Exploiting Php Filter Chains For Arbitrary File Read
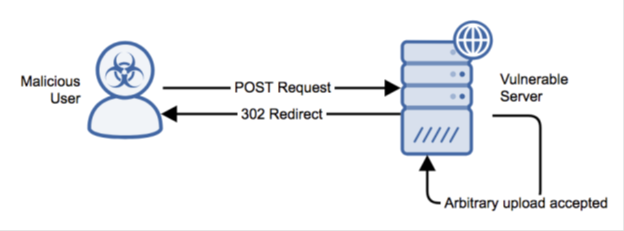
Web Server Phpcollab Editclient Php Arbitrary File Upload Alert Logic Using an error based oracle (and some php quirks) to arbitrarily exfiltrate a file via php filter chains. this technique came 4th in the portswigger's top 10 and also made our own hackernotes top 5!. As long as an action is performed on a file content and the full uri is controlled, the function can be affected by the php: filter wrapper, and therefore exploited by this tool.
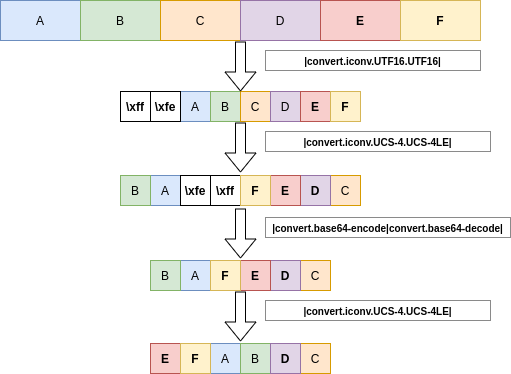
Php Filter Chains File Read From Error Based Oracle Using an error based oracle (and some php quirks) to arbitrarily exfiltrate a file via php filter chains. this technique came 4th in the portswigger's top 10 and also made our own. Rather than diving into the deep technical internals (which can be reviewed in the poc comments), this guide presents a procedural oriented programming (pop) adaptation of synacktiv's original object oriented programming (oop) exploit (available here). Hash kitten basically explained that the file could be leaked via an error based oracle. this blogpost details the several filter chain tricks involved in this attack, as well as some optimization from the original writeup. This skill helps you exploit local file inclusion (lfi) vulnerabilities in php applications by using php filter chains to generate arbitrary code without writing to disk.
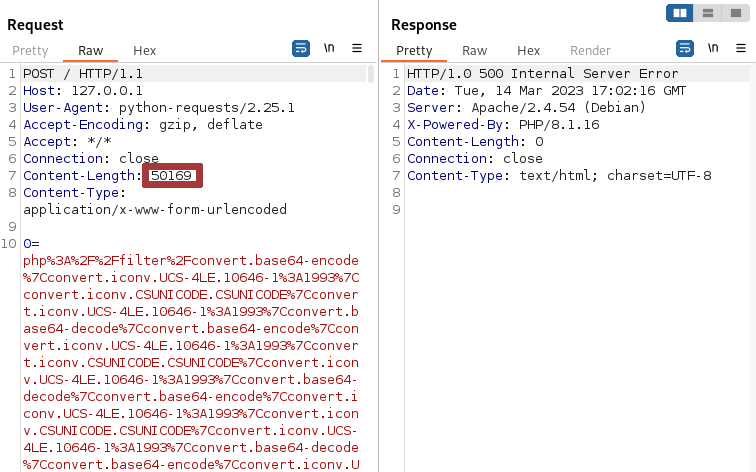
Php Filter Chains File Read From Error Based Oracle Hash kitten basically explained that the file could be leaked via an error based oracle. this blogpost details the several filter chain tricks involved in this attack, as well as some optimization from the original writeup. This skill helps you exploit local file inclusion (lfi) vulnerabilities in php applications by using php filter chains to generate arbitrary code without writing to disk. This article will cover various techniques for exploiting local file inclusion (lfi) vulnerabilities, including leveraging php wrappers, specific server paths, and other creative methods to. We discovered an interesting ctf inspired vulnerability, cve 2026 22200, in osticket, a popular open source helpdesk system. this flaw allows anonymous attackers to read arbitrary files from the server by injecting malicious php filter chain expressions into a ticket and then exporting it to pdf. This document covers the core exploitation mechanism used by the php include to shell char dict system to achieve arbitrary file reading with simultaneous code injection through php's php: filter stream wrapper. This technique is relevant in cases where you control the file path of a php function that will access a file but you won’t see the content of the file (like a simple call to file()) but the content is not shown.

Php Filter Chains File Read From Error Based Oracle R Netsec This article will cover various techniques for exploiting local file inclusion (lfi) vulnerabilities, including leveraging php wrappers, specific server paths, and other creative methods to. We discovered an interesting ctf inspired vulnerability, cve 2026 22200, in osticket, a popular open source helpdesk system. this flaw allows anonymous attackers to read arbitrary files from the server by injecting malicious php filter chain expressions into a ticket and then exporting it to pdf. This document covers the core exploitation mechanism used by the php include to shell char dict system to achieve arbitrary file reading with simultaneous code injection through php's php: filter stream wrapper. This technique is relevant in cases where you control the file path of a php function that will access a file but you won’t see the content of the file (like a simple call to file()) but the content is not shown.
Github Synacktiv Php Filter Chains Oracle Exploit A Cli To Exploit This document covers the core exploitation mechanism used by the php include to shell char dict system to achieve arbitrary file reading with simultaneous code injection through php's php: filter stream wrapper. This technique is relevant in cases where you control the file path of a php function that will access a file but you won’t see the content of the file (like a simple call to file()) but the content is not shown.
Comments are closed.