Exploring Github Repository Spoof That Mail
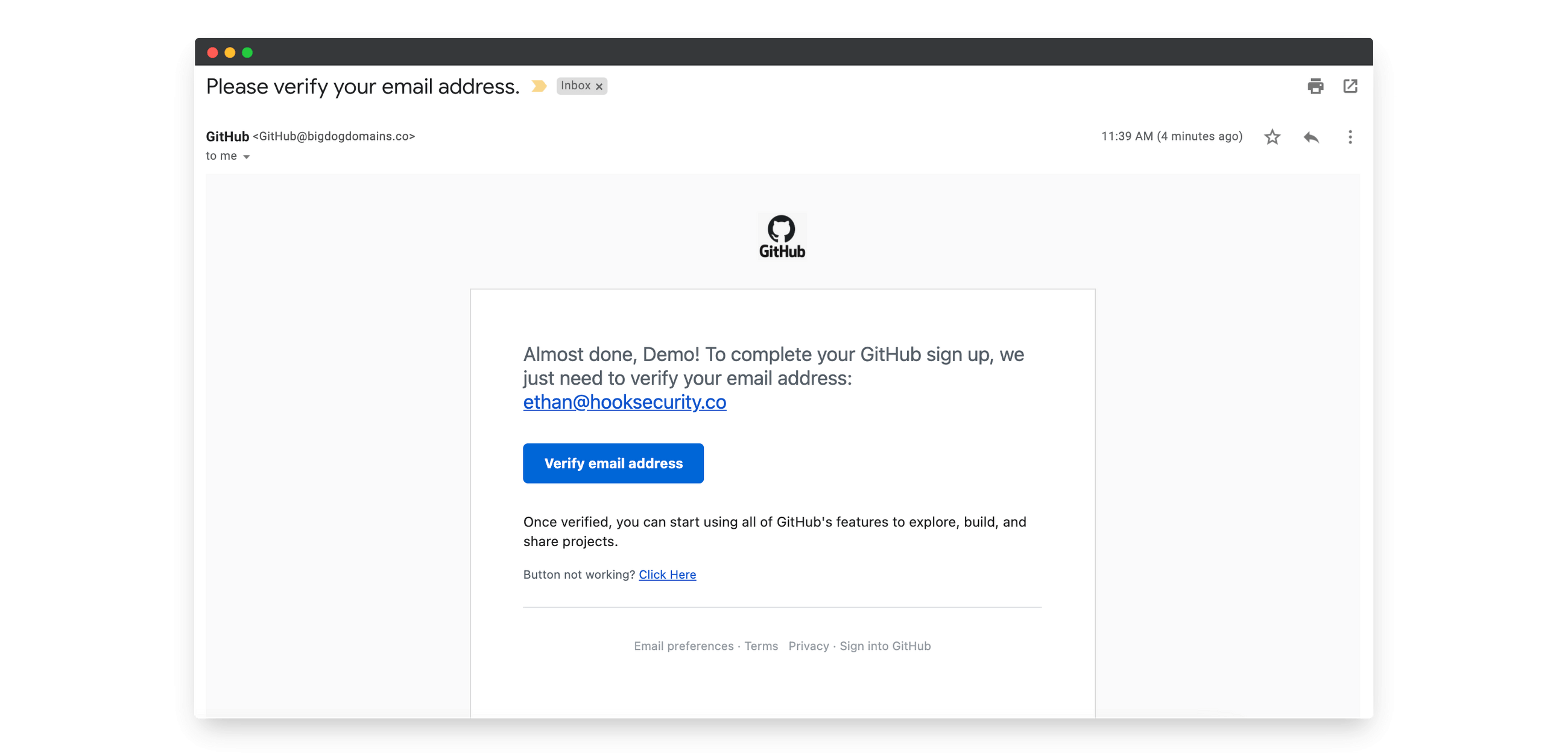
Github Phishing Email Example Hook Security Command line tool to detect email spoofing vulnerabilities by analyzing spf and dmarc dns records. supports single and bulk domain checks with multiple output formats. Exploring one of the trending github repository, spoofthatmail with testing and checking out reported issues.

Phishing On Github A Sophisticated Attack Leveraging Brand Trust Cybersecurity researchers have uncovered a sophisticated phishing campaign that exploits github notification emails to deliver stealthy malware to software developers. Apiiro’s findings reveal a large scale malicious repo confusion campaign impacting over 100,000 github repositories, shedding light on the evolving tactics of cybercriminals. A tool like “github commits email finder” ( lnkd.in gwxsxpsx) demonstrates how easily attackers can extract commit metadata, including contributor emails and associated ips, and cross reference them with databases like have i been pwned (hibp). I chose a well known open source project on github, forked the repository, and set my git configuration to impersonate one of its main maintainers. my goal: revert the latest commit and leave a message, seemingly from the other maintainer.
Malicious Actors Exploit Github To Distribute Fake Exploits A tool like “github commits email finder” ( lnkd.in gwxsxpsx) demonstrates how easily attackers can extract commit metadata, including contributor emails and associated ips, and cross reference them with databases like have i been pwned (hibp). I chose a well known open source project on github, forked the repository, and set my git configuration to impersonate one of its main maintainers. my goal: revert the latest commit and leave a message, seemingly from the other maintainer. Due to githubs file size limitation this cannot be included in the repository , so download , unzip and move the files into the prototype loader folder. place the files in the dataset folder and change the path in the respective files you wish to train with. In recent weeks, security researchers have uncovered an elaborate phishing campaign that leverages legitimate github notification mechanisms to deliver malicious content. victims receive seemingly authentic repository alerts, complete with real looking commit messages and collaborator updates. Commit spoofing in github can compromise your code integrity. read our guide to discover how to identify and extinguish github spoofing to secure your code. When a commit is pushed, github checks the author’s email against its user database. if there’s a match, github attributes that commit to the corresponding account, displaying the user’s name, avatar, and contribution history.
Comments are closed.