Explaining Zero Day Exploits

Understanding Zero Day Exploits And How To Protect Your Business A zero day exploit is a method or code specifically engineered to trigger the underlying vulnerability. it enables attackers to take desired actions—such as executing commands, escalating privileges, or bypassing authentication—by exploiting the flaw. A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware.
A Guide To Zero Day Exploits Zero day exploits: it is difficult to detect and mitigate zero day vulnerabilities that are unknown to suppliers. attackers can exploit these vulnerabilities before security fixes are released. Zero day exploit refers to a security vulnerability that is unknown to the software vendor or the public, allowing attackers to exploit it before it can be patched. Learn what zero day exploits are and how attackers weaponize them. includes defense strategies, recent statistics, and real world case studies. What is a zero day exploit? a zero day exploit (also called a zero day threat) is an attack that takes advantage of a security vulnerability that does not have a fix in place.
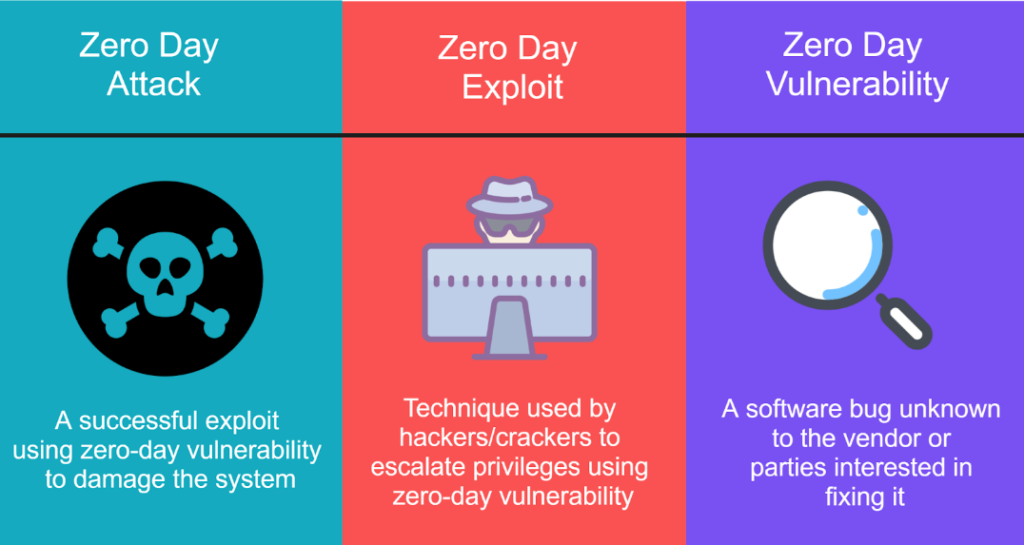
Understanding Zero Day Vulnerability Exploits Learn what zero day exploits are and how attackers weaponize them. includes defense strategies, recent statistics, and real world case studies. What is a zero day exploit? a zero day exploit (also called a zero day threat) is an attack that takes advantage of a security vulnerability that does not have a fix in place. This article is a complete guide to zero day exploits and how companies deal with the danger of undiscovered security flaws in it systems. we explain how zero day exploits typically occur and present the most effective ways to prevent hackers from leveraging unknown vulnerabilities in your systems. Zero day exploit: once attackers identify a zero day vulnerability, they develop a method or technique, known as an exploit, to exploit it. these exploits can be malicious code, phishing emails, or other tactics to bypass security measures and gain unauthorized system access. A zero day exploit is a piece of code or technique that exploits a software vulnerability unknown to the vendor since there are “zero days” of warning; no patch or fix exists, making it a powerful tool in the hands of attackers. A zero day exploit is a cyber vulnerability unknown to those needing to fix it, including product vendors. it represents a risk as developers have no time to patch it once exposed, leaving systems open to stealthy malicious activities until a solution is found.

Zero Day Exploits This article is a complete guide to zero day exploits and how companies deal with the danger of undiscovered security flaws in it systems. we explain how zero day exploits typically occur and present the most effective ways to prevent hackers from leveraging unknown vulnerabilities in your systems. Zero day exploit: once attackers identify a zero day vulnerability, they develop a method or technique, known as an exploit, to exploit it. these exploits can be malicious code, phishing emails, or other tactics to bypass security measures and gain unauthorized system access. A zero day exploit is a piece of code or technique that exploits a software vulnerability unknown to the vendor since there are “zero days” of warning; no patch or fix exists, making it a powerful tool in the hands of attackers. A zero day exploit is a cyber vulnerability unknown to those needing to fix it, including product vendors. it represents a risk as developers have no time to patch it once exposed, leaving systems open to stealthy malicious activities until a solution is found.
Comments are closed.