, the acl that rejects all connections will stop them.

F5 Data Center Firewall Dg Pdf I Pv6 Computer Network Because l2–7 network firewall security is foundational for information system protection, this deployment guide shows how to implement key policies to protect a typical data center network architecture using big ip with afm and ltm. Apm® access control lists (acls) restrict user access to host and port combinations that are specified in access control entries (aces). an acl can apply to layer 4 (the protocol layer), layer 7 (the application layer), or both. With access policy manager, you configure a resource to allow access to a web application or a network access connection, or you configure an access control list to allow or deny access to clients with network access, web applications, or web access management policies. Host specifies the host name of the access control list entry. location specific specifies whether or not this object contains one or more attributes with values that are specific to the location where the big ip device resides. the location specific attribute is either true or false. when using policy sync,.

11 Access Control Structures Firewalls 06 05 2023 Pdf Security With access policy manager, you configure a resource to allow access to a web application or a network access connection, or you configure an access control list to allow or deny access to clients with network access, web applications, or web access management policies. Host specifies the host name of the access control list entry. location specific specifies whether or not this object contains one or more attributes with values that are specific to the location where the big ip device resides. the location specific attribute is either true or false. when using policy sync,. In this section, we create two data groups, an address data group that contains a list of allowed address, and a string data group that associates the relevant virtual servers to the address group. Network firewall acls are grouped into polices and those policies contain rules or rule lists. rules may include protocol, source address and port, source vlan, destination address and port, schedule, action, and logging. F5 application delivery and security solutions are built to ensure that every app and api deployed anywhere is fast, available, and secure. learn how we can partner to deliver exceptional experiences every time. F5 big ip advanced firewall manager™ (afm) is a high performance icsa certified, stateful, full proxy network firewall designed to guard data centers against incoming threats that enter the network on the most widely deployed protocols—including http s, smtp, dns, sip, and ftp.

Deploying The Big Ip Data Center Firewall Deployment Guide Pdf In this section, we create two data groups, an address data group that contains a list of allowed address, and a string data group that associates the relevant virtual servers to the address group. Network firewall acls are grouped into polices and those policies contain rules or rule lists. rules may include protocol, source address and port, source vlan, destination address and port, schedule, action, and logging. F5 application delivery and security solutions are built to ensure that every app and api deployed anywhere is fast, available, and secure. learn how we can partner to deliver exceptional experiences every time. F5 big ip advanced firewall manager™ (afm) is a high performance icsa certified, stateful, full proxy network firewall designed to guard data centers against incoming threats that enter the network on the most widely deployed protocols—including http s, smtp, dns, sip, and ftp.
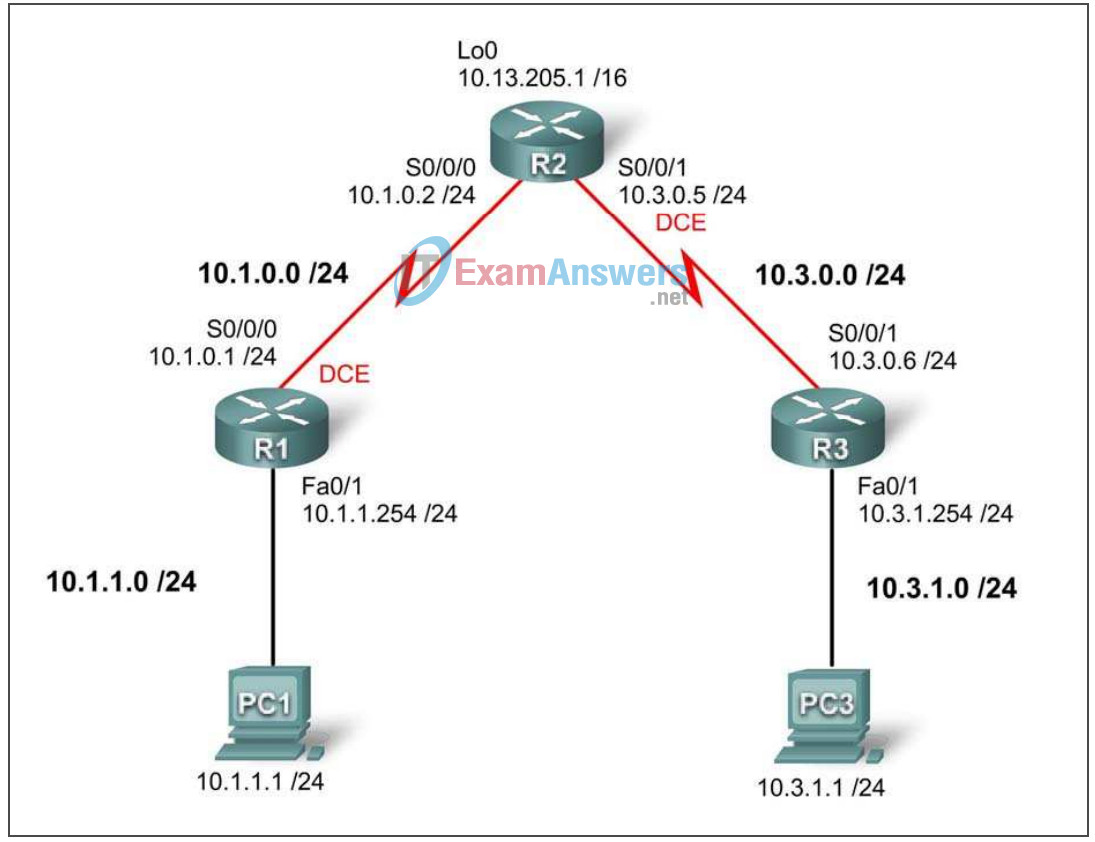
Lab 5 5 3 Troubleshooting Access Control Lists Answers F5 application delivery and security solutions are built to ensure that every app and api deployed anywhere is fast, available, and secure. learn how we can partner to deliver exceptional experiences every time. F5 big ip advanced firewall manager™ (afm) is a high performance icsa certified, stateful, full proxy network firewall designed to guard data centers against incoming threats that enter the network on the most widely deployed protocols—including http s, smtp, dns, sip, and ftp.
Comments are closed.