Exploring Sessions Wallarm Documentation

Wallarm Cyber Security Solutions Pdf Vulnerability Computing As soon as wallarm's api sessions identified user sessions related to your applications, you can explore them in the api sessions section of wallarm console. learn from this article how to go through the discovered data. Api sessions include the built in rules for the session identification and requires only enabled wallarm node to start working. optionally, you can fine tune api sessions under your needs as described in this article.
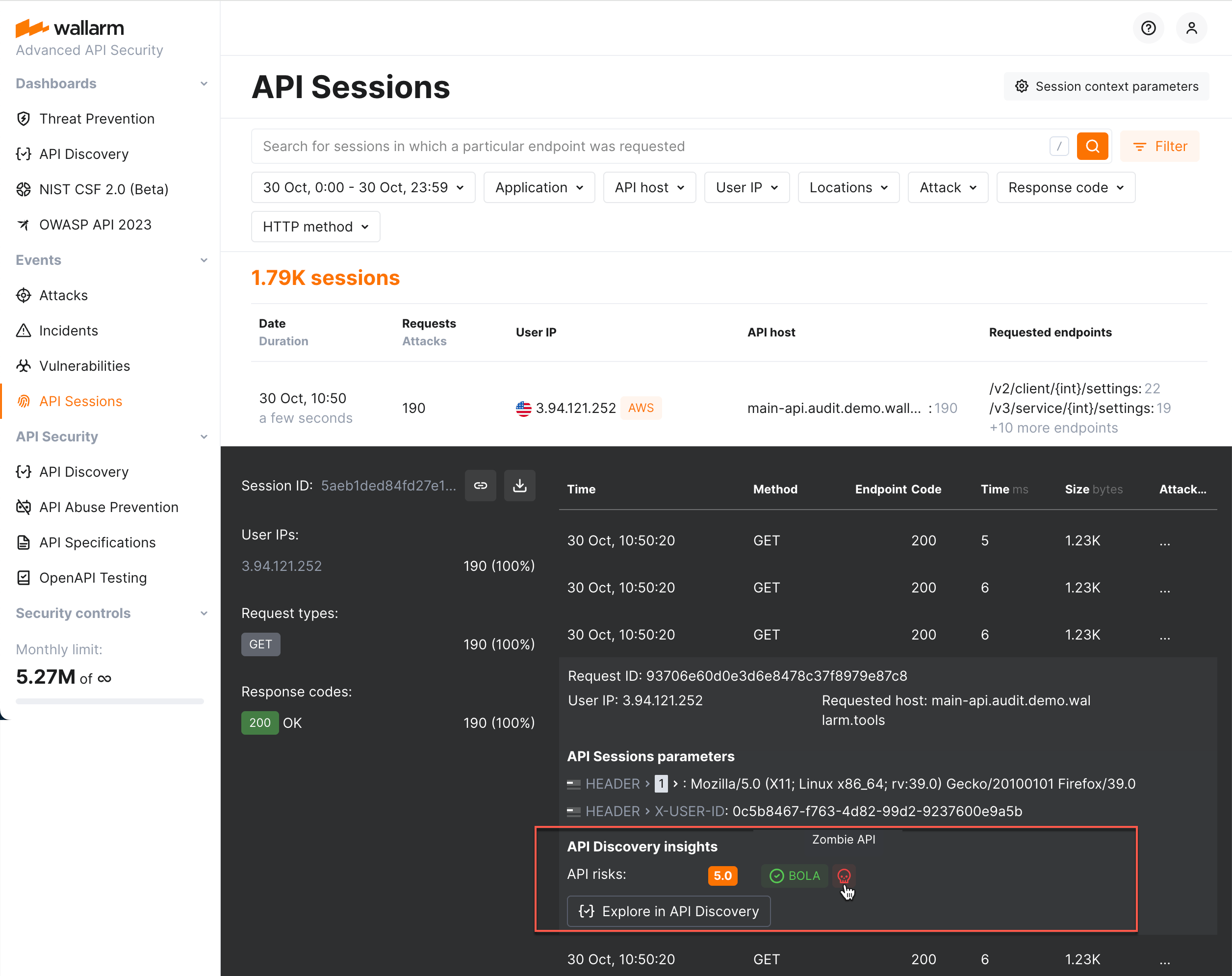
Exploring Sessions Wallarm Documentation Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. A structured view of session activity helps in understanding your endpoint place in malicious and legitimate activities, its relation to sensitive business flows and required protection measures. All traffic that wallarm node is enabled to secure is organized into sessions and displayed in the api sessions section. you can customize how requests should be grouped into sessions based on your applications' logic. To perform this analysis, in wallarm console → attacks, access the bot attack details, then click explore in api sessions. wallarm will open the api session section filtered: the session (s) related to this bot activities will be displayed.
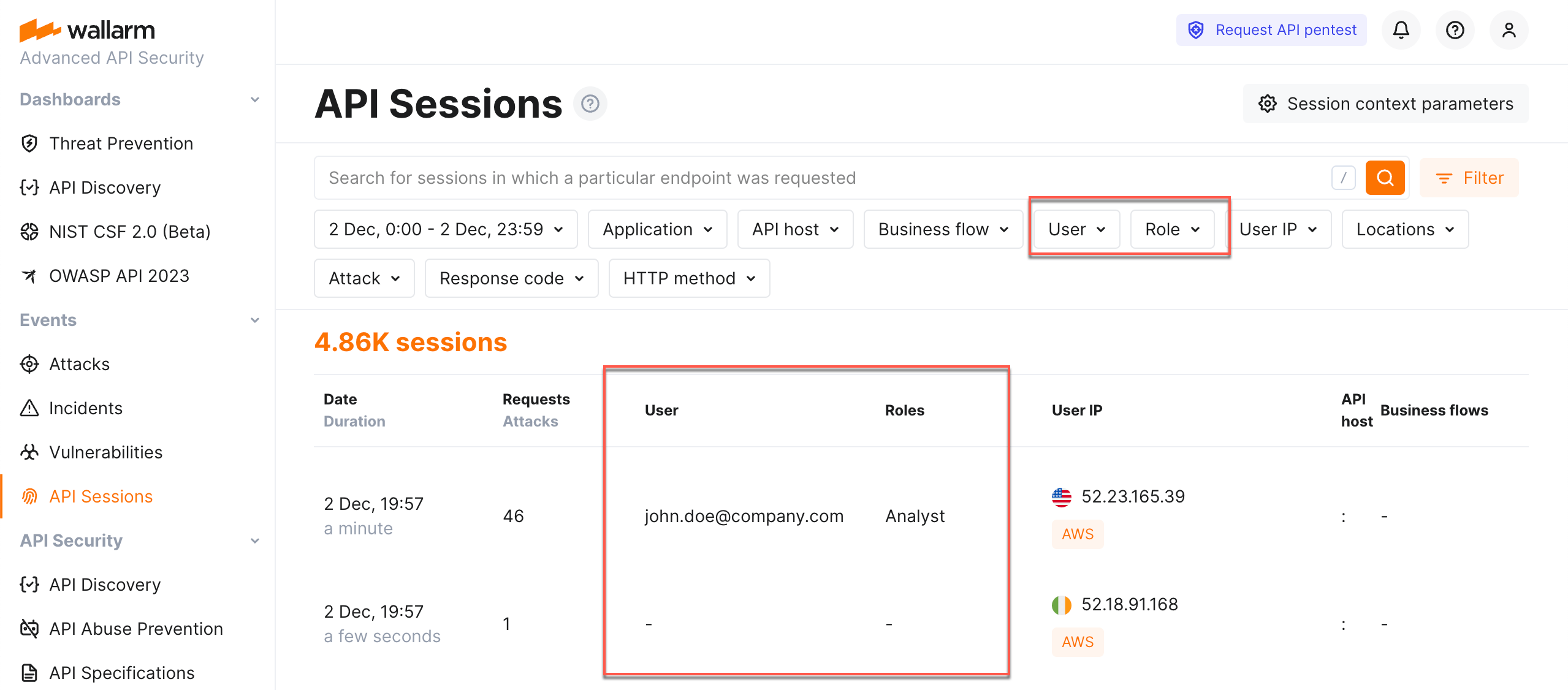
Exploring Sessions Wallarm Documentation All traffic that wallarm node is enabled to secure is organized into sessions and displayed in the api sessions section. you can customize how requests should be grouped into sessions based on your applications' logic. To perform this analysis, in wallarm console → attacks, access the bot attack details, then click explore in api sessions. wallarm will open the api session section filtered: the session (s) related to this bot activities will be displayed. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. For session blocking to be an effective measure against different types of threats, how requests are grouped into sessions should be properly configured. we recommend using fingerprints for unauthenticated sessions and a user identifier (like user id, token, etc.) for authenticated ones. Exploring results you can view api security testing results in two ways: mainly in postman's ai mode (recommended), or in wallarm console for history and tracking. Wallarm automates real time application protection and security testing for apis, apps, and microservices and apis across multi cloud and k8s environments.
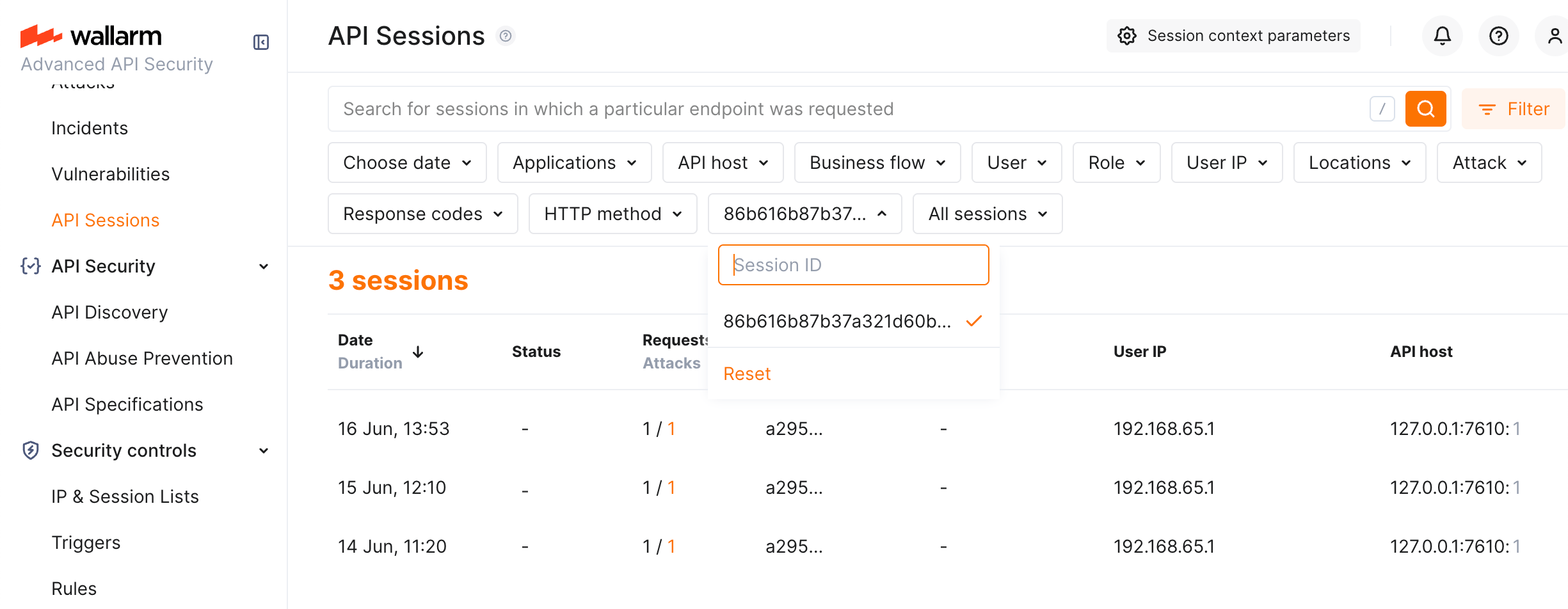
Exploring Sessions Wallarm Documentation Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. For session blocking to be an effective measure against different types of threats, how requests are grouped into sessions should be properly configured. we recommend using fingerprints for unauthenticated sessions and a user identifier (like user id, token, etc.) for authenticated ones. Exploring results you can view api security testing results in two ways: mainly in postman's ai mode (recommended), or in wallarm console for history and tracking. Wallarm automates real time application protection and security testing for apis, apps, and microservices and apis across multi cloud and k8s environments.
Comments are closed.