Exploiting Understanding Jwt Authentication Tokens Hacklido

Exploiting Understanding Jwt Authentication Tokens Hacklido Almost in our every day internet connected life, secure authentication is crucial. jwt (json web token) has become a mainstay in modern authentication, providing stateless, portable and cryptographically secured data exchange between web application, apis and single sign on systems. Learn how to identify and exploit json web token (jwt) vulnerabilities using several different testing methods. read the article now!.
Exploiting Understanding Jwt Authentication Tokens Hacklido Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. This lab reinforced some important real world security concepts: • understanding how jwt authentication works • identifying insecure token validation • exploiting weak configurations like. The token endpoint accepts a resource parameter that specifies which azure service the token should be scoped to. this is the audience claim (aud) in the resulting jwt. the imds endpoint will issue a token for any valid audience url, regardless of whether the managed identity has permissions on the target service. Before json web tokens (jwts) became popular in today’s app development landscape, web applications predominantly used server side sessions, which presented horizontal scalability issues. jwts solved this by moving authentication data from the server to the token itself.
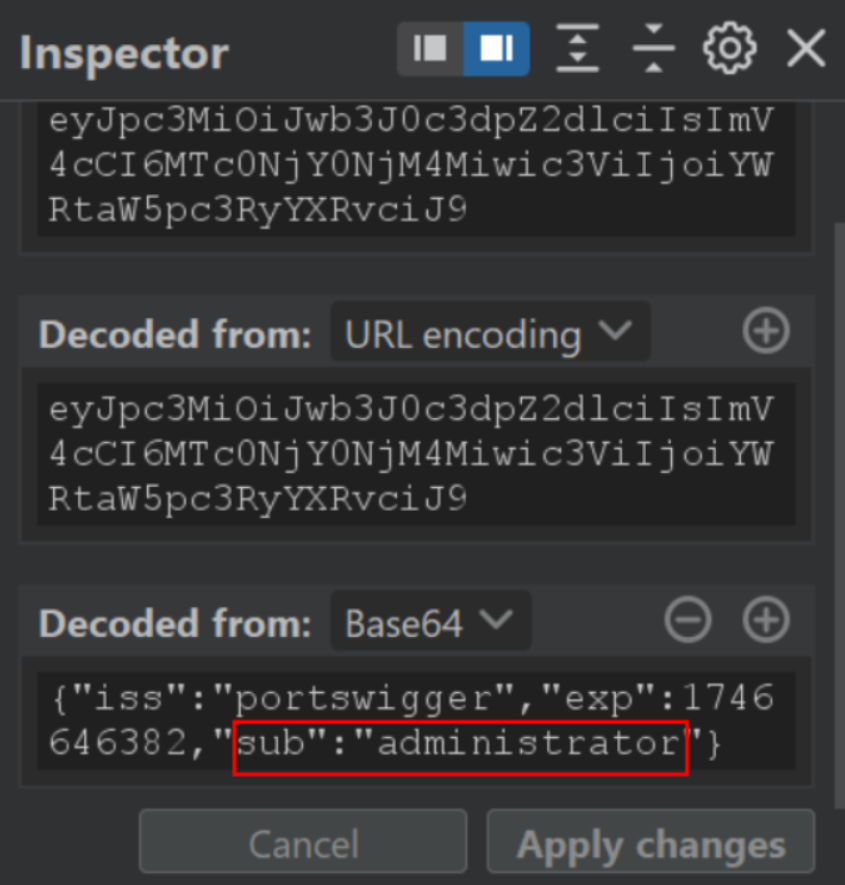
Exploiting Understanding Jwt Authentication Tokens Hacklido The token endpoint accepts a resource parameter that specifies which azure service the token should be scoped to. this is the audience claim (aud) in the resulting jwt. the imds endpoint will issue a token for any valid audience url, regardless of whether the managed identity has permissions on the target service. Before json web tokens (jwts) became popular in today’s app development landscape, web applications predominantly used server side sessions, which presented horizontal scalability issues. jwts solved this by moving authentication data from the server to the token itself. This article dissects a real world jwt jku header injection attack, showing how an attacker can forge admin tokens by hosting a malicious jwks, and provides a step‑by‑step guide to exploiting and fixing the vulnerability in a node.js application. In this post, we’ll go beyond the basics of jwt exploitation, exploring advanced techniques for bypassing authentication, gaining unauthorized access, and achieving privilege escalation. Json web tokens (jwts) are widely used for authentication and authorization in modern apis. however, misconfigurations or weak secrets can turn them into attack vectors. Attackers can circumvent authentication by changing the token signature via a vulnerability in the jwt library or signature validation code to avoid signature verification and produce a forged token if the jwt token signature validation is not implemented correctly.
Comments are closed.