Exploring Building Trust Through Zero Trust

Exploring Building Trust Through Zero Trust The paper also discusses the innovative contributions of the zero trust model in these fields, the challenges it faces, and proposes corresponding solutions and future research directions. In this comprehensive guide, we’ll explore the principles of zero trust, how it builds trust in the modern enterprise, and strategies for effective implementation.

Building Trust Through Zero Trust This guidance contains an abstract definition of zero trust architecture (zta) and gives general deployment models and use cases where zero trust could improve an enterprise’s overall information technology security posture. The increasing complexity of digital ecosystems and evolving cybersecurity threats have highlighted the limitations of traditional perimeter based security models, leading to the growing adoption of zero trust architecture (zta). We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. This hub provides the most operationally practical zero trust guidance available, drawn from real deployments across government and enterprise in 40 countries. zero trust has become the most misunderstood concept in cybersecurity — most organisations are buying “zero trust products” without building a zero trust architecture.

Building Out Zero Trust Architecture Barrier Networks We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. This hub provides the most operationally practical zero trust guidance available, drawn from real deployments across government and enterprise in 40 countries. zero trust has become the most misunderstood concept in cybersecurity — most organisations are buying “zero trust products” without building a zero trust architecture. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Understand zero trust architecture and its key benefits to secure your network from threats. dive into our guide and start implementing now. Plan your zero trust deployment with the workshop tool and measure your posture with the automated assessment — now featuring a new ai pillar. To close the security gap, cios need to fully understand what zero trust is and gain strategic guidance and help on the best path forward, which includes a comprehensive, multi layer security approach with zero trust and innovative cyber solutions.
Zero Trust Architecture Key Components And Considerations This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Understand zero trust architecture and its key benefits to secure your network from threats. dive into our guide and start implementing now. Plan your zero trust deployment with the workshop tool and measure your posture with the automated assessment — now featuring a new ai pillar. To close the security gap, cios need to fully understand what zero trust is and gain strategic guidance and help on the best path forward, which includes a comprehensive, multi layer security approach with zero trust and innovative cyber solutions.

Building A Successful Zero Trust Architecture Lp Networks Plan your zero trust deployment with the workshop tool and measure your posture with the automated assessment — now featuring a new ai pillar. To close the security gap, cios need to fully understand what zero trust is and gain strategic guidance and help on the best path forward, which includes a comprehensive, multi layer security approach with zero trust and innovative cyber solutions.

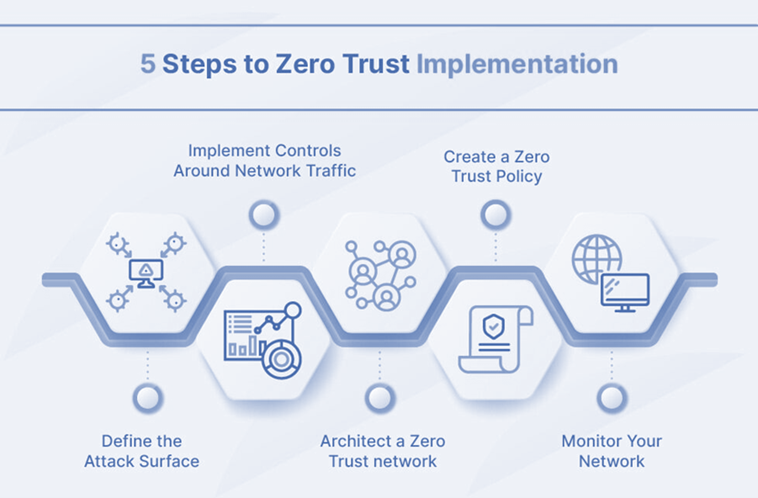
Building Blocks Of Zero Trust Infographic Portnox
Comments are closed.