Exploit Writing Tutorial Part 1 Stack Based Overflows Corelan

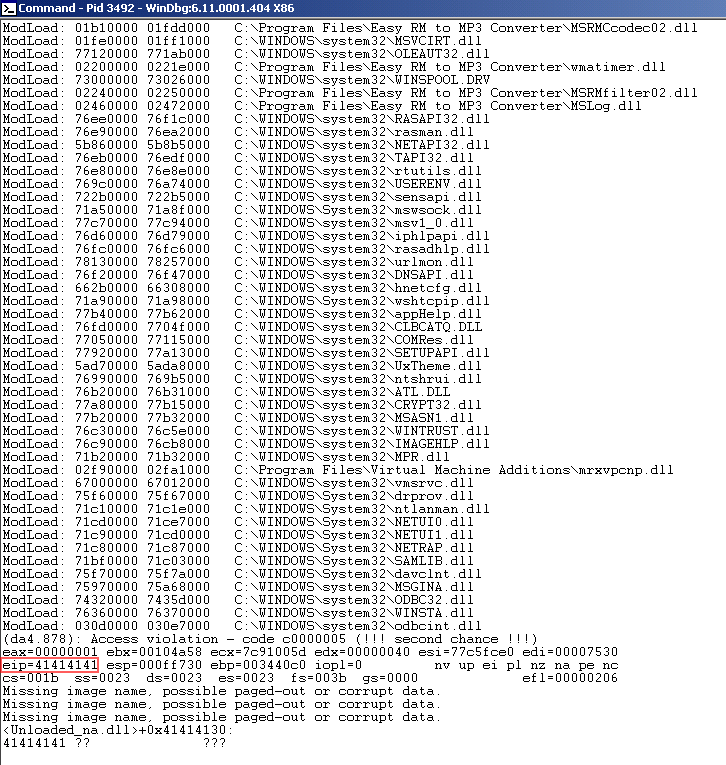
Peter Van Eeckhoutte S Blog Exploit Writing Tutorial Part 1 Stack We’re kicking things off with part 1 of the original series: 👉 exploit writing tutorial part 1 in the first video, we exploit a stack based buffer overflow on a modern windows 11 x64 environment. by the end of the tutorial, you will have learned: what a stack based buffer overflow really is the role of registers and key assembly instructions. This tutorial aims to explain the process of building an exploit from scratch, using a real world vulnerability in the easy rm to mp3 conversion utility as an example.
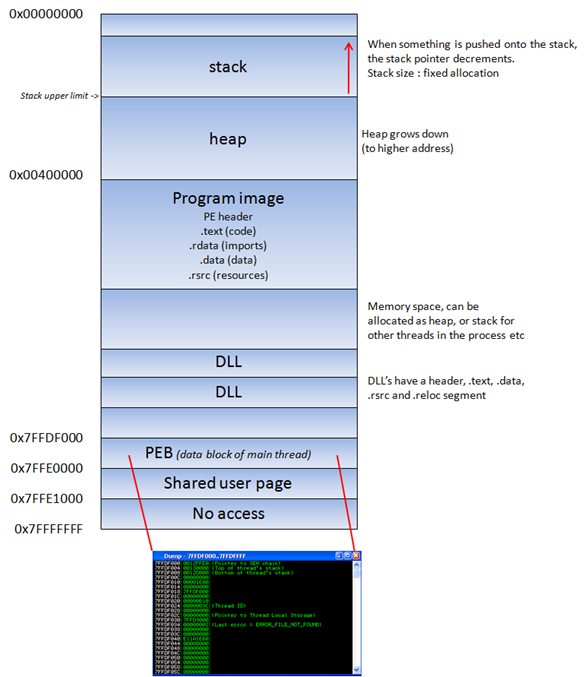
Exploit Writing Tutorial Part 1 Stack Based Overflows Penetration When a buffer on the stack overflows, the term stack based overflow or stack buffer overflow is used. when you are trying to write past the end of the stack frame, the term stack overflow is used. More specifically, in this video we will be exploiting a stack based buffer overflow on a windows 11 (x64) based virtual machine! by the end of the tutorial, you will have learned how. Exploit writing tutorial part 1 stack based overflows corelan team free download as pdf file (.pdf), text file (.txt) or read online for free. exploit writing tutorial by corelan team. Advisory source: link exploit writing tutorial part 1 stack based overflows.
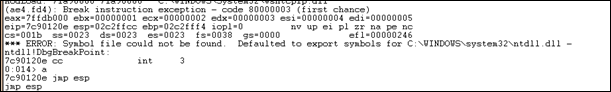
Exploit Writing Tutorial Part 1 Stack Based Overflows Penetration Exploit writing tutorial part 1 stack based overflows corelan team free download as pdf file (.pdf), text file (.txt) or read online for free. exploit writing tutorial by corelan team. Advisory source: link exploit writing tutorial part 1 stack based overflows. Corelan stack is a windows stack exploit development training. learn stack frames, calling conventions, seh overwrites, dep bypasses, rop frameworks, rop decoding, finding bad characters, egghunters on windows 11? memory layout, and real world exploitation techniques. Ever since i’ve started this blog, writing a basic tutorial about writing buffer overflows has been on my “to do” list… but i never really took the time to do so (or simply forgot about it). It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time…. It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time….
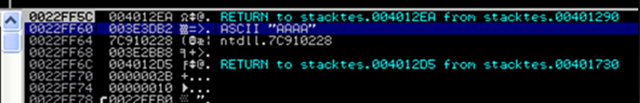
Exploit Writing Tutorial Part 1 Stack Based Overflows Penetration Corelan stack is a windows stack exploit development training. learn stack frames, calling conventions, seh overwrites, dep bypasses, rop frameworks, rop decoding, finding bad characters, egghunters on windows 11? memory layout, and real world exploitation techniques. Ever since i’ve started this blog, writing a basic tutorial about writing buffer overflows has been on my “to do” list… but i never really took the time to do so (or simply forgot about it). It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time…. It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time….
Exploit Writing Tutorial Part 1 Stack Based Overflows Penetration It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time…. It’s clean, simple and allows me to demonstrate some of the techniques that are used to write working and stable stack based buffer overflows. so perhaps this is a good time….
Comments are closed.