Evaluation Of Threat Models

Evaluation Of Threat Modeling Methodologies Pdf Methodology While all threat model methods, maybe capable of identifying potential threat and the type of threats identified vary significantly. this paper consists of five threat model methods. While all threat model methods, maybe capable of identifying potential threat and the type of threats identified vary significantly. this paper consists of five threat model methods.
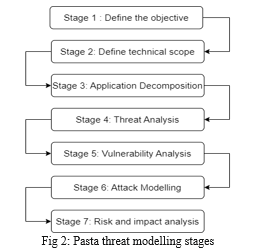
Evaluation Of Threat Models Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. Threat modelling is a structured method to identify, analyze, and mitigate potential threats in systems, applications, or organizations. it helps teams uncover vulnerabilities early and build security into the design before attackers exploit weaknesses. Threat modelling is essential for enhancing security and trust in information systems. common misconceptions include threat modelling being overly complex and a one time activity. five primary threat modelling methodologies exist: stride, octave, p.a.s.t.a., trike, and linddun. This paper presents an innovative approach to threat modeling specifically designed for security architects by integrating game theory principles with advanced risk assessment algorithms to.
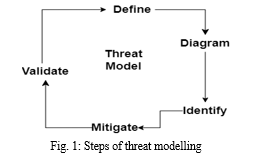
Evaluation Of Threat Models Threat modelling is essential for enhancing security and trust in information systems. common misconceptions include threat modelling being overly complex and a one time activity. five primary threat modelling methodologies exist: stride, octave, p.a.s.t.a., trike, and linddun. This paper presents an innovative approach to threat modeling specifically designed for security architects by integrating game theory principles with advanced risk assessment algorithms to. By systematically analyzing potential attack vectors and vulnerabilities, threat modeling helps in building robust defenses against sophisticated cyber attacks. This paper will present a comprehensive study concerning threat modelling including the phases involved in threat modelling, types of threat models and benefits and challenges of threat modelling. Model evaluation & threat research metr conducts research and evaluations to improve public understanding of the capabilities and risks of frontier ai systems. However, threat modeling is a domain that lacks common ground. what is threat modeling, and what is the state of the art work in this field? to answer these questions, this article presents a review of threat modeling based on systematic queries in four leading scientific databases.
Comments are closed.