Example Of Data Breach Attack Cycle

Data Breach Prevention Phases Of Data Breach Attack Cycle Ppt Powerpoint Learn all the details about data breach lifecycles that cause financial and reputational damage on kron blog. This guide breaks down 30 famous data breaches, from massive data breach incidents like yahoo and cam4 to smaller incidents that changed security practices. for each one, you’ll learn what happened and what lessons apply to your organization today.
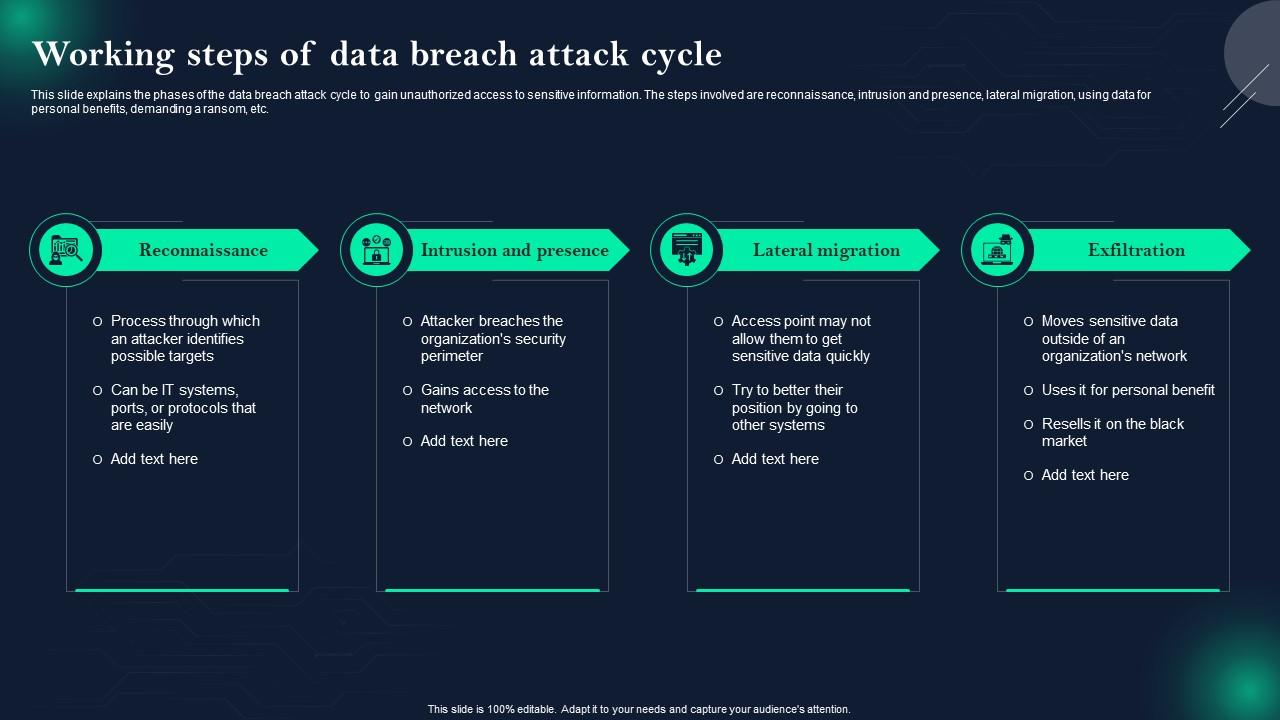
Data Breach Prevention Working Steps Of Data Breach Attack Cycle Ppt This article explores that roadmap. from the earliest phase of passive reconnaissance to the final act of data exfiltration and log cleansing, most cyberattacks follow a consistent, 10 step. Cyber attack chain (or cyber kill chain) is a step by step process hackers follow to carry out a cyberattack, starting with information gathering and often using phishing or malware to gain access. A cybersecurity data breach occurs when unauthorized individuals gain access to sensitive, protected, or confidential data. here's a step by step breakdown of what typically happens during a. There are five key data breach stages. learn how hackers pick their victims and identify vulnerabilities to exploit.
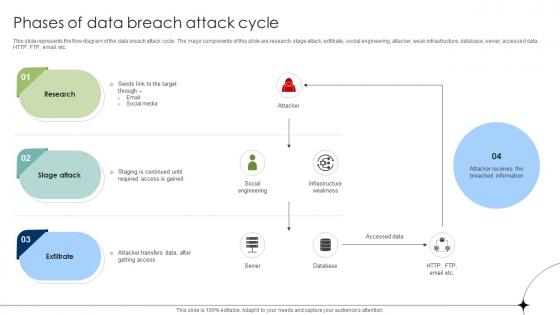
Phases Of Data Breach Attack Cycle Data Fortification Strengthening A cybersecurity data breach occurs when unauthorized individuals gain access to sensitive, protected, or confidential data. here's a step by step breakdown of what typically happens during a. There are five key data breach stages. learn how hackers pick their victims and identify vulnerabilities to exploit. You know you need to recover from this breach as quickly as possible, but what steps do you take to detect and rebuff the attacker? then, what comes after to ensure you can retain business continuity in the face of the breach?. When a data breach occurs, these steps will minimize the harm to the company and its clients. combined with dedicated employees, they will help the former spend a lot less money on recovery, while the latter will not lose as much sensitive information during the process. In this blog, we delve into the different stages of the data breach lifecycle and explore effective strategies to mitigate risks and minimize potential damages. Once the attacker has established an access point within the system, the next step is to set up an external communication channel. this enables them to send instructions, receive stolen data, and operate within the compromised environment with full control.

Working Steps Of Data Breach Attack Cycle Data Fortification You know you need to recover from this breach as quickly as possible, but what steps do you take to detect and rebuff the attacker? then, what comes after to ensure you can retain business continuity in the face of the breach?. When a data breach occurs, these steps will minimize the harm to the company and its clients. combined with dedicated employees, they will help the former spend a lot less money on recovery, while the latter will not lose as much sensitive information during the process. In this blog, we delve into the different stages of the data breach lifecycle and explore effective strategies to mitigate risks and minimize potential damages. Once the attacker has established an access point within the system, the next step is to set up an external communication channel. this enables them to send instructions, receive stolen data, and operate within the compromised environment with full control.
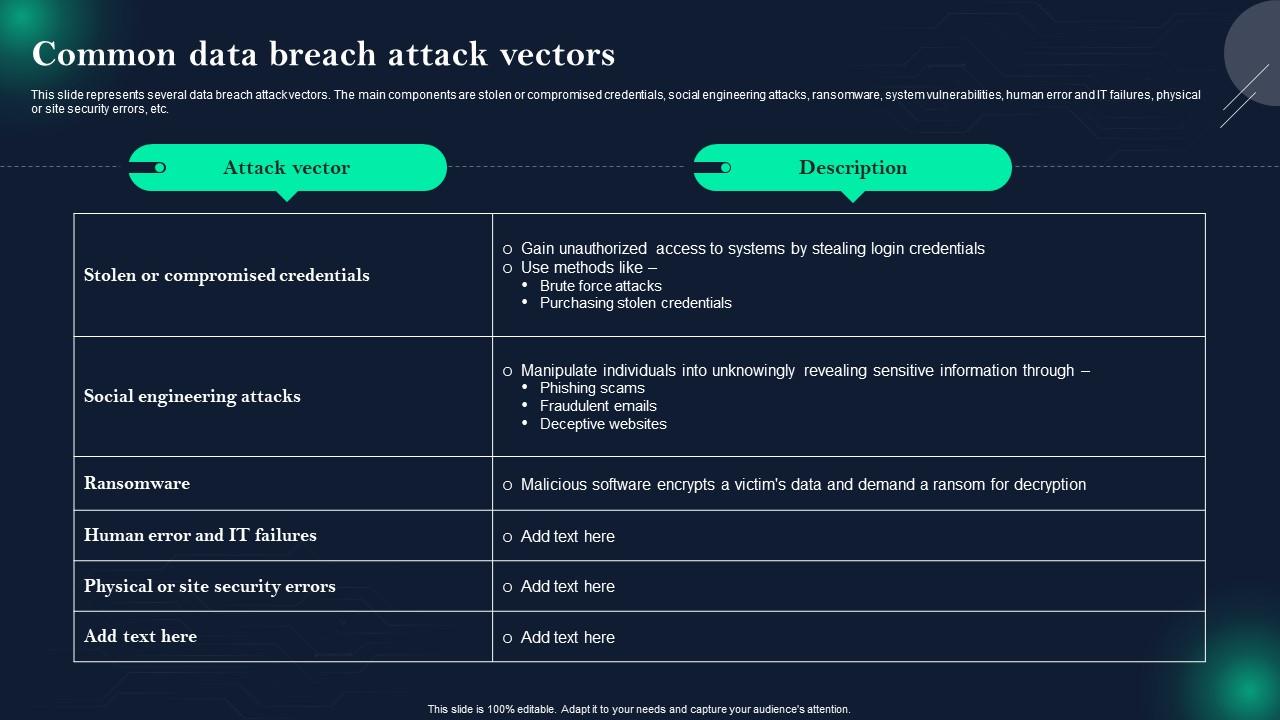
Data Breach Prevention And Mitigation Common Data Breach Attack Vectors In this blog, we delve into the different stages of the data breach lifecycle and explore effective strategies to mitigate risks and minimize potential damages. Once the attacker has established an access point within the system, the next step is to set up an external communication channel. this enables them to send instructions, receive stolen data, and operate within the compromised environment with full control.
Comments are closed.