Extracting A Zip File From A Memory Dump

Memory Dump File Concepts Pdf Computer File Computer Data Storage Extracting a zip file from a memory dump volatility univsthreats 25 ctf forensics ramblings of cornelia more. Dump a process memory and extract data based on regular expressions. tool uses multithreading. dump and inspect a process memory: after logging out from an application. garbage cleaners might not free the unused memory immediately, but should do so after 5 10 minutes after the last action.

A Zip File In The Memory Dump Download Scientific Diagram One of my friends stumbled upon a ctf challenge where he needed to retrieve a .rar file from a memory dump. after some research, i came up with the following solution:. To fix it, replace " o bulk" with " o bulk2". this tells bulk extractor to gather data from the memdump file, put the results in a folder named "bulk", and compile a wordlist of all readable strings. bulk extractor will take several minutes to run and output progress messages, as shown below:. This section explains how to analyze a memory dump before using volatility : extracting files and secrets. We can use "detect it easy (die)" to analyze the executable. once you have saved the compressed (zipped) folder of "detect it easy (die)" into the directory of your choice, extract its contents into that directory. enter the directory of the extracted contents and open detect it easy (die).
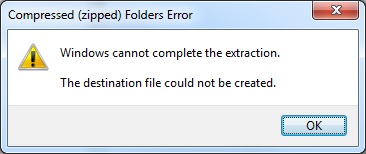
Zip File Not Extracting Why How To Fix It N Quick Solutions This section explains how to analyze a memory dump before using volatility : extracting files and secrets. We can use "detect it easy (die)" to analyze the executable. once you have saved the compressed (zipped) folder of "detect it easy (die)" into the directory of your choice, extract its contents into that directory. enter the directory of the extracted contents and open detect it easy (die). Capture live ram contents with free tool from belkasoft! belkasoft live ram capturer is a tiny free forensic tool that allows to reliably extract the entire contents of computer’s volatile memory—even if protected by an active anti debugging or anti dumping system. Mimikatz can be used to extract various types of user credentials, including plain text passwords, hashes, and kerberos tickets, from windows memory. it enables pass the hash (pth) and pass the ticket (ptt) attacks to be implemented. I would like to share a bit regarding the basic information about extracting malware from the dump memory using a powerful application called volatility. i called it basic knowledge because i want to give you some ideas on how to analyze things in the memory. After getting the memory dump it’s time to fetch the data from it. for this i am going to use bulk extractor , there are two way to use bulk extractor one is using command line interface and.
Comments are closed.