Exploring The Zero Trust Security Model Conll110

Zero Trust Security Model Pdf Learn more about the concepts and principles of the zero trust model and how microsoft 365 supports it. presented by mark simos and tarek dawoud. Today's organizations need a new security model that effectively adapts to the complexity of the modern environment, embraces the mobile workforce, and protects people, devices, apps, and data.

Embracing A Zero Trust Security Model Pdf Computer Security Security Exploring the zero trust security model | conll110 today's organizations need a new security model that effectively adapts to the complexity of the modern environment, embraces the mobile workforce, and protects people, devices, apps, and data where they're located. Explore the zero trust security model in this comprehensive 1 hour 15 minute conference talk from microsoft. discover how this new security approach adapts to modern environments, supports mobile workforces, and protects people, devices, apps, and data regardless of location. Organisasi saat ini membutuhkan model keamanan baru yang secara efektif beradaptasi dengan kompleksitas lingkungan modern, merangkul tenaga kerja seluler, dan melindungi orang, perangkat, aplikasi, dan data tempat mereka berada. A deep dive into the zero trust security model, explaining its principles and how it fortifies your cybersecurity defenses.
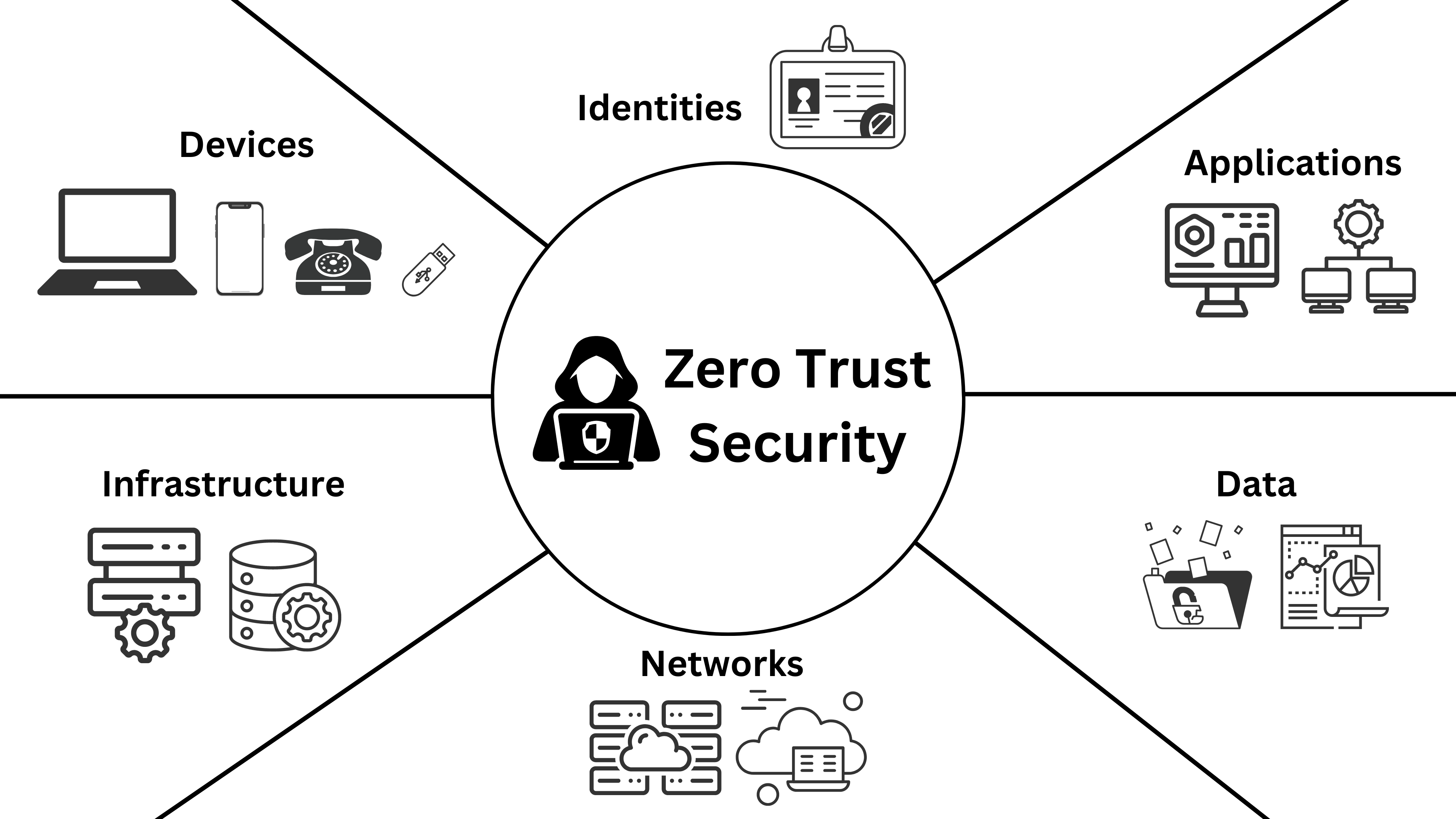
Ztn Webp Organisasi saat ini membutuhkan model keamanan baru yang secara efektif beradaptasi dengan kompleksitas lingkungan modern, merangkul tenaga kerja seluler, dan melindungi orang, perangkat, aplikasi, dan data tempat mereka berada. A deep dive into the zero trust security model, explaining its principles and how it fortifies your cybersecurity defenses. Learning and development services. Before delving into the benefits of zero trust, it is crucial to understand the core principles that underpin this security model. these principles form the foundation of zero trust architecture and guide its implementation. Unlike traditional security models that rely on a defined network perimeter, zero trust operates on the principle that no user or system should be automatically trusted. In the chapters that follow, this study presents a comprehensive analysis of the zero trust security model, offering actionable insights for organizations seeking to strengthen their cybersecurity posture.

Zero Trust Security Model Ciso2ciso Com Cyber Security Group Learning and development services. Before delving into the benefits of zero trust, it is crucial to understand the core principles that underpin this security model. these principles form the foundation of zero trust architecture and guide its implementation. Unlike traditional security models that rely on a defined network perimeter, zero trust operates on the principle that no user or system should be automatically trusted. In the chapters that follow, this study presents a comprehensive analysis of the zero trust security model, offering actionable insights for organizations seeking to strengthen their cybersecurity posture.
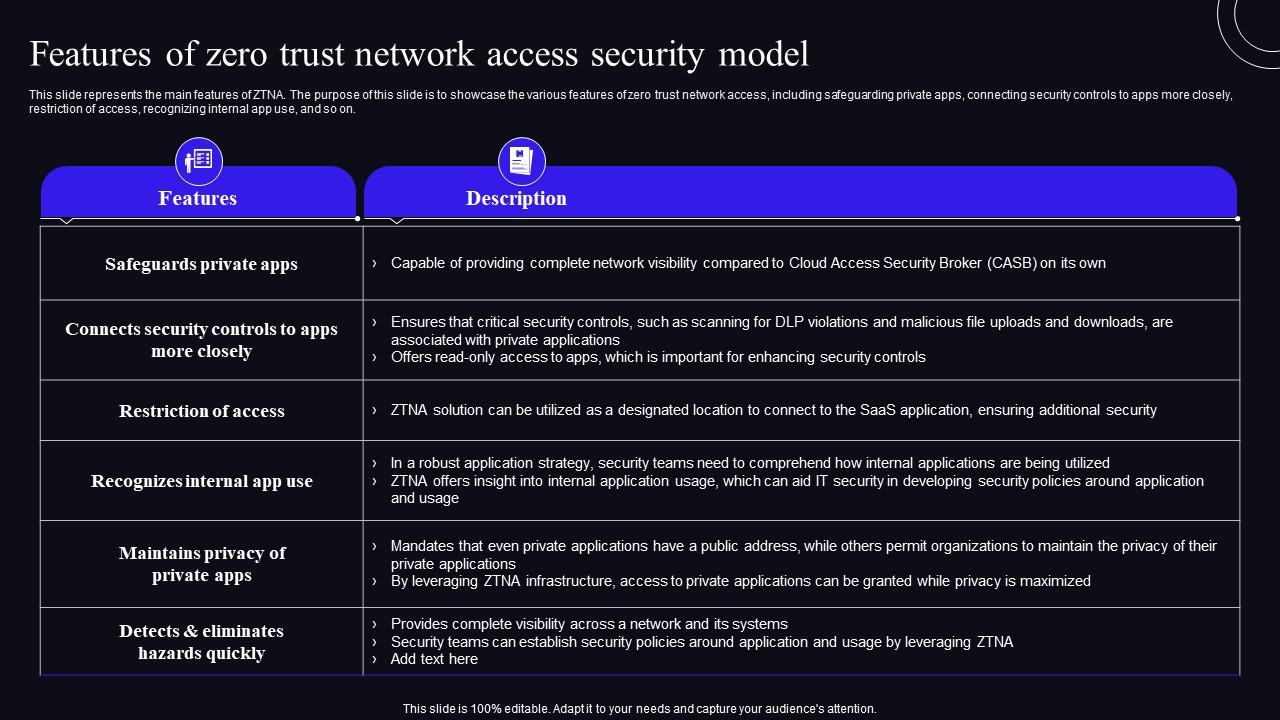
Features Of Zero Trust Network Access Security Model Zero Trust Unlike traditional security models that rely on a defined network perimeter, zero trust operates on the principle that no user or system should be automatically trusted. In the chapters that follow, this study presents a comprehensive analysis of the zero trust security model, offering actionable insights for organizations seeking to strengthen their cybersecurity posture.

Working Of Zero Trust Network Access Model Zero Trust Security Model
Comments are closed.