Exploitation Of Vulnerabilities A Topic Based Machine Learning

A Machine Learning Based Attack Detection And Miti Pdf To address this research gap, in the current study, we focus on extracting topics based on the textual content found in vulnerability descriptions, via word clustering, to investigate which weaknesses are strongly associated with recent exploits and most likely to be exploited in the future. Security vulnerabilities constitute one of the most important weaknesses of hardware and software security that can cause severe damage to systems, applications, and users.
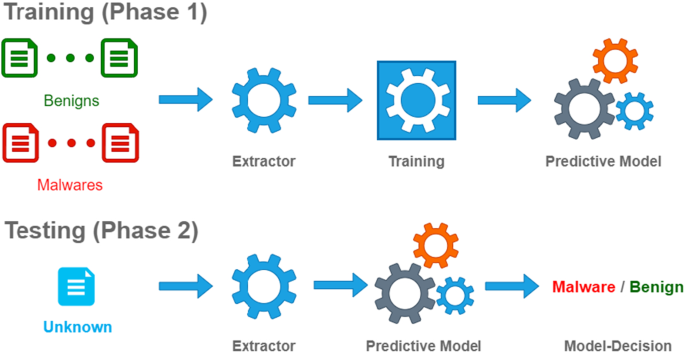
Exploitation Of Vulnerabilities A Topic Based Machine Learning The proposed framework is a framework that maps newly disclosed vulnerabilities with topic distributions, via word clustering, and predicts whether this new entry will be associated with a potential exploit proof of concept (poc). The study presents a robust framework for predicting the exploitation of vulnerabilities using topic based machine learning techniques. the proposed method enhances the accuracy of vulnerability assessment and provides actionable insights for cybersecurity professionals. Tl;dr: a topic based machine learning framework for explaining and predicting exploitation of vulnerabilities prioritizes vulnerabilities based on their topic distributions and exploit indicators. We also provide insights on the current most exploitable weaknesses and products through a generalized linear model (glm) that links the topic memberships of vulnerabilities with exploit indicators, thus distinguishing five topics that are associated with relatively frequent recent exploits.

Feature Selection For Machine Learning Based Early Detection Of Tl;dr: a topic based machine learning framework for explaining and predicting exploitation of vulnerabilities prioritizes vulnerabilities based on their topic distributions and exploit indicators. We also provide insights on the current most exploitable weaknesses and products through a generalized linear model (glm) that links the topic memberships of vulnerabilities with exploit indicators, thus distinguishing five topics that are associated with relatively frequent recent exploits. To address this research gap, in the current study, we focus on extracting topics based on the textual content found in vulnerability descriptions, via word clustering, to investigate which weaknesses are strongly associated with recent exploits and most likely to be exploited in the future. The study utilizes multiple machine learning algorithms to establish models for vulnerability prioritization and provides insights into recent exploitable vulnerabilities. Abstract: security vulnerabilities constitute one of the most important weaknesses of hardware and software security that can cause severe damage to systems, applications, and users. In this paper, authors proposed a framework that maps newly disclosed vulnerabilities with topic distributions and further predicts whether this new entry will be associated with a potential exploit proof of concept.

Machine Learning Platform Vulnerabilities Detailed Sc Media To address this research gap, in the current study, we focus on extracting topics based on the textual content found in vulnerability descriptions, via word clustering, to investigate which weaknesses are strongly associated with recent exploits and most likely to be exploited in the future. The study utilizes multiple machine learning algorithms to establish models for vulnerability prioritization and provides insights into recent exploitable vulnerabilities. Abstract: security vulnerabilities constitute one of the most important weaknesses of hardware and software security that can cause severe damage to systems, applications, and users. In this paper, authors proposed a framework that maps newly disclosed vulnerabilities with topic distributions and further predicts whether this new entry will be associated with a potential exploit proof of concept.
Comments are closed.