Evaluating Encryption With The Nist Protect Framework Securitysenses

Nist Cybersecurity Framework Identify Protect Detect Respond Recover Pdf While it will never be possible to eliminate all data breaches, this paper shows how encryption technology can be used to minimise the loss of information and the resulting impact on the organisation. The following sections list the six nist categories in the “protect” framework function, examining commonly deployed technologies within each. for each technology we describe a common data breach scenario, then look at wider security concerns, focusing on data loss or theft.

Evaluating Encryption With The Nist Protect Framework Securitysenses These mappings are intended to demonstrate the relationship between existing nist publications and the cybersecurity framework. Learn how to enhance your cybersecurity with the protect function in nist csf 2.0. explore access control, data security, and tools like encryption to safeguard assets effectively. This section describes nist guidance for data protection controls and how tenable solutions help validate that appropriate encryption controls are implemented within the organization. This systematic review evaluates the adoption and effectiveness of the nist cybersecurity framework (csf) in mitigating cyber threats across diverse sectors.
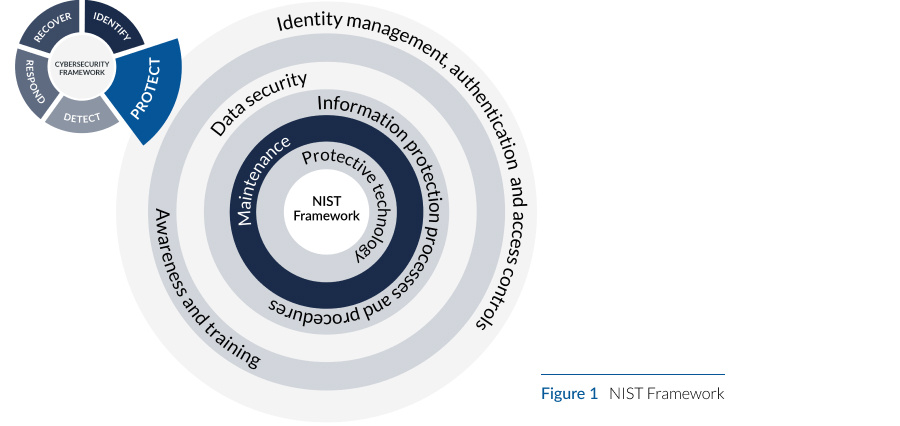
How File Encryption Can Improve Nist Framework Protect This section describes nist guidance for data protection controls and how tenable solutions help validate that appropriate encryption controls are implemented within the organization. This systematic review evaluates the adoption and effectiveness of the nist cybersecurity framework (csf) in mitigating cyber threats across diverse sectors. This guide dives into the nist compliance checklist, explores key standards like nist 800 53 and nist 800 171, and offers a practical road map to help you meet these requirements. Learn the core requirements of nist csf 2.0, why they matter, and how they help organizations strengthen cybersecurity posture and risk management. Abstract—this systematic review evaluates the adoption and effectiveness of the nist cybersecurity framework (csf) in mitigating cyber threats across diverse sectors. The framework is organized by five key functions– identify, protect, detect, respond, recover. these five widely understood terms, when considered together, provide a comprehensive view of the lifecycle for managing cybersecurity risk over time.
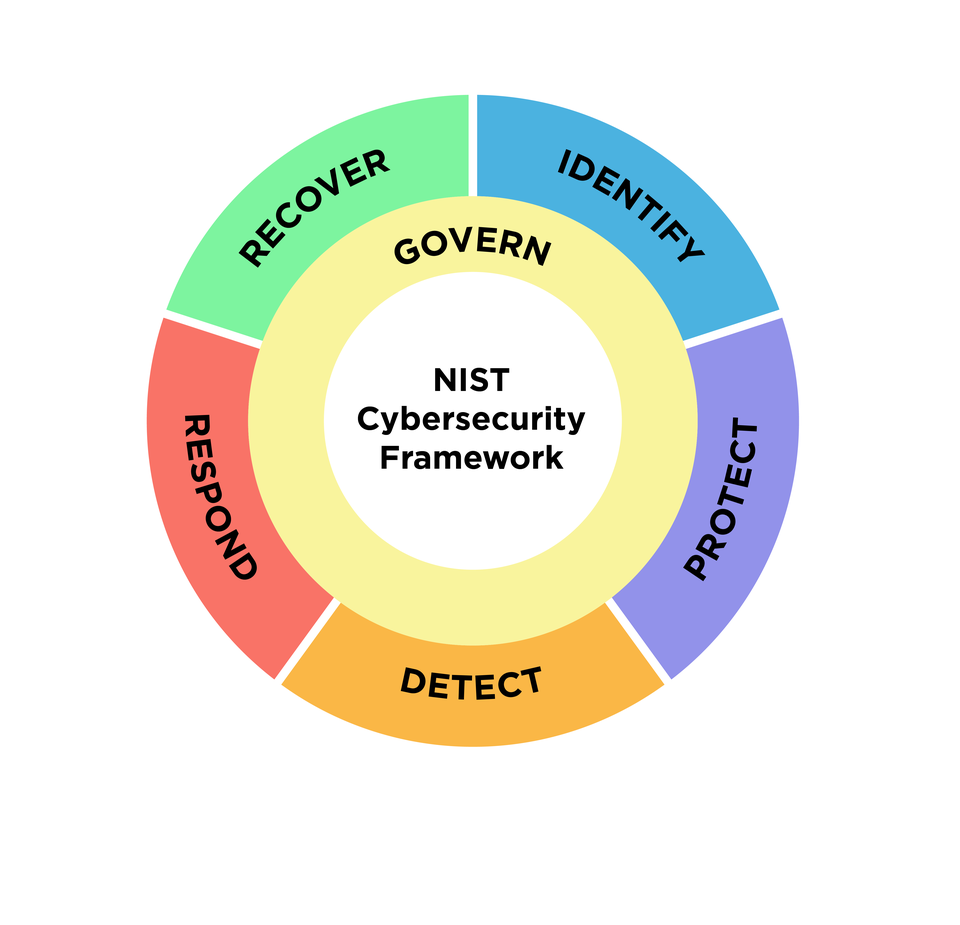
Nist Cybersecurity Framework 2 0 Draft This guide dives into the nist compliance checklist, explores key standards like nist 800 53 and nist 800 171, and offers a practical road map to help you meet these requirements. Learn the core requirements of nist csf 2.0, why they matter, and how they help organizations strengthen cybersecurity posture and risk management. Abstract—this systematic review evaluates the adoption and effectiveness of the nist cybersecurity framework (csf) in mitigating cyber threats across diverse sectors. The framework is organized by five key functions– identify, protect, detect, respond, recover. these five widely understood terms, when considered together, provide a comprehensive view of the lifecycle for managing cybersecurity risk over time.

Nist Cybersecurity Framework Protect 11 11 Innovation Blog Abstract—this systematic review evaluates the adoption and effectiveness of the nist cybersecurity framework (csf) in mitigating cyber threats across diverse sectors. The framework is organized by five key functions– identify, protect, detect, respond, recover. these five widely understood terms, when considered together, provide a comprehensive view of the lifecycle for managing cybersecurity risk over time.
Comments are closed.