Exploring Api Authentication Methods For Digital Infrastructure
Exploring Api Authentication Methods For Digital Infrastructure By becoming knowledgeable about the different authentication techniques and selecting the one that is most suitable for your company, you can ensure the security of your digital infrastructure, prevent unauthorised access, and lessen the likelihood of cyberattacks and data breaches. In this comprehensive guide, you’ll learn what api authentication is, why it matters, the most effective methods, best practices, and how to implement authentication in real world scenarios.

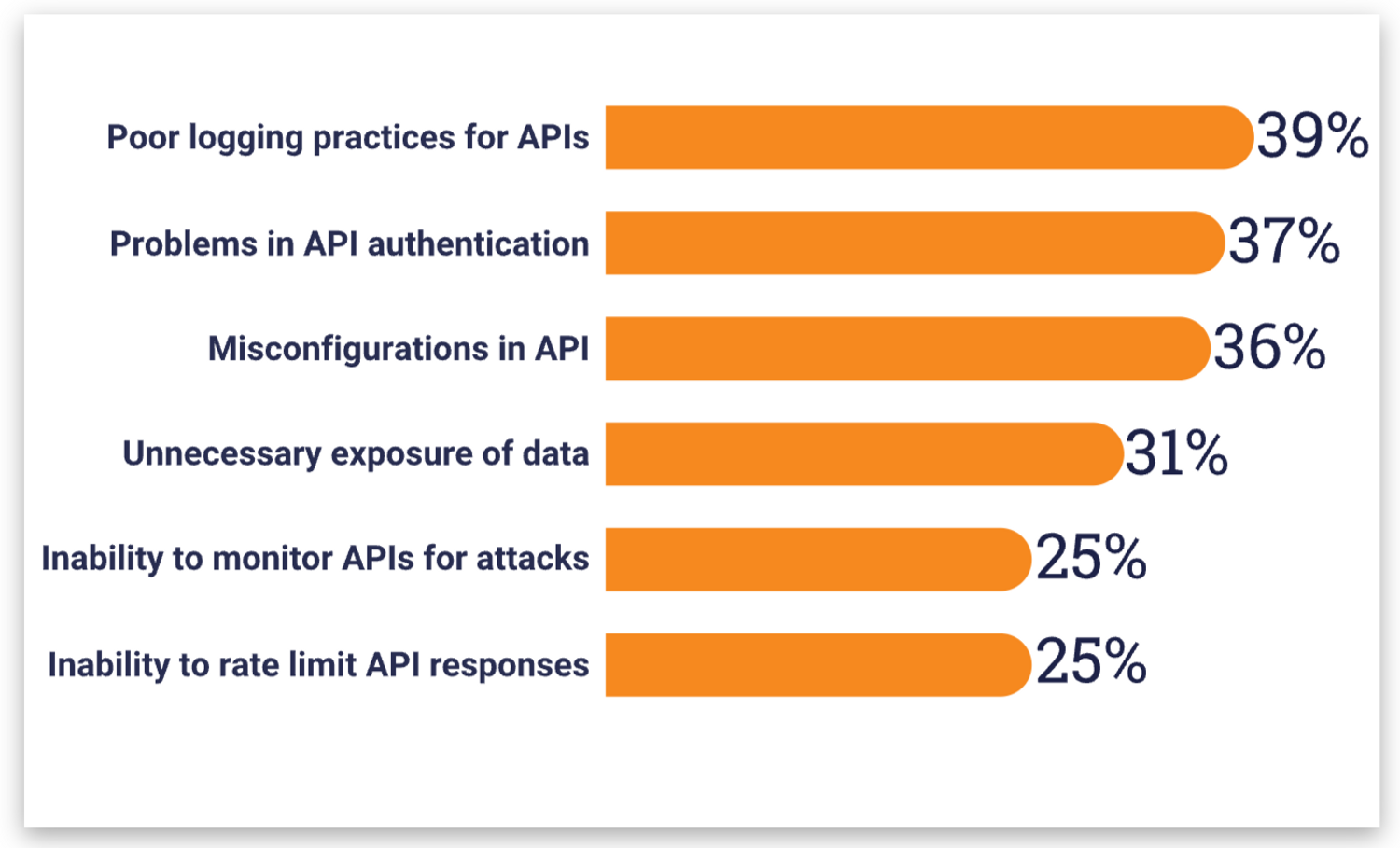
9 Popular Api Authentication Methods To Secure Api This paper reviews api security in cloud applications and discusses details of api vulnerabilities, existing security tools for api security to mitigate api attacks. In the enterprise, authentication isn't just a "lock"—it's the foundation of your entire trust model. i've seen too many teams treat these as the same thing, but they really aren't. Understand api authentication: api keys, oauth 2.0, jwt tokens, basic auth, and bearer tokens. when to use each method, security trade offs, and implementation examples. From api keys to oauth 2.0 and jwt — explore the most common api authentication methods, their strengths, weaknesses, and when to use each.

9 Popular Api Authentication Methods To Secure Api Understand api authentication: api keys, oauth 2.0, jwt tokens, basic auth, and bearer tokens. when to use each method, security trade offs, and implementation examples. From api keys to oauth 2.0 and jwt — explore the most common api authentication methods, their strengths, weaknesses, and when to use each. This paper comprehensively reviews current api authentication methods, evaluates their security effectiveness, and discusses innovative trends such as zero trust architecture and continuous authentication. With the proliferation of microservices, api gateways, and high transactional systems, choosing the right authentication mechanism can make or break your api’s security and performance. this. Explore api authentication methods like oauth, jwt, and api keys, along with best practices and top tools to enhance api security. Explore 7 api authentication methods, their tradeoffs, and why real time api monitoring is essential in modern socs.

9 Popular Api Authentication Methods To Secure Api This paper comprehensively reviews current api authentication methods, evaluates their security effectiveness, and discusses innovative trends such as zero trust architecture and continuous authentication. With the proliferation of microservices, api gateways, and high transactional systems, choosing the right authentication mechanism can make or break your api’s security and performance. this. Explore api authentication methods like oauth, jwt, and api keys, along with best practices and top tools to enhance api security. Explore 7 api authentication methods, their tradeoffs, and why real time api monitoring is essential in modern socs.
Most Common Api Authentication Methods And Best Practices Explore api authentication methods like oauth, jwt, and api keys, along with best practices and top tools to enhance api security. Explore 7 api authentication methods, their tradeoffs, and why real time api monitoring is essential in modern socs.
Comments are closed.