Exploiting An Api Endpoint Using Documentation Portswigger Academy Tutorial

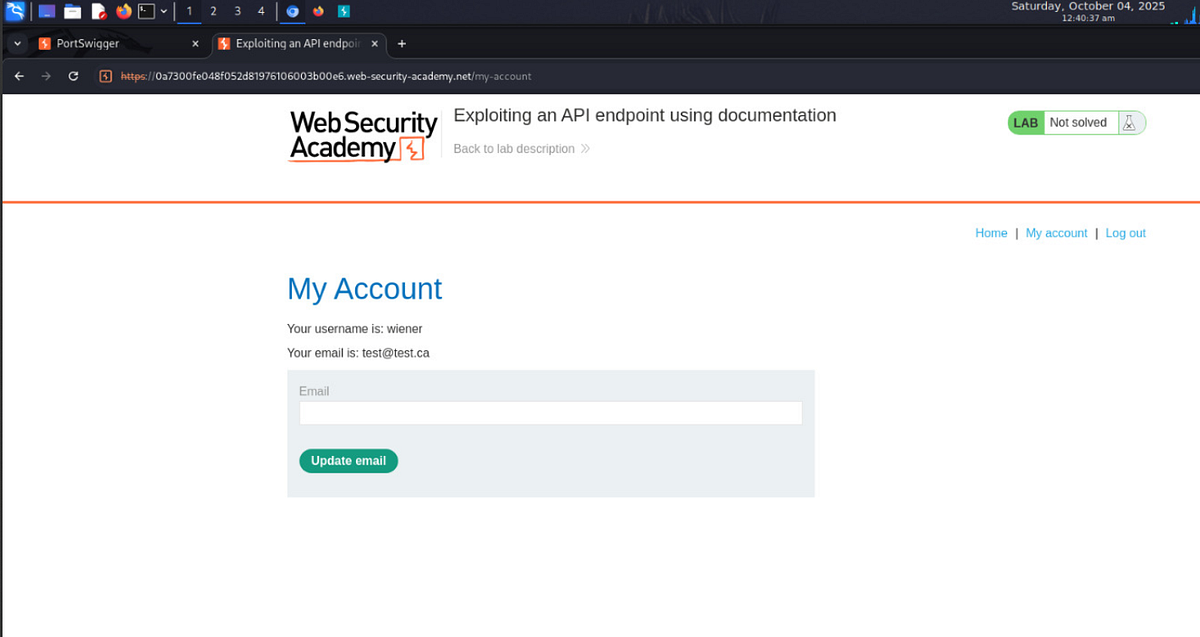
Lab Exploiting An Api Endpoint Using Documentation Web Security Academy Required knowledge to solve this lab, you'll need to know: what api documentation is. how api documentation may be useful to an attacker. how to discover api documentation. these points are covered in our api testing academy topic. A pi testing — lab: exploiting an api endpoint using documentation in this portswigger web security academy lab, the goal is simple:.

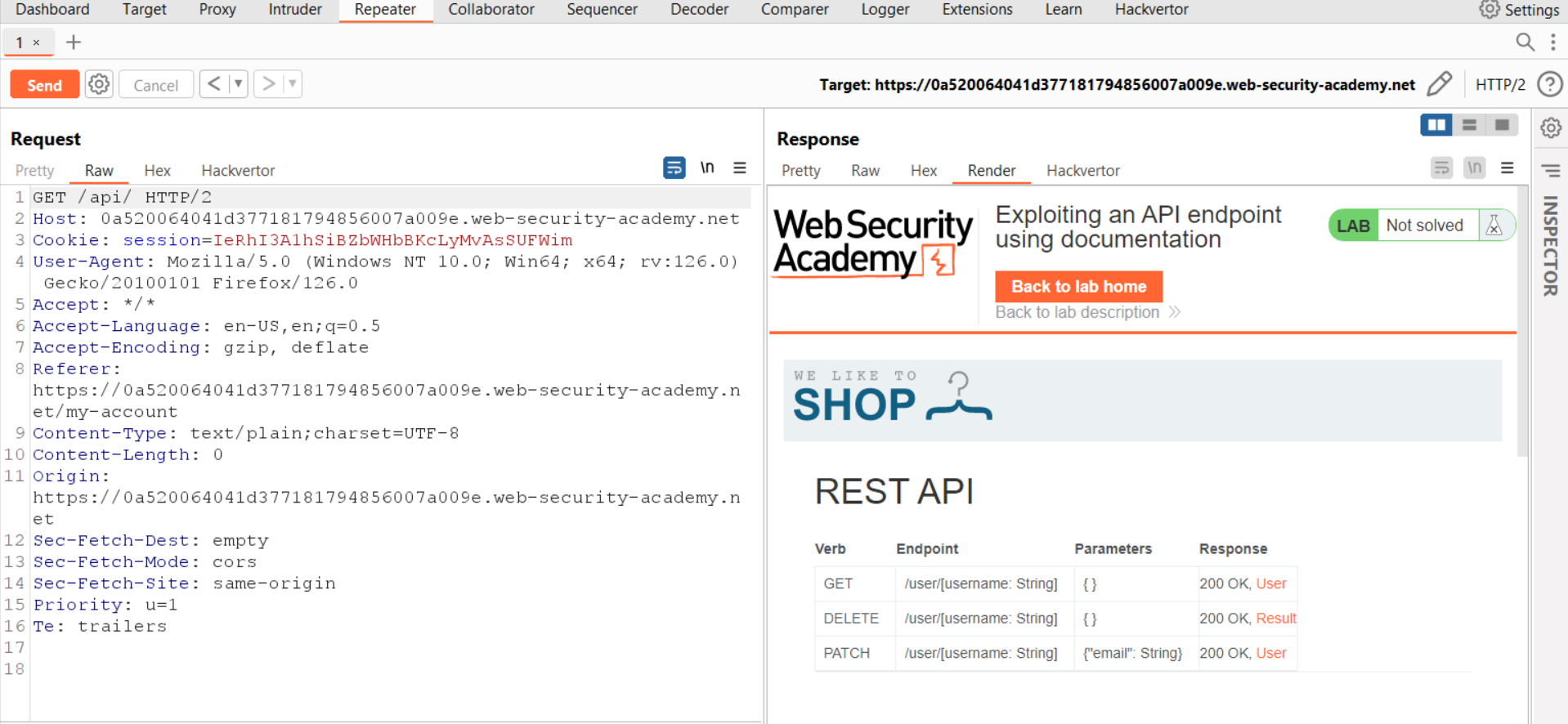
Christian V Exploiting An Api Endpoint Using Documentation The lab demonstrated in this video can be found at the following link: portswigger web security api testing lab exploiting api endpoint using docu. 1. exploiting an api endpoint using documentation we’re asked to delete the user “carlos” using the api exposed by this web application. we find the documentation for the api via api and see that we can delete a user by sending a delete request to api user username. To start api testing, we first need to find out as much information about the api as possible, to discover its attack surface. to begin, we should identify api endpoints. Exploiting an api endpoint using documentation ¶ portswigger web security learning paths api testing api testing identifying and interacting with api endpoints api testing lab exploiting unused api endpoint.

Free Video Learning Server Side Request Forgery Basics Using To start api testing, we first need to find out as much information about the api as possible, to discover its attack surface. to begin, we should identify api endpoints. Exploiting an api endpoint using documentation ¶ portswigger web security learning paths api testing api testing identifying and interacting with api endpoints api testing lab exploiting unused api endpoint. To start api testing, you first need to find out as much information about the api as possible, to discover its attack surface. to begin, you should identify api endpoints. these are locations where an api receives requests about a specific resource on its server. Public facing api documentation is often overlooked by devs and testers — but not by attackers. this lab proves how “helpful” docs can turn into a red carpet for exploitation. After getting a basic understanding of apis let’s now try to find these api endpoints and exploit them using their documentation. we will be using portswigger’s lab to see the same in action. Api testing is important as vulnerabilities in apis may undermine core aspects of a website’s confidentiality, integrity, and availability. let dive into this lab dummy walkthrough :).
Exploiting An Api Endpoint Using Documentation Lab1 Portswigger To start api testing, you first need to find out as much information about the api as possible, to discover its attack surface. to begin, you should identify api endpoints. these are locations where an api receives requests about a specific resource on its server. Public facing api documentation is often overlooked by devs and testers — but not by attackers. this lab proves how “helpful” docs can turn into a red carpet for exploitation. After getting a basic understanding of apis let’s now try to find these api endpoints and exploit them using their documentation. we will be using portswigger’s lab to see the same in action. Api testing is important as vulnerabilities in apis may undermine core aspects of a website’s confidentiality, integrity, and availability. let dive into this lab dummy walkthrough :).
Exploiting An Api Endpoint Using Documentation Cyberiumx After getting a basic understanding of apis let’s now try to find these api endpoints and exploit them using their documentation. we will be using portswigger’s lab to see the same in action. Api testing is important as vulnerabilities in apis may undermine core aspects of a website’s confidentiality, integrity, and availability. let dive into this lab dummy walkthrough :).
Exploiting An Api Endpoint Using Documentation Cyberiumx
Comments are closed.